All Articles
259 articles published
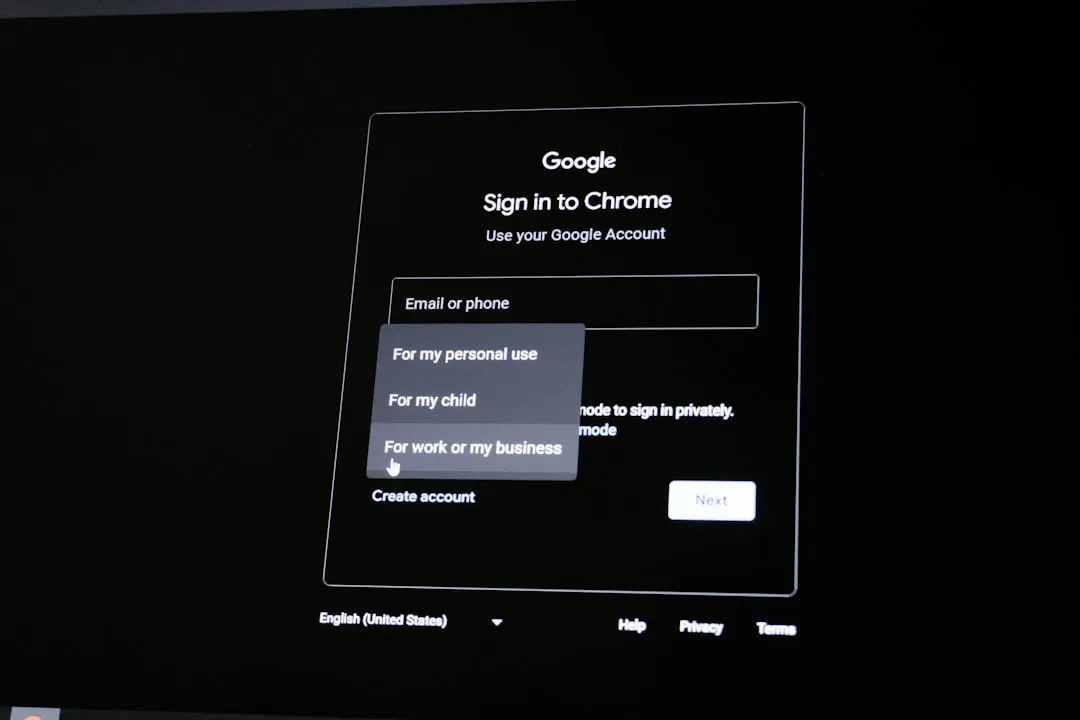
AI Browser Extensions Pose New Security Risks
Emerging threats in AI and browser extensions introduce new security risks, including shadow AI and unguarded extension vulnerabilities. Organizations must be aware of these threats and consider strategies to mitigate their impact. Stolen credentials can turn authentication systems into an attack surface.

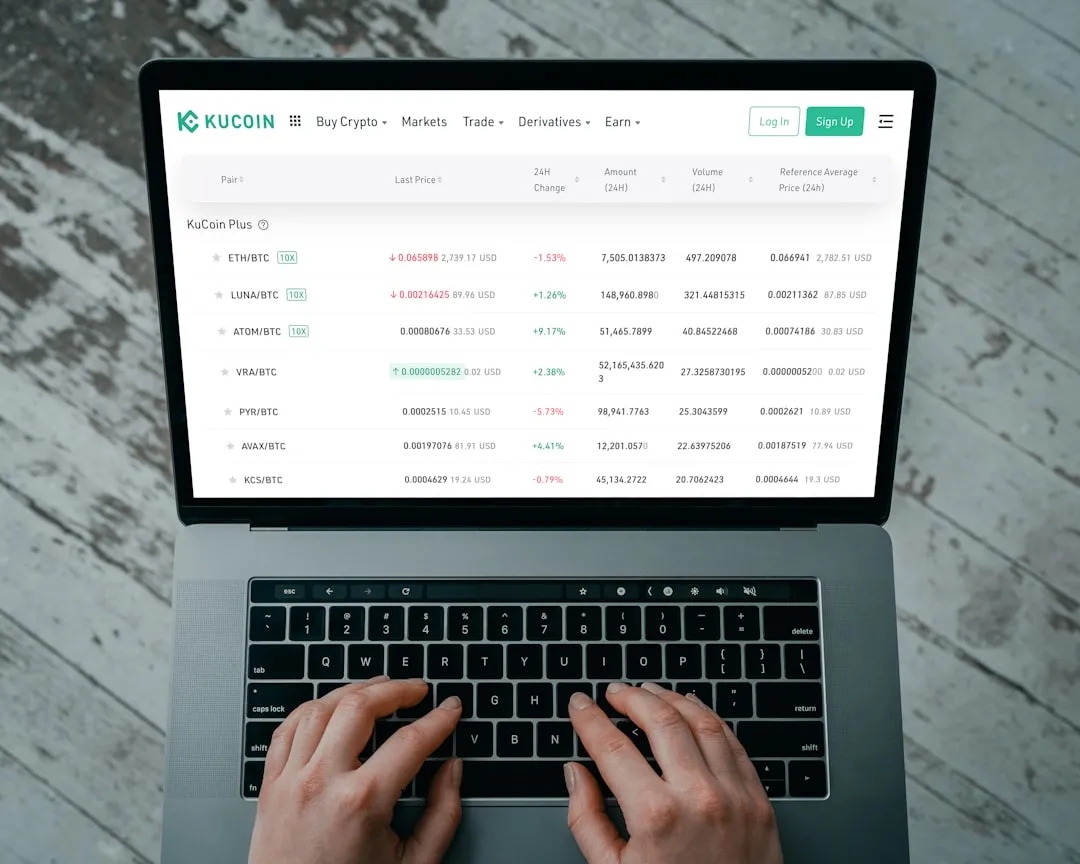
Global Crypto Fraud Crackdown
An international law enforcement operation has identified over 20,000 victims of cryptocurrency fraud, highlighting the global nature of crypto crimes. The crackdown involves cooperation across Canada, the UK, and the US. Learn about the key facts and takeaways from this operation.

Rockstar Games Hacked
Rockstar Games faces a critical hack with threats of a massive data leak. The incident highlights growing ransomware attacks on major corporations, potentially exposing sensitive game development materials and customer information.
High-Profile Targets Under Siege
Russia's Fancy Bear APT group, a new VENOM phishing platform, and suspected Indian government-backed threat actors are targeting high-profile individuals and organizations. These attacks highlight the importance of patching and implementing zero-trust security measures to protect against sophisticated threats.
Credential-Based Attacks Intensify
Stolen credentials are turning authentication systems into attack surfaces, with wearable biometric authentication emerging as a potential solution. A new Rust-based security scanner promises speed and efficiency in detecting threats.

Critical Infrastructure Under Siege
Targeted attacks on critical infrastructure are escalating, with Juniper Networks patching dozens of vulnerabilities and Russia's APT28 spying on global organizations. Learn about the key threats and how to protect your systems.
Cybersecurity Initiatives Advance
Cloudflare aims for post-quantum security by 2029, while Pluralsight launches SecureReady to address the cybersecurity skills gap. Learn about these initiatives and their impact on the industry.
Emerging Botnets Target IoT and Cloud
New botnets like Masjesu and Chaos malware variants are targeting IoT devices and misconfigured cloud deployments, posing significant threats to global cybersecurity. These emerging threats highlight the evolving landscape of cyber attacks and the need for continued vigilance.

GlassWorm Campaign Evolves with Zig Dropper
The GlassWorm campaign has introduced a new Zig dropper to infect developer IDEs, while Russian submarine activity near undersea cables and a Windows zero-day vulnerability pose significant threats. Learn about these emerging threats and how to protect against them.
LucidRook Malware Targets Taiwan NGOs
A new Lua-based malware, LucidRook, is targeting NGOs and universities in Taiwan. Meanwhile, Russia's Fancy Bear APT continues its global attacks, highlighting the need for patching and zero-trust security measures.
Marimo & Chrome Under Attack
Critical vulnerabilities in Marimo and Chrome pose significant risks to users, with exploits already reported in the wild. Learn about the technical details and implications of these threats.

Nation-State Cyber Attacks Surge
Russia's APT28 and Iranian hackers launch targeted cyber attacks on global organizations, US energy, and water sectors. Learn about the threats and how to protect yourself.
Notable Security Incidents and Research
Recent security incidents include Cloudflare's post-quantum security roadmap, zero-day exploits for the human mind, and backdoored updates for WordPress and Joomla plugins. These threats highlight the need for long-term cryptographic planning and awareness of social engineering tactics.

Ransomware Hits Healthcare
A recent ransomware attack on Dutch healthcare software vendor ChipSoft highlights the vulnerability of healthcare organizations to such attacks, which can have significant consequences for patient care. This article explores the key facts and implications of this threat. Ransomware attacks are a growing concern for healthcare.

Supply Chain Under Siege
Recent supply chain attacks have compromised CPUID's API, exposed Eurail customer data, and stolen millions from Bitcoin Depot. Learn about these high-severity breaches and how to protect yourself.
Targeted Attacks Hit Corporate Assets
Threat actors UNC6783 and APT28 launch targeted attacks on corporate assets, compromising business process outsourcing providers and deploying PRISMEX malware. High-value companies across multiple sectors are at risk, highlighting the need for robust security measures.

AI Security Risks Exposed
Recent attacks on Apple Intelligence and Grafana highlight the growing concern of AI-related security risks. Enterprises are deploying AI without fully understanding the risks, including model collapse and adversarial abuse. Learn how to secure your AI-powered systems.

Data Breaches Expose Sensitive Info, $3.6M Stolen
Recent data breaches have exposed sensitive information and resulted in significant financial losses, highlighting the need for robust cybersecurity measures. This article provides an overview of the latest threats and offers recommendations for protection.
Data Breaches Surge with SaaS Integrator and Eurail Attacks
Recent data breaches at a SaaS integrator and Eurail have exposed sensitive information for hundreds of thousands of individuals, highlighting the need for better security practices. Cyber fraud is also increasing in mobile-first regions.

Emerging Threats: Emoji-Based Attacks and Patched Vulnerabilities
Threat actors are using emojis to evade detection, while cybercriminals target accountants to drain Russian firms' bank accounts. Meanwhile, Palo Alto Networks and SonicWall have patched high-severity vulnerabilities. Learn about these emerging threats and how to protect yourself.
North Korea Spreads Malicious Packages
North Korean hackers have spread over 1,700 malicious packages across npm, PyPI, Go, and Rust ecosystems, targeting developer tooling and extending the Contagious Interview campaign. This attack highlights the evolving nature of supply chain threats and potential vulnerabilities in the Go, Rust, and PHP ecosystems.
Zero-Day Exploits Hit Adobe Reader & WordPress
Critical zero-day vulnerabilities in Adobe Reader and WordPress are being actively exploited, posing significant risks to users and organizations. These exploits require immediate attention to prevent malicious attacks.
Zero-Day Threats Hit Adobe and WordPress
Critical zero-day vulnerabilities are being exploited in Adobe Reader and the Ninja Forms File Uploads premium add-on for WordPress, posing significant risks to various industries. These threats allow hackers to execute remote code and compromise systems using malicious PDF documents and arbitrary file uploads.
AI Reshapes Cybersecurity Amid RSAC Debates
RSAC 2026 highlights the growing role of AI in cybersecurity, with industry leaders debating its applications and challenges. Learn about the future of security operations and the need for better metrics.
CISA Orders Patch for Critical Flaw as Data Theft Attacks Hit
US government agencies face a critical deadline to patch an Ivanti EPMM flaw, while Snowflake customers suffer data theft attacks due to a SaaS integrator breach. Learn about the vulnerabilities and how to protect yourself.

Critical Infrastructure Under Siege
Targeted attacks on critical infrastructure and IoT devices are on the rise, with the US disrupting a Russian espionage operation involving hacked routers and DNS hijacking. Learn about the key threats and how to protect your organization.

Critical Flaws in Fortinet and Next.js Under Active Exploitation
Active exploitation of critical flaws in Fortinet and React2Shell, ransomware attacks on critical infrastructure, and significant crypto thefts highlight the urgent need for robust security measures. Read on to understand these threats and how to protect against them.

Iranian Hackers Target US Critical Infrastructure
Iranian threat actors are targeting US critical infrastructure, including water and wastewater systems and the energy sector, causing operational disruption and financial losses. The FBI and Pentagon have issued warnings about these threats. Readers should understand the scope of these attacks and take immediate action to protect their organizations.
WordPress & Grafana Under Attack
Hackers target Ninja Forms vulnerability to takeover WordPress sites, while GrafanaGhost attackers leak enterprise data through AI components. Learn how to protect your sites and data from these emerging threats.

Zero-Day Attacks Surge with Medusa Ransomware
A surge in zero-day exploitation is facilitating high-velocity Medusa ransomware attacks, while the Storm-1175 threat actor targets vulnerable systems. Thousands of zero-day flaws have been discovered across major systems, and a maximum-severity vulnerability in Flowise is being exploited for remote code execution.

Zero-Day Vulnerabilities Under Active Exploitation
Multiple zero-day vulnerabilities are being actively exploited, including a critical flaw in Ivanti Endpoint Manager Mobile and 13-year-old bugs in Apache ActiveMQ Classic and Flowise. These vulnerabilities pose significant risks to federal enterprises and other organizations.

AI-Driven Supply Chain Threats Escalate
Threat actors leverage AI for automated supply chain attacks, targeting GitHub misconfigurations and Node.js maintainers. Medusa ransomware campaigns exploit vulnerabilities at an alarming rate, highlighting the need for secure configuration practices.
AI Security Risks Surge in Healthcare
The increasing use of AI in healthcare poses significant security risks, including shadow AI. As AI becomes more prevalent, organizations must prioritize security protocols to mitigate potential threats. Bernie Sanders has expressed concerns about the threat of AI to American society.
Cyber Fraud Surges as Fortinet Releases Emergency Patch
A critical FortiClient EMS flaw is being exploited, and cyber fraud has surged to $17.6 billion in losses. Learn about the latest threats and how to protect yourself.

DDoS Attacks Disrupt Critical Infrastructure
A large-scale DDoS attack on Russian telecom giant Rostelecom has disrupted internet services across dozens of cities, highlighting the importance of robust security measures. Meanwhile, REvil leaders have been identified behind 130 German ransomware attacks, and emerging threats like LiteLLM are turning developer machines into credential vaults for attackers.

Docker Engine Vulnerability Exposed
A high-severity vulnerability in Docker Engine allows attackers to bypass authorization, posing a significant threat to container security. Update to the latest version to mitigate this risk. Learn more about the vulnerability and its implications.
GPU Rowhammer Attacks Enable Privilege Escalation
Researchers have demonstrated GPU Rowhammer attacks can escalate privileges, potentially allowing attackers to take full control of a host. Learn about GPUBreach, GDDRHammer, and GeForge attacks.
Industrialized Social Engineering on the Rise
Sophisticated social engineering attacks are becoming increasingly industrialized, posing significant threats to maintainers and users of popular packages. Recent high-profile hacks demonstrate the patience and sophistication of certain threat actors.
Iranian Hackers Target US Critical Infrastructure as Russia Steals Microsoft Tokens
Iranian-affiliated cyber actors are exploiting programmable logic controllers in US critical infrastructure, while Russian hackers steal Microsoft Office tokens via router exploitation. Mitsubishi Electric products also vulnerable to attacks.

Nation-State Cyber Attacks Target US Infrastructure
Iranian and Russian nation-state actors are launching targeted cyber attacks against US critical infrastructure, including energy and water facilities. These attacks exploit vulnerabilities in programmable logic controllers and compromise SOHO routers for DNS hijacking.

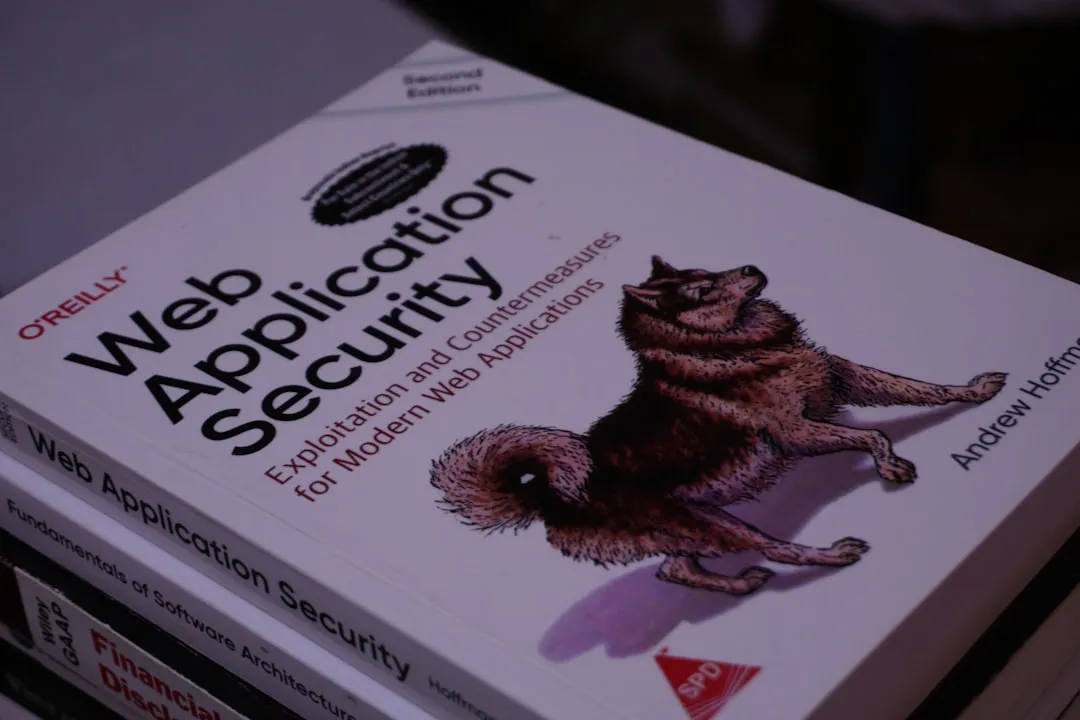
Pentesting Tools Hit a Wall as GenAI Risks Rise
Automated pentesting tools are struggling to keep up with modern attack surfaces, while generative AI risks and infostealers pose new threats. Learn how to defend against these emerging trends.
Ransomware Leaders Identified
German police have identified the alleged leaders of the GandCrab and REvil ransomware groups, marking a significant victory in the fight against cybercrime. This breakthrough may lead to further disruptions of ransomware operations and reduce the incidence of such attacks.

Storm-1175 Threat Actor Exploits Zero-Days
China-linked Storm-1175 threat actor exploits zero-day and N-day vulnerabilities to deploy Medusa ransomware, posing a significant threat to internet-facing systems. Organizations must ensure their systems are up-to-date and securely configured to mitigate potential attacks.

Cyberattack Hits German Party
A cyberattack on the German political party Die Linke has raised concerns about cybersecurity threats to organizations. Hackers have threatened to leak data, emphasizing the need for robust security measures.
Iran-Linked Threat Actor Targets Microsoft 365
An Iran-linked threat actor is suspected to be behind a password-spraying campaign targeting Microsoft 365 environments in Israel and the U.A.E. The campaign highlights ongoing cyber threats in the Middle East region, with attackers exploiting weak passwords or authentication mechanisms.

Medusa Ransomware Zero-Day Attacks
Medusa ransomware affiliate linked to zero-day attacks, posing a significant risk to organizations. Microsoft has identified Storm-1175 as the actor behind Medusa payloads, highlighting the need for timely vulnerability remediation and robust security measures.

Node.js Under Siege
North Korean hackers target Node.js maintainers with social engineering campaigns, exploiting Redis and PostgreSQL to deploy persistent implants. 36 malicious npm packages discovered, affecting thousands of projects.

Qilin and Warlock Ransomware Threats Escalate
Qilin and Warlock ransomware operations are using vulnerable drivers to disable over 300 EDR tools, posing a significant threat to cybersecurity. Learn about the emerging threats and techniques used by these ransomware groups.

23-Year Old Linux Vulnerability Discovered
A hidden Linux vulnerability was recently discovered after 23 years, highlighting the importance of continuous security research and testing. This finding underscores the potential for unknown vulnerabilities in widely used software and emphasizes the need for vigilant patch management.
Malicious npm Packages and Fortinet Vulnerability Exploited
Discover how malicious npm packages exploited Redis and PostgreSQL to deploy persistent implants, and learn about the critical Fortinet vulnerability patched in FortiClient EMS. Understand the risks of privilege escalation and unauthorized access.
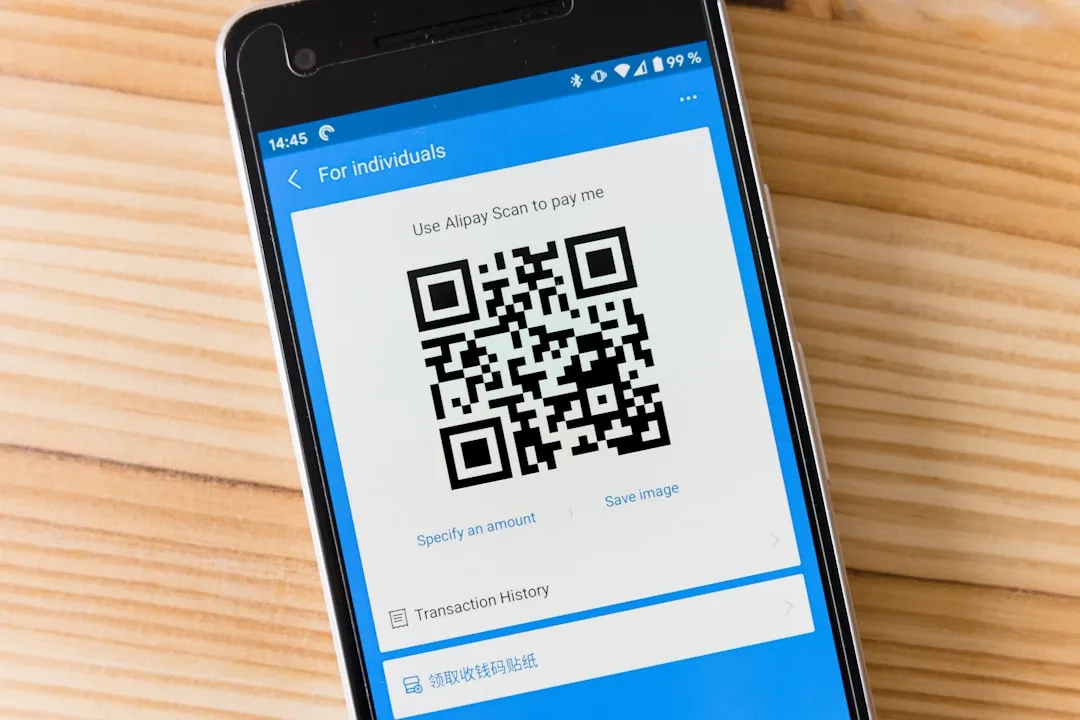
Phishing Attacks Surge with QR Codes and Device Code Abuse
A new wave of phishing attacks using QR codes and device code abuse is targeting users, stealing personal and financial information. Learn about the surge in these attacks and how to protect yourself.

Supply Chain Under Siege
A high-severity privilege escalation vulnerability in OpenClaw and the unveiling of Chainguard's Factory 2.0 platform highlight the importance of securing the software supply chain, as seen in The Claude source code leak. Learn about the key threats and takeaways to protect your organization.

Trivy Supply Chain Attack Hits EU Commission
The European Commission has confirmed a data breach linked to the Trivy supply chain attack, with over 300GB of sensitive data stolen. This incident highlights vulnerabilities in supply chain and video conferencing software, emphasizing the need for swift patching and robust security measures.
CVE-2025-55182 Exploited to Steal Sensitive Data
Cybersecurity experts warn of active exploitation of CVE-2025-55182, a critical vulnerability that can be used to steal sensitive data and gain unauthorized access to systems. This large-scale credential harvesting operation has affected 766 Next.js hosts, highlighting the need for prompt patching and security updates.
High-Profile Cyber Attacks Intensify
Recent cyber attacks on high-profile organizations like Hasbro and The Drift Protocol have resulted in significant financial losses and data breaches. These targeted attacks highlight the increasing threat of sophisticated operations and the need for robust cybersecurity measures.
LinkedIn Secretly Scans Browsers
LinkedIn has been secretly scanning visitors' browsers, raising concerns about data privacy and potential misuse. Over 6,000 Chrome extensions are affected, highlighting a significant scope of impacted users.
North Korean Cyberattacks Surge
North Korean threat actors are behind several high-profile cyberattacks, including the Axios npm hack and Drift's $285 million loss. Recent attacks showcase sophisticated social engineering tactics and swift financial gains. Understanding these threats is crucial for cybersecurity awareness.

Ransomware Attacks Escalate with Qilin and REF1695 Operations
Active ransomware and cyberattacks are on the rise, with Qilin and REF1695 operations targeting organizations worldwide. Critical infrastructure is at risk, including emergency communications systems. Learn about the key threats and how to protect yourself.

AI-Powered Cybersecurity Gains Momentum Amid Emerging Threats
Security leaders are adopting AI-powered solutions to enhance cybersecurity posture, as discussed at RSAC 2026. Apple's DarkSword exploit protection rollout highlights efforts to stay ahead of threats. Learn about the intersection of geopolitics, AI, and cybersecurity.

Critical Infrastructure Under Siege
Vulnerabilities in critical infrastructure pose significant risks, with ShareFile flaws and Hitachi Energy's Ellipse product under attack. Emerging threats like CrystalRAT malware and Casbaneiro bank trojan also threaten security. Learn about the key threats and how to protect yourself.
Cybersecurity Under Scrutiny
Vulnerability research faces re-evaluation due to potential flaws, while EmDash emerges as a secure WordPress alternative. Modern intrusions increasingly exploit valid credentials and routine access, highlighting the need for improved security measures.
Critical Cyberattacks Hit Mercor, Bitcoin
Mercor faces a cyberattack tied to the LiteLLM project compromise, while quantum computer researchers predict Bitcoin encryption can be broken in a few years. Ukraine also warns of Russian hackers revisiting past breaches.

EU Commission Hack Exposes Data
The European Commission's cloud infrastructure was hacked by TeamPCP, exposing data from at least 29 other EU entities. This incident highlights the significant risk of supply chain attacks and the need for robust access controls.
North Korean Hackers Steal $285 Million
North Korean hackers have stolen $285 million from the Solana-based decentralized exchange Drift in a durable nonce social engineering attack. This critical incident highlights the significant threat posed by North Korean hacking groups to cryptocurrency exchanges. Read on for key details and recommendations.

Supply Chain Risks Surge Amid Critical Vulnerabilities
Critical vulnerabilities in supply chain infrastructure pose significant threats to organizations. Recent discoveries highlight the need for robust security measures and timely patching.
Zero-Day Exploits Hit Mercor and TrueConf
Recent cyberattacks on Mercor and TrueConf highlight the active exploitation of zero-day vulnerabilities in targeted campaigns. Threat actors are using these exploits for reconnaissance, privilege escalation, and payload execution, posing significant risks to organizations. This article provides an overview of the threats and recommendations for mitigation.

Zero-Day Exploits Hit TrueConf Servers and Banking Systems
Hackers exploit zero-day vulnerability in TrueConf conference servers to push malicious updates, while a phishing campaign targets Latin America and Europe with Windows banking trojans like Casbaneiro. These attacks highlight the ongoing threat of zero-day exploits and social engineering.

Claude Code Leak Sparks Malware Fears
The recent Claude Code source code leak has led to the exploitation of a critical vulnerability, allowing threat actors to deliver Vidar information-stealing malware via fake GitHub repositories. This poses significant risks to users and highlights the importance of swift security reviews and patches.
Critical Vulnerabilities Under Active Exploitation
Active exploitation of critical vulnerabilities in FreeBSD and F5 BIG-IP APM instances poses a significant threat to systems. Over 14,000 F5 BIG-IP APM instances remain exposed to RCE attacks, while a full FreeBSD remote kernel RCE with root shell has been disclosed.

Drift Crypto Hack Exposes $280M, Supply Chains Under Siege
A critical hack of the Drift crypto platform has resulted in the theft of $280 million. Meanwhile, supply chain attacks and data breaches continue to pose significant threats to cybersecurity. Learn about these incidents and how to protect yourself.

New Malware Threats Emerge
A surge in new malware threats has been detected, including CrystalRAT, AGEWHEEZE, and AtlasCross RAT. These threats pose a significant risk to individuals and organizations, with capabilities such as remote access, data theft, and keylogging.

Ransomware & AI Threats Escalate
Hospitals face severe consequences from ransomware attacks, while Google's Vertex AI poses a security risk due to over-privileged agents. Attackers are increasingly using trusted tools against organizations, highlighting the need for vigilance and rehearsals in defense.

Ransomware Strikes Medtech Giant
Medtech giant Stryker suffered a data-wiping attack claimed by Iranian-linked Handala hacktivist group, highlighting risks to critical infrastructure. The company has since returned to full operation, but the incident underscores the severity of ransomware threats.
Supply Chain Attacks Expose Code
Recent supply chain attacks have led to the exposure of sensitive source code, emphasizing the need for secure software development and distribution practices. Anthropic's Claude Code and Axios npm package were compromised, with Google attributing the latter to a North Korean threat actor. Learn how to protect your organization from similar threats.

Supply Chain Attacks Hit Axios, Mercor, and Nissan
Recent supply chain attacks have targeted major companies like Axios, Mercor, and Nissan, resulting in data breaches and compromised systems. Learn about the key facts and takeaways from these incidents.

Vertex AI Vulnerability Exposes Google Cloud
A security flaw in Google Cloud's Vertex AI platform could allow AI agents to be weaponized for unauthorized access to sensitive data. Researchers demonstrated how attackers can exploit this vulnerability to steal data and break into restricted cloud infrastructure.

Vulnerability Research Integrity Under Fire
Concerns over vulnerability research integrity arise as Node.js Security Bug Bounty Program pauses, potentially impacting discovery and disclosure. New Progress ShareFile flaws enable pre-auth RCE attacks, highlighting patching needs.
Vulnerability Research Under Scrutiny Amid AI Breakthroughs and GIGABYTE Flaw
Concerns over vulnerability research validity emerge as AI deobfuscates JavaScript code, while GIGABYTE Control Center faces arbitrary file-write flaw. Understand the implications and necessary actions.

Crypto Exchange Hacks & Government Cyberattacks Surge
Cryptocurrency exchange hacks and cyberattacks on government networks are intensifying, with $53 million stolen from Uranium Finance and TrueConf zero-day exploits targeting Southeast Asian governments. Latin American governments face disruptive attacks and probes.

Cybercrime Hits Uranium Finance
A Maryland man was indicted for stealing $54 million from Uranium Finance in 2021, highlighting the ongoing threat of cyber-enabled financial crime. The incident involved hacking smart contracts and destroying a cryptocurrency exchange, showcasing the severity of cybercrime's impact on financial systems.
High-Severity Bugs Hit PX4 Autopilot, Vim, GNU Emacs
Multiple high-severity vulnerabilities have been disclosed in products like PX4 Autopilot, Vim, and GNU Emacs, affecting various systems including transportation and defense. These flaws could allow arbitrary code execution or other malicious activities. Affected vendors have released patches or recommendations to mitigate these vulnerabilities.
Iranian Threat Actors Escalate Attacks on US Organizations
Iranian threat actors are deploying 'pseudo-ransomware' and reviving Pay2Key operations to target high-impact US organizations, while also breaching the personal email of the FBI director. This escalation poses a significant threat to national security and highlights the need for increased vigilance.
AI-Driven Code Surge Redefines AppSec
The surge in AI-driven code is forcing a rethink of application security practices, with evolving threats and new vulnerabilities emerging. Learn how to evaluate AI SOC agents and adapt to the changing AppSec landscape.
Critical Flaws Exposed in Anritsu, Cisco, and Telegram
Multiple high-severity vulnerabilities have been discovered in Anritsu Remote Spectrum Monitor, Cisco source code, and a critical no-click flaw in Telegram. These threats pose significant risks to communications, defense, and emergency services. Understanding these vulnerabilities is crucial for proactive defense.

DeepLoad Malware & CareCloud Breach
A new AI-powered malware called 'DeepLoad' is evading detection, while a data breach at healthcare tech firm CareCloud exposed sensitive patient data. Learn about these emerging threats and how to protect yourself.

Emerging Threats Hit Asia
A previously undocumented remote access trojan named AtlasCross RAT is being used in an active campaign targeting Chinese-speaking users. Russian-origin CTRL toolkit and China-linked clusters are also on the rise, targeting Southeast Asian government organizations with various malware families.
Evaluating AI SOC Agents and Improving Tier 1 Productivity
Learn how to evaluate AI SOC agents effectively and improve Tier 1 productivity in security operations centers. Discover key questions to ask and process fixes to unlock efficiency.

FBI Director Hacked, Vulnerability Research Under Fire
The FBI Director's personal email was breached by Iran-linked hackers, highlighting the vulnerability of high-profile individuals. Meanwhile, concerns over compromised vulnerability research may impact trust in security reports and patches.

FreeBSD Forums Hacked Amidst Rising Security Concerns
The FreeBSD Forums were hacked, highlighting the need for robust security measures on online forums. This incident serves as a reminder to monitor and respond to security incidents. Learn more about this breach and its implications.

Google's Quantum Breakthrough Threatens Crypto
Google's quantum breakthrough significantly reduces the resources needed to break Bitcoin and Ethereum encryption, posing a major threat to cryptocurrency security. This development has profound implications for crypto platforms and the future of quantum computing.

Ransomware and Crypto Exchange Hacks Surge
A surge in ransomware claims and crypto exchange hacks poses a significant threat to cybersecurity. Over 7,655 ransomware claims were reported in the past year, while a hacker stole $53 million from the Uranium crypto exchange. Learn how to protect yourself from these threats.
Supply Chain Attacks Hit Axios and OpenAI
Recent supply chain attacks on Axios and a critical vulnerability in OpenAI Codex pose significant threats to software security. Learn about the malicious dependency in Axios and how it could compromise systems, as well as the potential for GitHub token compromise via OpenAI Codex.

CareCloud Probes Potential Healthcare Data Breach
A potential data breach at healthcare IT platform CareCloud may have leaked patient data, highlighting ongoing cybersecurity risks in the healthcare sector. The incident is under investigation and has been disclosed to the Securities and Exchange Commission. This article provides an overview of the situation and its implications.
Citrix & F5 Under Attack
Critical vulnerabilities in Citrix NetScaler and F5 BIG-IP are being exploited, allowing attackers to gain administrative access and deploy webshells. Organizations using these products must patch immediately to prevent attacks.

Critical Exploits Hit Fortinet & F5 BIG-IP
Organizations face significant threats as critical vulnerabilities in Fortinet's FortiClient EMS and F5 BIG-IP are being actively exploited, potentially leading to remote code execution or denial-of-service conditions. Immediate action is required to patch these flaws.

DeepLoad Malware Spreads with ClickFix
A new malware loader called DeepLoad has been discovered, using the ClickFix social engineering tactic to distribute itself and steal browser credentials. This high-severity threat utilizes AI-assisted obfuscation and WMI persistence, making it a significant concern for security professionals.

European Commission Hacked
The European Commission suffered a data breach after its Europa.eu web platform was hacked by the ShinyHunters extortion gang, highlighting ongoing cyber threats to government organizations. This incident underscores the need for robust cybersecurity measures in the public sector.

Italian Bank Fined $36M for Data Protection Failures
The Italian Data Protection Authority has fined Intesa Sanpaolo SpA $36 million for data protection failures, highlighting the importance of adequate technical and organizational measures to protect personal data. This incident emphasizes the need for robust security measures to prevent similar breaches.

Manufacturing and Healthcare Face Security Challenges
The manufacturing and healthcare sectors are struggling with security challenges related to access management and password security. Large Language Models can write complex code that dismantles least-privilege security models, emphasizing the need for robust security practices.

New Malicious Implants Emerge
A newly identified malicious implant named RoadK1ll enables threat actors to move quietly through networks, while a vulnerability in OpenAI's ChatGPT allowed sensitive data exfiltration. These findings highlight the ongoing efforts of threat actors to develop new tools and techniques.

Russian Court Cracks Down on Cybercrime
A Russian military court has sentenced 26 members of the cybercrime group Flint24 for large-scale payment card fraud, highlighting the importance of international cooperation in combating cybercrime. This significant law enforcement victory demonstrates the ongoing threat of organized cybercrime groups and potential vulnerabilities in financial transaction systems.

Telnyx Targeted in TeamPCP Supply Chain Attack
Telnyx faces a high-severity supply chain attack as malicious SDK versions are uploaded to PyPI, affecting Windows, macOS, and Linux. This incident highlights the importance of securing software supply chains.

Apple iOS Under Attack
Apple is sending Lock Screen notifications to outdated iPhones and iPads due to active web-based exploits, warning users of potential security risks. The Coruna iOS Exploit Kit has been identified as a likely update to Operation Triangulation, indicating evolving attack techniques.
Enlidea Emerges Amid Automated Research Boom
The development of Enlidea, a decentralized research hub, marks a significant shift in automated research and security. As companies like OpenAI aim to debut fully automated researchers, the implications for cybersecurity are profound. This article explores the emerging trends and technologies that may shape the future of security.

GitHub Malware Alert
A large-scale campaign is targeting developers on GitHub with fake Visual Studio Code (VS Code) security alerts, tricking users into downloading malware. This poses a significant risk to developer systems and projects, emphasizing the need for caution when interacting with VS Code alerts.
Google's Quantum-Safe Deadline Looms Amid Rising Threats
As Google sets a 2029 deadline for quantum-safe cryptography migration, OpenAI launches a bug bounty program to identify abuse and safety risks in its AI systems. Meanwhile, emerging threats from compromised IP cameras, AitM phishing pages, and malicious VS Code extensions pose significant security concerns.

Infinity Stealer Malware Targets macOS
A new info-stealing malware named Infinity Stealer is targeting macOS systems, using a Python payload and Nuitka compiler. This campaign highlights the growing threat of targeted attacks on macOS devices, emphasizing the need for increased security measures.

iOS Under Siege
A high-severity targeted email campaign is leveraging the DarkSword exploit kit to target iOS devices, attributed to Russian state-sponsored threat group TA446. Organizations must be aware of the potential for targeted attacks on their mobile devices and keep software up-to-date.

WordPress and Citrix NetScaler Vulnerabilities Under Active Exploitation
High-severity vulnerabilities in WordPress plugins and Citrix NetScaler are being actively exploited, putting over 500,000 websites and critical infrastructure at risk. Administrators must prioritize patching to prevent exploitation.

Automotive Cybersecurity Threats Rise
The cybersecurity of vehicles is under threat due to the rise of connected and autonomous vehicles, introducing new vulnerabilities. As technology advances in the automotive industry, the need for robust cybersecurity measures grows. Readers should be aware of the evolving threat landscape and take necessary precautions.

Bearlyfy's Custom Ransomware Hits Russian Firms
The Bearlyfy group has launched targeted ransomware attacks on over 70 Russian companies using custom GenieLocker ransomware, demonstrating increased sophistication in ransomware campaigns. These attacks aim to inflict maximum damage on Russian businesses, highlighting the need for enhanced cybersecurity measures.

Iran-Linked Hackers Breach FBI Director's Email
Iran-linked hackers have breached the personal email account of the FBI director, leaking sensitive documents. The attack demonstrates the increasing sophistication and brazenness of nation-state actors. Read on for key takeaways and recommendations.
Cybersecurity Evolves: RSAC 2026 and Quantum-Safe Future
The RSAC 2026 Conference brings new cybersecurity developments, including Google's 2029 deadline for quantum-safe cryptography. Organizations must prepare for the post-quantum future by assessing and updating their cryptographic infrastructure.

Telnyx PyPI Package Hacked
The Telnyx package on Python Package Index was compromised with malware, highlighting supply chain attack risks. Learn how to protect your systems and verify package integrity.

AI-Powered Phishing on the Rise
Emerging threats in cybersecurity include AI-powered phishing campaigns and new attack techniques from SANS Institute's top 5 most dangerous threats. These sophisticated attacks can evade traditional security controls, posing significant risks to individuals and organizations. Staying informed is crucial to mitigating these threats.

Critical Infrastructure Under Siege
A critical vulnerability in WAGO industrial switches threatens energy and transportation systems, while Google warns of quantum computers potentially hacking encrypted systems by 2029. Learn how to protect your organization from these emerging threats.

F5 BIG-IP Vulnerability and Emerging Threats
A newly disclosed vulnerability in F5 BIG-IP could allow remote code execution, while security research highlights various emerging threats. Learn about the key findings and how to protect your systems.

GitHub Boosts Code Security with AI
GitHub enhances its Code Security tool with AI-powered bug detection, expanding vulnerability coverage. Experts also call for a 'near-miss' database to improve cybersecurity information sharing.

High-Severity Patches and Cybercrime Arrests
Recent high-severity vulnerability patches and arrests highlight the ongoing battle against cybercrime. TP-Link router vulnerabilities have been patched, while the alleged developer of RedLine malware faces up to 30 years in prison. Stay informed on the latest cybersecurity threats.

Iran-Linked Hackers Target FBI Director
Rising geopolitical tensions are reflected in cyber operations, with an Iran-linked hacking group stealing the FBI director's personal emails. The incident highlights the increasing politicization of technology and its implications for global security.

Nation-State Malware Upgrades
Nation-state malware is evolving with China's APT Red Menshen upgrading its BPFdoor malware, and exploit kits like Coruna and DarkSword spreading on the Dark Web. Intermediaries are driving the global spyware market expansion, making it harder for organizations to defend themselves.
Phishing Attacks Surge with OAuth Abuse
Recent phishing campaigns have targeted Microsoft accounts, including a successful attack on the Dutch National Police. Threat actors are using Bubble AI app builder to evade detection and leveraging OAuth abuse techniques.

Security Breaches Hit EU Commission & Telnyx
The European Commission is investigating a breach after a threat actor gained access to their Amazon cloud environment, while TeamPCP has compromised the telnyx Python package. These incidents highlight the ongoing risk of security breaches and data theft.

Vulnerability Patches and Age Verification
Cisco patches multiple vulnerabilities in IOS software, while Apple rolls out age verification to UK iPhone users. Learn about the importance of cybersecurity best practices and how to protect your devices.

Ransomware Disrupts Spanish Port as Experts Urge AI-Driven Security
A ransomware attack has disrupted operations at a major Spanish fishing port, highlighting the need for AI-native security tools to combat AI-based attacks. Experts emphasize that defenders must use AI-driven security to counter these threats. Learn about the recent attack and the importance of AI-driven security in this article.

Chinese Hackers Target Telecom Infrastructure
Chinese state-sponsored hackers are targeting telecom infrastructure with kernel implants and passive backdoors, enabling long-term espionage with significant national security implications. This attack highlights the ongoing threat of Chinese hacking groups to critical infrastructure.

Coruna iOS Kit & GitHub Trojan Attacks
The Coruna iOS exploit kit and a malicious GitHub repository are putting devices at risk. Learn about these threats, the RedLine infostealer malware administrator's extradition, and how to protect yourself.
High-Severity Exploits and Cybercrime Takedowns
Multiple high-severity exploits have been discovered, including an Aquasecurity Trivy vulnerability. Meanwhile, cybercrime forums are being taken down and underground markets are selling paid AI accounts. Learn about the latest threats and how to protect yourself.

Malware Campaigns Target Crypto & Browser Data
Active malware and ransomware campaigns are targeting cryptocurrency and browser data, with threats like GlassWorm using Solana dead drops. Learn about the latest attacks and how to protect yourself.

Patched Router Flaws and Exposure Management
TP-Link patches critical router flaws, while Onit Security raises funds for its exposure management platform. Learn about the latest security research findings and how to protect your organization from potential threats.

Regulatory Crackdown on Cybercrime Amidst Rising Supply Chain Threats
Recent regulatory actions and law enforcement efforts target cybercrime, while supply chain attacks pose significant threats to code security. Learn about the latest developments and takeaways.

Russian Cybercriminal Sentenced to Prison for Ransomware Attacks
A Russian national has been sentenced to two years in prison for managing a botnet used in ransomware attacks against US companies. This sentencing highlights ongoing efforts to combat cybercrime and ransomware attacks. Learn more about the threat and how to protect yourself.
TikTok Phishing & Ajax Hack Expose Social Engineering Risks
A new TikTok phishing campaign and the Ajax football club hack highlight social engineering threats, while a critical PTC Windchill vulnerability requires immediate patching. Learn about these risks and how to protect yourself.

Torg Grabber & Supply Chain Attacks Hit Crypto and Open-Source
A new wave of cyber threats is targeting cryptocurrency users and open-source software, with Torg Grabber infostealer malware and supply chain attacks on PyPI and Docker Hub. Learn how to protect yourself from these emerging threats.
Ubuntu Boosts Security
Ubuntu plans to enhance security by stripping some GRUB features in the upcoming 26.10 release, aiming to improve secure boot mechanisms and reduce vulnerabilities. This development reflects ongoing efforts to improve Linux security. Readers should monitor future updates for potential impacts on their systems.
Zero-Day Exploits and Cybercrime Takedowns
Critical zero-day vulnerabilities in iOS and Chrome are being exploited, while cybercrime forums are being taken down. Learn about the latest threats and how to protect yourself.
CISA Orders Patching of Actively Exploited n8n Vulnerability
CISA has ordered federal agencies to patch the actively exploited n8n vulnerability, indicating a significant threat to government systems. The vulnerability allows for remote code execution, making it a high-priority patch for affected systems. Prompt patching is essential to prevent exploitation and protect against potential attacks.

Supply Chain Attacks Surge
A wave of supply chain attacks is targeting developer tools and packages, putting thousands of projects at risk. Learn about the latest threats and how to protect your projects.

Critical Data Breaches Hit Stryker and Telus Digital
Iranian hacktivists have struck medical device maker Stryker, while a hacker claims to have stolen nearly 1 petabyte of data from Telus Digital, highlighting the need for robust cybersecurity measures and incident response plans.
Critical n8n Flaws, KadNap Botnet, and Android Malware Threats
Today's threat landscape includes critical n8n workflow automation flaws, the KadNap botnet infecting edge devices, and new Android malware families targeting banking apps. These threats pose significant risks to security and require immediate attention.

Cybercrime and Law Enforcement Under Spotlight
The Cyber National Mission Force is getting a new commander amid broader leadership turnover. Meanwhile, Poland foiled a cyberattack on a nuclear center that may have originated from Iran, and US law enforcement agencies disrupted the SocksEscort cybercrime proxy network powered by Linux malware.

HPE Aruba Networking AOS-CX Vulnerabilities Patched
HPE has patched multiple security vulnerabilities in the Aruba Networking AOS-CX operating system, including authentication and code execution issues. Users should apply the patches to prevent potential exploitation. No known active exploitation has been reported.
Iran-Linked Wiper Malware Hits Medtech Firm Stryker
A critical Iran-linked wiper malware attack on medtech firm Stryker has raised concerns about nation-state actors targeting critical infrastructure. Meanwhile, new malware campaigns, including Slopoly and VENON, are evolving the threat landscape. Learn about these emerging threats and how to protect your organization.

Critical Patches Released for iOS and Windows
Apple and Microsoft have released critical security patches to prevent exploitation of known vulnerabilities. Users are advised to update their software immediately to protect against potential attacks.
Critical n8n and KadNap Exploits, Ransomware Surge
Active exploitation of n8n and KadNap malware poses critical threats, while ransomware attacks target healthcare organizations and critical infrastructure. Stay informed on the latest cybersecurity threats and take action to protect your systems.

Critical Supply Chain Attacks Hit Veeam and Cloud Environments
Supply chain attacks and data breaches are on the rise, with Veeam Software patching critical flaws in its Backup & Replication solution and a threat actor breaching a cloud environment in 72 hours. Learn about the key threats and how to protect your organization.

AI-Powered Security Solutions Gain Momentum
Jazz and Kai secure funding for AI-powered data loss prevention and IT-OT security, while OpenAI's Codex finds hundreds of critical vulnerabilities. Learn about the emerging threats and funding in AI-powered security solutions.
Cloud Resilience Under Fire
The Middle East conflict exposes significant cloud resilience gaps, while major vendors release critical ICS patches. Learn how to protect your infrastructure from emerging threats.

Cloud Vulnerabilities Under Siege
Hackers are exploiting cloud and software vulnerabilities at an alarming rate, with high-value organizations in Asia being targeted. Malicious code and phishing campaigns are also on the rise, highlighting the need for rapid patching and vigilance. Adobe has patched 80 vulnerabilities across eight products, and cybercriminals are impersonating city officials to steal permit payments.

Critical Data Breaches and AI-Powered Cybersecurity
Multiple critical data breaches have exposed sensitive information, while AI-powered cybersecurity solutions are being developed to combat these threats. Learn about the latest breaches and advancements in cybersecurity research and funding.

Critical Infrastructure Under Siege
Critical infrastructure faces significant threats from vulnerabilities, ransomware, and nation-state attacks. Recent discoveries include Honeywell IQ4x BMS Controller and Apeman Cameras vulnerabilities, as well as new malware and threat actor activity. Learn how to protect your systems.

Insider Threats Expose Sensitive Data
A recent incident involving a DOGE employee stealing Social Security data highlights the risks of insider threats. Organizations must implement strict access controls to prevent such breaches, which can lead to financial and reputational damage.

Reducing Attack Surfaces
Learn how to minimize the risk of zero-day exploits by managing internet-facing exposure. Effective attack surface reduction is crucial as time-to-exploit shrinks. Prioritize proactive security measures to protect your environment.

AI Assistants Redefine Security Risks
The increasing use of AI assistants among developers and IT workers introduces new security risks and challenges. As AI assistants become more widespread, security professionals must reassess their security priorities and consider the potential risks associated with these tools. This article explores the implications of AI assistants on organizational security and provides recommendations for mitigating these risks.
Critical Infrastructure Under Siege
Critical infrastructure faces multiple threats, including vulnerabilities in industrial control systems, the KadNap malware targeting routers, and emerging AI-powered attacks. Organizations must prioritize patching, securing networks, and implementing robust cybersecurity strategies to protect against these threats.
Google Looker Studio Vulnerabilities Exposed
High-severity vulnerabilities in Google Looker Studio and malicious Chrome extensions pose significant threats, while evolving malware and new security platforms highlight the cat-and-mouse game in cybersecurity. Learn about the latest developments and how to protect yourself.

Critical Ivanti Flaw Exploited, APT28 Espionage Campaign Uncovered
A critical flaw in Ivanti Endpoint Manager is being actively exploited, while APT28's customized Covenant malware is used for long-term espionage. Learn about the threats and how to protect yourself.

Phishing Attacks Surge
Russian state-sponsored hackers are targeting government officials and journalists with Signal and WhatsApp phishing campaigns, while threat actors abuse .arpa DNS and IPv6 to evade defenses. Financial and healthcare organizations are also being targeted with Microsoft Teams phishing and A0Backdoor malware.

US Shifts Cyber Strategy to Offense
The White House has released a new cyber strategy document prioritizing offense and preemption. This shift may impact cybersecurity professionals and organizations. Learn about the implications and recommendations.
CISA Adds Three New Vulnerabilities to KEV Catalog
CISA has added three new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, posing significant risks to the federal enterprise. The vulnerabilities include flaws in Omnissa Workspace, SolarWinds Web Help Desk, and Ivanti Endpoint Manager. Organizations should prioritize remediation to protect against active threats.

ClickFix Ransomware and Russian Cyber Campaigns
ClickFix attack and Termite ransomware pose high severity threats, while Russian cyber campaigns target Signal and WhatsApp. Emerging threats include abuse of internet infrastructure and custom malware. Stay informed to protect against these evolving cyber threats.
Critical Infrastructure Under Siege
A Chinese threat actor is targeting critical infrastructure in Asia, exploiting web servers and using Mimikatz. The campaign has targeted multiple sectors, including aviation, energy, and government, highlighting the need for increased security measures.

Phishing Attacks Surge with New Tactics
Phishing attacks are on the rise with new tactics, including abusing .arpa DNS and IPv6 reverse DNS. Data breaches and cybersecurity strategy updates are also in focus. Learn about the latest threats and how to protect yourself.

Critical Threats: UNC4899, Cisco Vulnerability, and Phishing Attacks
The cybersecurity landscape is threatened by active exploitation of vulnerabilities, phishing and social engineering attacks, and data breaches. UNC4899 is suspected to be behind a sophisticated cloud compromise campaign, while a recent Cisco Catalyst SD-WAN vulnerability is being widely exploited. Phishing attacks impersonating US city and county officials are also on the rise.

AI-Driven Cyber Threats Escalate
Microsoft reports hackers are abusing AI in cyberattacks, while OpenAI's Codex Security and Anthropic's AI model identify thousands of vulnerabilities. Learn how AI is changing the cybersecurity landscape and what you can do to protect yourself.

Cognizant TriZetto Breach Exposes 3.4M Patient Records
A critical data breach at Cognizant TriZetto has exposed sensitive health information of 3.4 million patients, highlighting vulnerabilities in healthcare data security. This incident underscores the need for robust security measures to protect patient privacy. Read on for key details and recommendations.

Hackers Abuse .arpa Domain and IPv6 to Evade Phishing Defenses
Threat actors are using the .arpa domain and IPv6 reverse DNS to bypass traditional security controls in phishing campaigns. This new evasion technique poses a significant threat to organizations, highlighting the need for improved defenses. Learn how to protect your organization from these sophisticated attacks.

MyFirst Kids Watch Hacked Amidst Rising Cyber Threats
The MyFirst Kids Watch has been hacked, allowing access to its camera and microphone. This incident is part of a larger landscape of cyber threats, including fake Claude Code install guides, Iran's cyber-kinetic war doctrine, and vulnerabilities in Rockwell industrial control systems. These threats underscore the importance of cybersecurity in protecting sensitive information and physical assets.

Cybercrime Surges with $46M Crypto Heist and Phishing-as-a-Service Takedown
A recent surge in cybercrime includes a $46 million cryptocurrency heist and the takedown of a phishing-as-a-service operation. Learn about the latest threats and how to protect yourself.

Nation-State Actors Unleash New Malware Campaigns
Nation-state actors are launching sophisticated malware campaigns, including the ClickFix social engineering campaign and attacks on Iraqi officials. These threats highlight the evolving landscape of cyberattacks and the need for heightened security measures.

State-Sponsored Threats and Vulnerabilities Plague Cybersecurity
State-sponsored threat actors and vulnerabilities pose significant risks to cybersecurity. Chinese state hackers target telcos, while vulnerabilities in Avira antivirus and WordPress plugins are exploited. Learn about the key threats and how to protect yourself.

Critical Infrastructure Under Siege
Targeted attacks on critical infrastructure are on the rise, with a China-linked APT group targeting telecommunication service providers and a Russian ransomware operator pleading guilty in the US. These attacks highlight the need for robust security measures and international cooperation.

Zero-Day Exploits Target iOS and GitHub Users
Critical zero-day vulnerabilities are being actively exploited, targeting iOS users and GitHub repositories. Over 100 GitHub repositories are distributing the BoryptGrab stealer, while CISA has added iOS flaws from the Coruna exploit kit to the KEV list. Users must take immediate action to protect themselves.

AI-Driven Threats Intensify Nation-State Attacks
Nation-state actors are leveraging AI-powered tools to launch sophisticated cyberattacks, targeting governments and organizations worldwide. Recent campaigns by Transparent Tribe and Iranian APT hackers demonstrate the growing threat of AI-driven attacks. Stay informed on the latest threats and learn how to protect your organization.

Critical Cloud and Networking Vulnerabilities Under Active Exploitation
Multiple critical vulnerabilities in cloud and networking products are being actively exploited, putting organizations at risk. VMware Aria Operations and Cisco SD-WAN products are among those affected, with patches available for some but not all vulnerabilities. Administrators must take immediate action to protect their networks.

Ghanaian National Pleads Guilty in $100M Fraud Ring
A Ghanaian national has pleaded guilty to his role in a $100 million fraud ring that targeted victims across the US. The ring used business email compromise attacks and romance scams. Learn how to protect your organization from similar threats.

Multiple Product Vulnerabilities Expose Users to Attacks
Recent security incidents and vulnerabilities in Hikvision, Rockwell, and Apple products, as well as a self-propagating JavaScript worm on Wikipedia, pose significant threats to users. These vulnerabilities could allow attackers to escalate privileges, gain access to sensitive information, and execute arbitrary code. It is essential for users to stay informed and take necessary precautions to protect themselves.

Phishing and Cybercrime Surge
A recent surge in phishing and cybercrime activities has highlighted the vulnerability of IoT devices and the importance of robust security measures. The hacking of the MyFirst Kids Watch and the bust of the Tycoon 2FA phishing platform underscore the need for increased vigilance. Read on to learn more about these threats and how to protect yourself.

Zero-Day Vulnerabilities and AI-Powered Threats
Critical zero-day vulnerabilities in FreeScout and VMware Aria Operations, along with AI-powered malware and info-stealing threats, pose significant risks to organizations. Immediate action is required to patch and mitigate these threats.

Coruna iOS Exploit Kit Under Active Exploitation
The Coruna iOS exploit kit is being actively exploited, targeting iOS devices with 23 exploits across five chains. Originally used by nation-state actors, it now appears in broader criminal campaigns. Learn how to protect your devices.
Phishing Operations Takedown and Cybercrime Syndicates Disrupted
Law enforcement agencies and threat hunters have made significant strides in disrupting major phishing operations and cybercrime syndicates, resulting in the takedown of Tycoon 2FA and LeakBase forum. These efforts highlight the importance of collaboration in combating cybercrime. Read on to learn more about these successes and their impact on the threat landscape.

Phishing Sites Slip Past Google Safe Browsing
Recent reports reveal Google Safe Browsing misses 84% of confirmed phishing sites, while the 2026 Browser Data report exposes major enterprise security blind spots. These findings highlight the need for improved detection capabilities and ongoing security research to combat emerging threats.
Ransomware Takedowns and Critical Infrastructure Threats Escalate
Law enforcement actions against ransomware operations and stolen credential marketplaces show progress, but targeted attacks on critical infrastructure and emerging threats pose significant risks. Organizations must stay vigilant and adapt their security strategies to combat these evolving threats.

Zero-Days and Cybercrime: Emerging Threats
A possible US government iPhone-hacking toolkit has been leaked, while half of 2025's exploited zero-days targeted enterprises. Meanwhile, law enforcement efforts have led to the dismantling of a major phishing platform and the breakup of an African cybercrime syndicate.
AI and Encryption Under Siege
TikTok's refusal to introduce end-to-end encryption and the JVG algorithm's potential to break RSA-2048 encryption pose significant threats to user data and online security. A new RFP template for AI usage control and governance offers a glimmer of hope. Learn how to navigate these challenges.

AI-Powered Attacks Surge
The emergence of AI-powered attack tools poses a significant threat to cybersecurity. Recent breaches, including the compromise of Fortinet FortiGate firewalls, highlight the dangers of these advanced attacks. Learn how to adapt your defenses against this new frontier in cybersecurity threats.
Cisco Firewall Vulnerabilities and Leakbase Takedown
Cisco has released patches for high-severity vulnerabilities in its Secure Firewall Management Center, while the FBI and European law enforcement agencies have taken down the Leakbase cybercrime forum. Learn about the key threats and recommendations for protection.
Hacktivist Surge and Cybercrime Disruption
A surge in hacktivist and nation-state attacks has hit organizations worldwide, while law enforcement actions disrupt major phishing and cybercrime platforms. Learn about the key threats and how to protect yourself.

Silver Dragon Targets Governments
An advanced persistent threat group known as Silver Dragon has been linked to cyber attacks targeting entities in Europe and Southeast Asia. The group's tactics include exploiting public-facing internet servers and delivering phishing emails with malicious attachments. Organizations must prioritize security to stay informed about emerging threats.
VMware Aria Operations RCE Flaw Under Active Exploitation
A critical VMware Aria Operations vulnerability is being exploited in attacks, allowing for remote code execution. This poses a significant threat to affected systems, and immediate action is required to patch the flaw. The US Cybersecurity and Infrastructure Security Agency has added the vulnerability to its Known Exploited Vulnerabilities catalog.
Android Zero-Day Under Attack
A critical zero-day vulnerability in Android's Qualcomm component is being exploited, while Israel and Iran engage in a cyber conflict. Learn about the threats and how to protect yourself.

Critical Threats: AWS Drone Strikes, Ransomware, and Zero-Days
AWS data centers face drone strikes, major ransomware attacks hit healthcare and gaming, and zero-day vulnerabilities are exploited in the wild. Stay ahead of these critical threats with our latest analysis.

New Surveillance Threats Emerge
Researchers uncover methods to track cars via tire sensors, while Microsoft warns of OAuth redirect abuse and a new attack hijacks OpenClaw instances. These emerging threats highlight the need for increased security measures.

Iranian Cyberattacks Disrupt Cloud Services Amidst Rising Phishing Threats
Iranian cyberattacks have hit Amazon data centers, disrupting cloud services. Meanwhile, phishing campaigns and emerging threats like quantum decryption of RSA pose significant risks. Learn about the latest cybersecurity threats and how to protect yourself.

Major Data Breaches Hit LexisNexis and University of Hawaii
Two significant data breaches have been confirmed, affecting millions. Learn about the impacts on LexisNexis and the University of Hawaii Cancer Center, including sensitive information compromised.

Nation-State Cyberattacks Escalate Amid Global Crackdown
Nation-states are escalating their cyberattacks, with Israel and the US targeting Iran's infrastructure. Meanwhile, a global crackdown on cybercrime has led to the arrest of alleged members of 'The Com' collective.
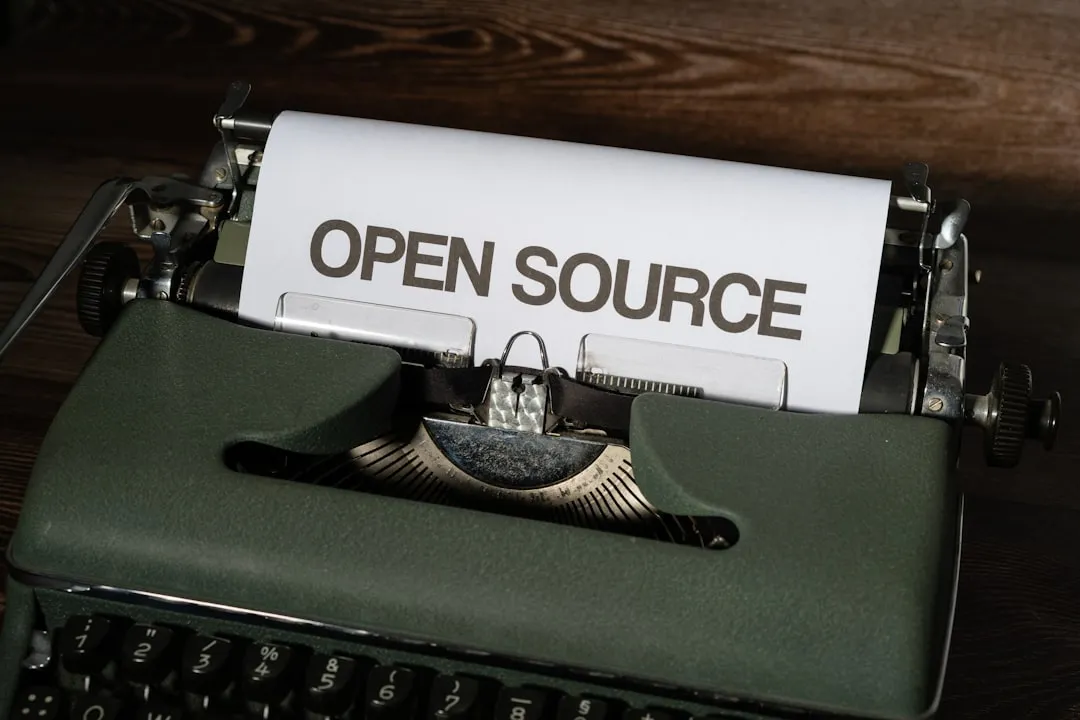
Open Source Security Risks
The exploitation paradox in open source highlights potential security risks. Secure coding practices are essential for maintaining the security of open source projects. Community contributions can introduce vulnerabilities if not properly reviewed.
Ransomware Hits Sensitive Targets Amid AI Security Concerns
A recent ransomware attack on the University of Hawai'i Cancer Center highlights the importance of protecting sensitive data. Meanwhile, the increasing use of AI in development poses new security challenges. Learn about these threats and how to mitigate them.
US Gov iPhone Hack Tool Leaked, Charging Stations Vulnerable
A leaked US government iPhone hacking toolkit poses significant risks to national security and individual privacy. Meanwhile, vulnerabilities in charging station systems could enable attackers to gain unauthorized control or disrupt services. Hackers are also abusing OAuth error flows to spread malware.

AI-Powered Cyberattacks Escalate
Recent cyberattacks have leveraged AI to weaponize code, create deepfakes, and inject malicious data. Enterprises must invest in advanced security measures to stay ahead of emerging threats.

GitHub Copilot and OpenClaw Under Attack
High-severity vulnerabilities in GitHub Copilot and OpenClaw pose significant risks to users. Learn about the threats and how to protect yourself.

Iranian Cyberattacks & Chrome Zero-Days
The UK warns of heightened Iranian cyberattack risks, while Chrome vulnerabilities put thousands at risk. Data breaches and cybercrime continue to threaten global security.
Phishing Campaign Targets Google Users
A sophisticated phishing campaign is using a fake Google security site to steal credentials and MFA codes. Meanwhile, Samsung settles over smart TV data collection, and Claude AI experiences a worldwide outage. Learn about these threats and how to protect yourself.

US-Israel and Iran Engage in Critical Cyberattacks
The US, Israel, and Iran are engaged in a series of critical cyberattacks, including wiper malware and DDoS attacks. North Korean APT groups target air-gapped systems, while cyberattacks on government and critical infrastructure continue to pose a threat.
Zero-Day AI Threats and Cloud Security Updates
Critical zero-day vulnerabilities in AI systems pose significant threats, while cloud security enhancements offer new protections. Learn about the latest developments and how to stay secure.

Critical Flaws in Juniper Routers and Windows 11
New vulnerabilities have been discovered in Juniper Networks PTX routers and Windows 11, posing a significant threat to cybersecurity. These flaws can be exploited by attackers to gain remote access and execute malicious code. It is essential to patch these vulnerabilities immediately to prevent potential attacks.

Cybercrime Crackdown: Europol Arrests & Crypto Scam Seizures
Europol's crackdown on 'The Com' cybercrime gang leads to 30 arrests, while the US Department of Justice seizes $61 million in Tether linked to pig butchering crypto scams. Learn about these significant law enforcement actions and their impact on the cybercrime landscape.
Mexican Gov Hack & Google API Leak
A critical cyberattack on the Mexican government utilizing AI abuse has resulted in significant data theft, while thousands of exposed Google Cloud API keys pose a risk to sensitive data. Learn about these threats and how to protect yourself.
Ransomware Hits Healthcare
A critical ransomware attack has hit a Mississippi healthcare system, while over 900 Sangoma FreePBX instances have been compromised in ongoing web shell attacks. These incidents highlight the vulnerability of healthcare systems to cyber threats.

AI and Crypto Under Siege
Critical vulnerabilities in OpenClaw AI and cryptocurrency wallets have led to significant financial losses, while notorious threat actors like Kimwolf continue to wreak havoc. Stay informed on the latest threats and learn how to protect yourself.
Cybersecurity Research and Awareness
Expert recommends preparing for post-quantum cryptography now, while Samsung updates ACR privacy practices after Texas lawsuit. The rise of ransomware has generated funding for a complex criminal ecosystem.

Malicious Browser Extensions and Go Modules on the Rise
Thousands of users have been affected by a compromised Chrome extension, QuickLens, stealing crypto. Meanwhile, a malicious Go module has been discovered, harvesting passwords and deploying a Linux backdoor. Learn how to protect yourself from these threats.

Pentagon Flags Anthropic as Supply Chain Risk
The Pentagon has designated Anthropic as a supply chain risk due to concerns over its AI model's use in military applications, highlighting growing concerns about AI-related threats to national security. This decision raises questions about the need for robust mitigations and the potential risks of AI in military contexts. Readers should understand the implications of this designation and how it may impact the development and deployment of AI technologies.
Chrome Zero-Day & Azure Ransomware Attacks
A critical Google Chrome zero-day vulnerability is being exploited, while a Microsoft Azure vulnerability is being used by ransomware attackers. Learn about these threats and how to protect yourself.

Cisco SD-WAN Zero-Day Exploited, Devs Targeted, ICS Vulnerabilities Found
A critical Cisco SD-WAN zero-day is being exploited, while developers are being targeted by malicious campaigns and industrial control systems are vulnerable to new threats. Learn how to protect yourself and your organization from these emerging threats.

Cisco SD-WAN Zero-Day Under Active Exploitation
A critical zero-day vulnerability in Cisco SD-WAN has been exploited since 2023, allowing attackers to bypass authentication and gain administrative access. Meanwhile, a data breach at European DIY chain ManoMano has affected 38 million customers, highlighting the importance of securing third-party services and patching vulnerabilities.

Cisco SD-WAN Zero-Day Exploited, UAT-10027 Hits US Education
A critical Cisco SD-WAN zero-day is being exploited, while UAT-10027 targets US education and healthcare. EV2GO and SWITCH EV charging systems also have severe vulnerabilities.
Critical Charging Infrastructure Vulnerabilities and Cisco SD-WAN Zero-Day Exploit
Multiple critical vulnerabilities have been discovered in charging infrastructure systems, while a zero-day exploit has been found in Cisco SD-WAN. These threats highlight the importance of patching and keeping software up to date to prevent large-scale denial of service, privilege escalation, and corruption of data.
Critical Industrial Control System Vulnerabilities Under Active Exploitation
Multiple vulnerabilities in Yokogawa Centum and Exaopc products are under active exploitation, allowing attackers to gain control of industrial control systems. Cisco IOS and IOS XE software patches are also available to prevent further exploitation. Immediate action is required to patch these vulnerabilities.
Critical Router Flaws and State-Sponsored Hacks Expose Networks
Zero-day vulnerabilities in Juniper Networks PTX and Zyxel routers allow for full router takeover, while Chinese cyberspies breach telecom firms and government agencies. Ransomware and cybercrime threats also persist.

Critical Vulnerabilities and Malicious Campaigns Targeting Multiple Sectors
Newly disclosed vulnerabilities in software and hardware, along with malicious campaigns targeting specific sectors, pose significant threats to cybersecurity. Readers should be aware of these risks and take necessary precautions to protect themselves.

Cybersecurity Industry News and Best Practices
The cybersecurity industry is evolving rapidly with new threats and technologies emerging daily, highlighting the importance of staying informed about the latest threats and trends to maintain a strong security posture. Recent vulnerabilities in software development workflows and critical security flaws in software products underscore the need for regular patching and employee education. By understanding these risks and taking proactive measures, organizations can better protect themselves against cyber attacks.

Industrial Control System Vulnerabilities Pose Critical Threats
Recent vulnerabilities in industrial control systems highlight the need for ongoing security maintenance and updates. Cybersecurity research emphasizes the importance of awareness and best practices to ensure business continuity.
Critical Infrastructure Under Fire
Johnson Controls Frick Controls Quantum HD vulnerabilities pose a high risk to critical infrastructure, while the Aeternum botnet loader emerges as a new threat. Learn about these emerging threats and how to protect against them.

Ongoing Cyberattacks and Data Breaches
Multiple high-severity cyberattacks and data breaches are ongoing, including North Korean hackers deploying new malware to breach air-gapped networks and compromises of medical device manufacturer UFP Technologies and Sangoma FreePBX instances. These attacks highlight the need for vigilance in cybersecurity.

Other Notable Threats Emerge as Ransomware and Zero-Days Persist
A previously undocumented threat activity cluster targets US education and healthcare, while Zyxel patches a critical vulnerability in its routers. Meanwhile, ransomware attacks and zero-day exploits continue to pose significant threats.
Ransomware Payments Plummet Amidst Surge in Attacks
Despite a surge in ransomware attacks, payments to threat actors have dropped significantly. This trend, combined with the emergence of AI-powered fake ID sites and cyberattacks on medical device makers, underscores the evolving landscape of cybersecurity threats.
Targeted Attacks Hit Developers and Critical Infrastructure
Sophisticated threat actors are targeting developers and critical infrastructure with malicious repositories, backdoors, and vulnerabilities. Stay ahead of the threats with our analysis and recommendations.
Zero-Day Attacks Surge: Aeternum Botnet, Critical Infrastructure Vulnerabilities, and Malicious Developer Campaigns
A surge in zero-day attacks, including the Aeternum botnet and critical infrastructure vulnerabilities, poses significant threats to global security. Meanwhile, malicious campaigns target developers and financial sectors, highlighting the need for enhanced cybersecurity measures.

Chinese Cyberspies Breach Telecom Firms as Malicious Packages Target Developers
Chinese cyberspies have breached dozens of telecom firms and governments worldwide, while malicious packages target developers and the financial sector. Ransomware and data breaches affect multiple industries, and security patches address critical vulnerabilities.
Critical Cisco SD-WAN Flaw Exploited, China-Linked Espionage Uncovered, and EV Charging Hacks
A critical vulnerability in Cisco SD-WAN is being exploited, a Chinese cyber espionage campaign has been disrupted by Google, and vulnerabilities have been found in electric vehicle charging infrastructure. These threats pose significant risks to network security, intellectual property, and critical infrastructure.

Cisco SD-WAN Under Attack
Multiple Cisco SD-WAN vulnerabilities are being actively exploited, while developers and IT systems face targeted attacks. Learn about the key threats and how to protect yourself.
Critical Cisco SD-WAN Vulnerabilities Exploited
Multiple critical vulnerabilities in Cisco SD-WAN products are being exploited, allowing attackers to gain admin access and potentially disrupt critical infrastructure. Ransomware attacks are also on the rise, with a recent surge in attack numbers despite decreased payments.
Cisco SD-WAN Zero-Day Exploited, Chinese Cyber Espionage Disrupted
A critical zero-day vulnerability in Cisco SD-WAN is being actively exploited by attackers, while Google disrupts a Chinese cyber espionage campaign targeting telecoms and governments worldwide. Learn about the key threats and how to protect your organization.

Cisco SD-WAN Zero-Day Exploited, Devs Targeted, and Major Breaches
A critical Cisco SD-WAN zero-day is under active exploitation, while developers face targeted attacks, and major data breaches hit millions of users. Learn about the threats and how to protect yourself.

Cisco SD-WAN Zero-Day Under Active Exploitation
A critical zero-day vulnerability in Cisco SD-WAN is being actively exploited, allowing attackers to bypass authentication and gain administrative access. This vulnerability affects Cisco Catalyst SD-WAN Controller and Manager, with a patch available. Readers should prioritize updating their systems to prevent exploitation.

Cisco SD-WAN Zero-Day Exploited, AI Threats Rise
Critical Cisco SD-WAN vulnerabilities are under active exploitation, while malicious AI-related activities and targeted attacks on critical infrastructure pose significant threats to global security. Learn about the key risks and how to protect your organization.

Critical Cisco SD-WAN Bugs Exploited Amidst Zero-Days and AI Threats
Active exploitation of critical Cisco SD-WAN vulnerabilities, alongside zero-day exploits in cyber espionage campaigns and malicious AI-generated code attacks, pose significant threats to global cybersecurity. Learn about the key risks and necessary mitigation strategies.
Emerging Threats Accelerate Network Breaches
Newly discovered vulnerabilities, including Spectre-like exploits and critical Serv-U flaws, are accelerating network breaches. Organizations must stay informed to ensure timely mitigation.

Industrial Control System Vulnerabilities Pose Significant Risks
The Cybersecurity and Infrastructure Security Agency (CISA) has warned of vulnerabilities in InSAT MasterSCADA and Schneider Electric EcoStruxure Building Operation products, which could allow remote code execution and unauthorized access to sensitive data. These vulnerabilities pose significant risks to critical infrastructure sectors, including energy, water, and transportation systems.

Industrial Control Systems Under Siege
Critical vulnerabilities in industrial control systems pose significant risks, while malicious activities target developers and supply chains with fake job interviews and social engineering attacks. Learn about the key threats and how to protect against them.
Ransomware and Cyber Espionage Threats Escalate
Ransomware and cyber espionage campaigns are on the rise, targeting critical infrastructure and sensitive information. Recent attacks include a Chinese cyber espionage campaign that breached 53 organizations across 42 countries, and the Lazarus Group's use of Medusa ransomware in attacks on the Middle East and US healthcare sectors.
Ransomware Attacks Surge
A surge in ransomware attacks targets healthcare organizations, while a medical device maker discloses a data breach and phishing campaigns hit freight companies. Learn about the key threats and how to protect yourself.
Ransomware Payments Plummet Amidst Rising Attacks
Despite a surge in ransomware attacks, payments to threat actors have reached an all-time low. Recent incidents include the breach of Olympique Marseille and a lawsuit against SonicWall. Learn about the evolving landscape of ransomware threats and how to defend against them.

Critical Vulnerabilities Exposed in Trend Micro, Juniper, and Zyxel Products
Newly disclosed vulnerabilities in Trend Micro, Juniper Networks, and Zyxel products pose significant risks to users. ICS and energy sector vulnerabilities are also highlighted, emphasizing the need for urgent patches and security measures.

CarGurus Breach & Zero-Day Sales Rock Cybersecurity
A massive data breach at CarGurus exposed 12.4 million accounts, while a former defense contractor employee was jailed for selling zero-days to a Russian broker. Learn about these critical threats and how to protect yourself.

Cisco SD-WAN Zero-Day Exploited, Plus Ransomware and SolarWinds Patches
A critical zero-day vulnerability in Cisco SD-WAN is being actively exploited, while the Lazarus Group launches a Medusa ransomware campaign and SolarWinds patches critical Serv-U flaws. Learn about these threats and how to protect your organization.

Critical Cisco and Zyxel Vulnerabilities Under Attack
Multiple critical vulnerabilities in Cisco SD-WAN and Zyxel routers are being actively exploited, posing significant risks to organizations. Learn about the threats and how to protect your networks.

Critical Software Vulnerabilities Pose High Risk
Newly discovered vulnerabilities in popular software pose a significant threat to users, with potential for remote code execution and root access. Recent research also highlights the speed at which attackers can own a network using credential misuse and AI tools.

Data Breaches, Extortion, and Code Execution Flaws
Multiple high-severity data breaches and extortion attempts have been reported, alongside critical vulnerabilities in software that could allow for remote code execution. These threats pose significant risks to organizations and individuals alike, highlighting the need for robust security measures.
Lazarus Group Attacks Healthcare with Medusa Ransomware
The Lazarus Group has launched targeted attacks on healthcare and Middle East entities using Medusa ransomware, while vulnerabilities in InSAT MasterSCADA and Schneider Electric products pose additional risks to critical infrastructure. Learn about the threats and how to protect your organization.

Nation-State Cyberattacks Surge
MuddyWater, APT28, and Lazarus Group launch targeted attacks on organizations worldwide. Learn about the latest nation-state sponsored cyber threats and how to protect your organization.

RoguePilot & SANDWORM_MODE Threats Uncovered
High-severity vulnerabilities in GitHub Codespaces and npm packages have been discovered, posing significant risks to developers and the software supply chain. The RoguePilot flaw and SANDWORM_MODE campaign highlight the need for vigilance in AI-driven development tools and open-source dependencies.

Zero-Day Vulnerability Under Active Exploitation
A critical zero-day vulnerability is being actively exploited, while significant data breaches and new malware campaigns pose high risks to users. Immediate action is necessary to prevent further exploitation.
Zero-Days & Ransomware: Twin Threats to US Security
The Lazarus Group's Medusa ransomware attacks and active exploitation of zero-day vulnerabilities pose significant threats to national security. Recent incidents involve a former US defense contractor employee selling zero-day exploits to a Russian broker and the targeting of US healthcare organizations with Medusa ransomware.

AI-Related Security Threats Escalate
Recent discoveries highlight the growing concern of AI-related security threats, including vulnerabilities in GitHub Codespaces and industrial-scale campaigns by Chinese AI firms to extract capabilities from models like Claude. These threats pose significant risks to repository security and model integrity.

Critical Vulnerabilities Under Attack
Multiple critical vulnerabilities are being actively exploited by threat actors, including the ShinyHunters extortion gang and North Korean state-backed hackers. New malware families and supply chain attacks are also on the rise, targeting healthcare organizations and financial institutions.
Reddit Fined $19M, VMware Patches Critical Flaws
The UK fines Reddit $19 million for unlawful use of children's data. Meanwhile, VMware patches critical vulnerabilities and the cybersecurity industry sees a surge in AI-focused investments. Learn about the latest threats and best practices.

SolarWinds & FortiGate Under Attack
Critical vulnerabilities in SolarWinds and FortiGate pose significant risks, while recent ransomware attacks and newly disclosed threats demand immediate attention from security teams. Learn about the key threats and how to protect your organization.