Introduction
A recent wave of cyberattacks has targeted critical infrastructure in the United States, with Iranian-affiliated advanced persistent threat (APT) actors exploiting programmable logic controllers (PLCs) and Russian hackers stealing Microsoft Office tokens via router exploitation. These attacks have resulted in operational disruptions and financial losses across multiple sectors, including government services, water and wastewater systems, and energy. According to CISA, the Iranian-affiliated actors have targeted internet-facing operational technology (OT) devices, including Rockwell Automation/Allen-Bradley-manufactured PLCs. Meanwhile, Russian military intelligence units have used known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, as reported by Krebs on Security.
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers
The Iranian-affiliated advanced persistent threat (APT) actors have been conducting exploitation activity targeting internet-facing OT devices, including PLCs manufactured by Rockwell Automation/Allen-Bradley. This activity has led to PLC disruptions across several US critical infrastructure sectors, resulting in operational disruption and financial loss. The actors have used leased, third-party hosted infrastructure with configuration software, such as Rockwell Automation's Studio 5000 Logix Designer software, to create an accepted connection to the victim's PLC. Targeted devices include CompactLogix and Micro850 PLC devices. As noted by CISA, the actors have used commonly used OT ports to communicate with PLCs, including ports 44818, 2222, 102, and 502.
To mitigate these attacks, organizations should urgently review the tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) for indications of current or historical activity on their networks. The following steps can be taken:
- Remove PLCs from direct internet exposure via secure gateway and firewall.
- Query available logs for the provided IOCs in the corresponding time frames.
- Check available logs for suspicious traffic on the ports associated with OT devices.
- Implement multifactor authentication (MFA) for access to the OT network from an external network.
Russia-Linked Hackers Steal Microsoft Office Tokens via Router Exploitation
Russian military intelligence units have been using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users. The spying campaign has allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code. The attack targets small office and home office routers with weak security settings or outdated software. According to Bleeping Computer, authorities have disrupted the FrostArmada campaign, which hijacked local traffic from MikroTik and TP-Link routers to steal Microsoft account credentials.
To protect against these attacks, organizations should ensure that their routers are updated with the latest security patches and implement robust security measures, such as:
- Changing default passwords and settings
- Enabling MFA for access to the network
- Using a virtual private network (VPN) to encrypt internet traffic
- Regularly monitoring network activity for suspicious behavior
Mitsubishi Electric GENESIS64 and ICONICS Suite Products Vulnerabilities
Mitsubishi Electric GENESIS64 and ICONICS Suite products contain vulnerabilities that could allow a local attacker to disclose SQL Server credentials. The vulnerabilities, identified as CVE-2025-14815 and CVE-2025-14816, are due to cleartext storage of sensitive information and cleartext storage of sensitive information in the GUI. According to CISA, successful exploitation of these vulnerabilities could allow a local attacker to disclose SQL Server credentials used by the affected products and use them to disclose, tamper with, or destroy data, or to cause a denial-of-service (DoS) condition on the system.
To mitigate these vulnerabilities, Mitsubishi Electric recommends performing the following steps:
- Updating to fixed versions of the affected products
- Changing the permissions of HHSplitter.exe so that only trusted administrators can execute it
- Deleting HHSplitter.exe from the system if it is unnecessary
- Using Windows authentication instead of SQL authentication for the SQL server authentication method
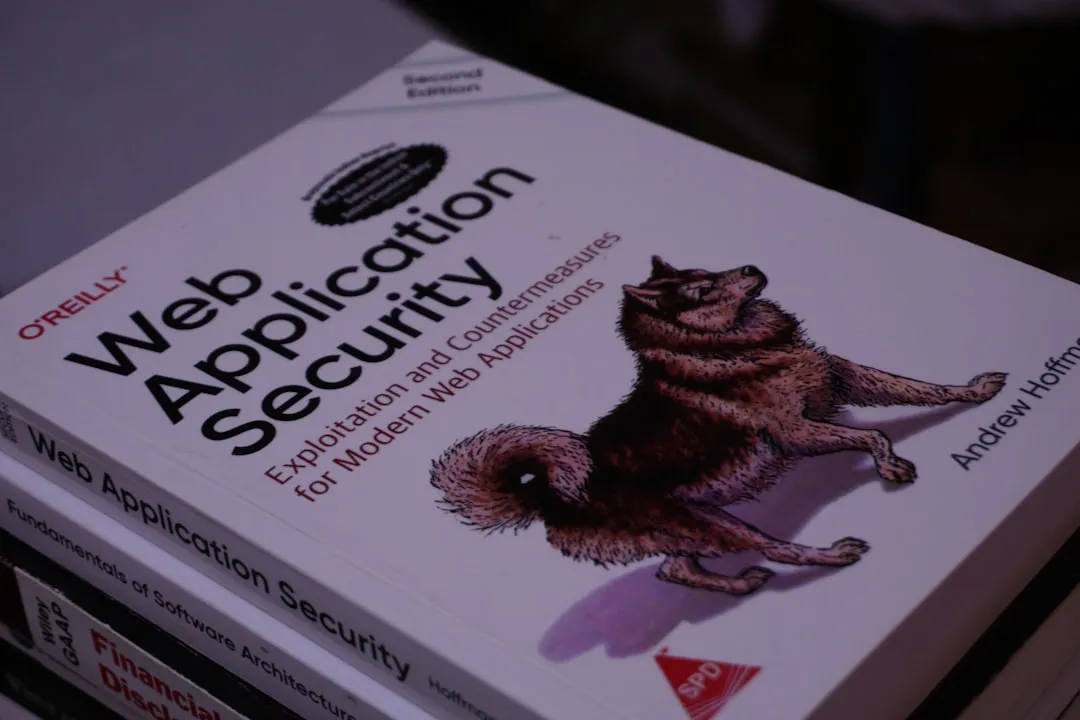
Recommendations and Takeaways
To protect against these cyber threats, security practitioners should take the following steps:
- Implement robust security measures, such as MFA and VPNs, to protect against unauthorized access
- Regularly monitor network activity for suspicious behavior
- Update software and systems with the latest security patches
- Use secure protocols for communication, such as HTTPS and SFTP
- Limit access to sensitive data and systems to authorized personnel only
- Conduct regular security audits and risk assessments to identify vulnerabilities and weaknesses
By taking these steps, organizations can reduce their risk of being targeted by cyber threats and protect their critical infrastructure from disruption. As noted by CISA, it is essential for organizations to stay vigilant and proactive in their cybersecurity efforts to prevent and respond to cyber threats effectively. Key action items include:
- Applying the latest security patches to PLCs and routers
- Implementing MFA for all remote access to OT networks
- Conducting regular network monitoring and incident response planning
- Ensuring all employees understand cybersecurity best practices and phishing attack prevention techniques.