Introduction
A recent arbitrary file-write flaw discovered in the GIGABYTE Control Center has raised concerns over the validity of vulnerability research findings, as AI breakthroughs render traditional security measures ineffective. With the ability to deobfuscate any minified JavaScript code, AI poses a significant threat to current security practices. The stakes are high, with potential impacts on user data and system security. As Bleeping Computer reports, the GIGABYTE Control Center vulnerability allows remote access to files on vulnerable hosts, highlighting the need for robust security practices.
The validity of vulnerability research has been called into question, with concerns over the accuracy of findings. This is particularly concerning given the growing reliance on vulnerability research to inform security decisions. According to Sockpuppet, the issue of cooked vulnerability research has significant implications for the security community. Furthermore, the use of AI in deobfuscating JavaScript code raises concerns about the effectiveness of current obfuscation techniques. As Afterpack notes, AI can deobfuscate any minified JavaScript code, rendering obfuscation ineffective as a security measure.
The GIGABYTE Control Center is a utility software that allows users to monitor and control various aspects of their system, including fan speeds, temperature, and voltage. The software is widely used by gamers and overclockers, who rely on it to optimize their system's performance. However, the discovery of the arbitrary file-write flaw has raised concerns about the potential risks associated with using this software.
Security Research and Vulnerability Disclosures
Vulnerability research is a cornerstone of the security community, providing valuable insights into potential threats. Recent concerns over the validity of findings have raised questions about the effectiveness of this research. According to Sockpuppet, vulnerability research has been called into question, with concerns over the accuracy of findings. This is particularly concerning given the growing reliance on vulnerability research to inform security decisions.
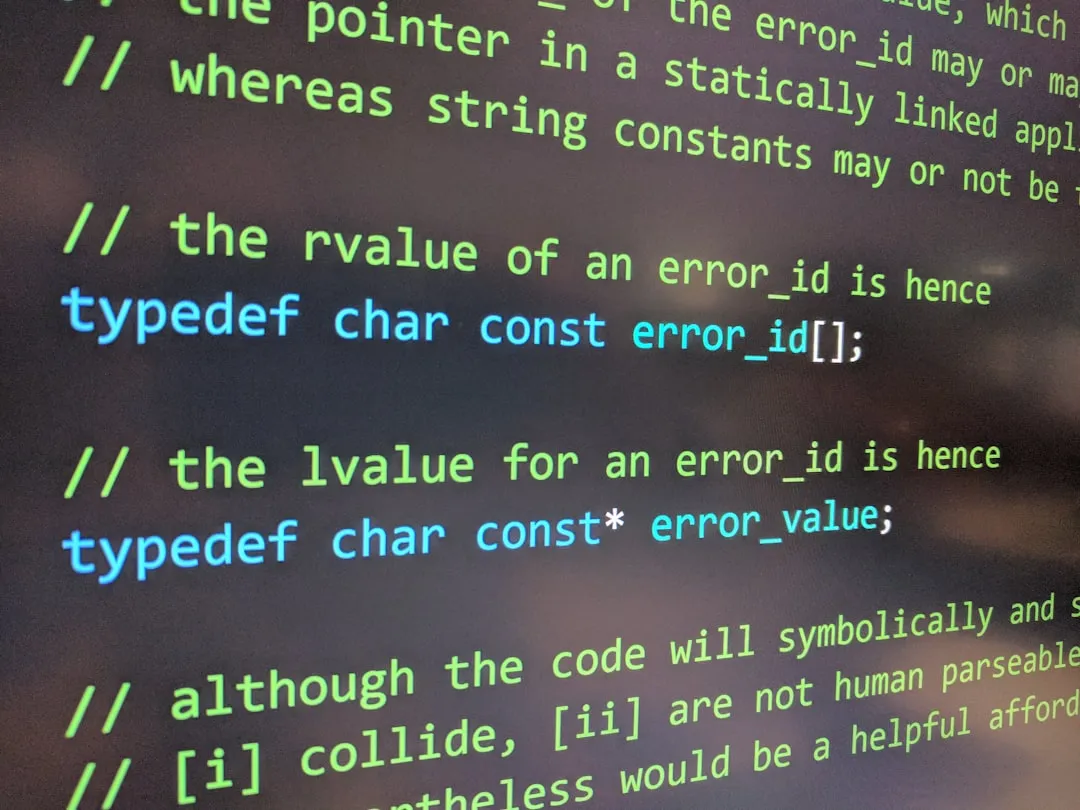
The use of AI in deobfuscating JavaScript code has significant implications for security practices. As Afterpack notes, AI can deobfuscate any minified JavaScript code, rendering obfuscation ineffective as a security measure. This raises concerns about the effectiveness of current security measures and highlights the need for alternative approaches.
The GIGABYTE Control Center vulnerability is a prime example of the risks associated with inadequate security practices. As Bleeping Computer reports, the vulnerability allows remote access to files on vulnerable hosts, making it a prime target for attackers. To exploit this vulnerability, an attacker would need to send a specially crafted request to the affected system, which would then allow them to write arbitrary files to the system.
The technical details of the vulnerability are as follows:
- The vulnerability affects the GIGABYTE Control Center software, version
1.0.0.0and earlier. - The vulnerability is caused by a flaw in the
file_writefunction, which allows an attacker to write arbitrary files to the system. - The vulnerability can be exploited remotely, without the need for authentication or physical access to the system.
To mitigate this risk, it is essential to update the GIGABYTE Control Center to prevent exploitation of the arbitrary file-write flaw. Additionally, organizations should reevaluate their use of obfuscation as a security technique, given AI's deobfuscation capabilities.
Recommendations and Takeaways
To maintain trust in security measures, it is crucial to ensure the validity of vulnerability research findings. This can be achieved by implementing robust testing and validation procedures, as well as promoting transparency and accountability within the security community. According to Sockpuppet, the issue of cooked vulnerability research has significant implications for the security community.
Given AI's deobfuscation capabilities, it is essential to reevaluate the use of obfuscation as a security technique. Alternative approaches, such as encryption and secure coding practices, should be prioritized to ensure the confidentiality and integrity of sensitive data. The GIGABYTE Control Center vulnerability highlights the need for robust security practices, including regular updates and patches to prevent exploitation of known vulnerabilities.
To mitigate the risks associated with the GIGABYTE Control Center vulnerability, organizations should:
- Update the GIGABYTE Control Center to version
1.0.1.0or later, which includes a patch for the arbitrary file-write flaw. - Reevaluate their use of obfuscation as a security technique, given AI's deobfuscation capabilities.
- Implement robust testing and validation procedures to ensure the validity of vulnerability research findings.
- Promote transparency and accountability within the security community to maintain trust in security measures.
- Use encryption and secure coding practices to protect sensitive data.
- Regularly update and patch software to prevent exploitation of known vulnerabilities.
Additionally, organizations should consider implementing the following security controls:
- Network segmentation: Segmenting the network into smaller, isolated zones can help reduce the attack surface and prevent lateral movement in case of a breach.
- Access control: Implementing strict access controls, such as role-based access control (RBAC), can help limit the damage caused by a breach.
- Monitoring and logging: Monitoring and logging system activity can help detect and respond to potential security incidents.
By prioritizing these recommendations, organizations can reduce the risk of exploitation and maintain the confidentiality and integrity of sensitive data. As the security landscape continues to evolve, it is essential to stay informed about emerging threats and adapt security practices accordingly. To ensure a secure digital environment, take the following actions:
- Stay up-to-date with the latest vulnerability research and patches.
- Implement robust security measures, including encryption and secure coding practices.
- Promote transparency and accountability within the security community.
- Regularly review and update security protocols to address emerging threats.