Introduction
A surge in attacks on critical infrastructure has left many organizations vulnerable, with Johnson Controls Frick Controls Quantum HD vulnerabilities and the emergence of the Aeternum botnet loader posing significant risks. According to CISA, multiple high-risk vulnerabilities were discovered in Johnson Controls Frick Controls Quantum HD, including OS command injection and code injection flaws, which could lead to pre-authentication remote code execution, information leak, or denial of service. The Aeternum botnet loader has been using a blockchain-based command-and-control infrastructure to evade takedown efforts, as reported by The Hacker News. This article delves into the details of these threats and provides recommendations for protection.
Johnson Controls Frick Controls Quantum HD Vulnerabilities
Vulnerability Details
The vulnerabilities discovered in Johnson Controls Frick Controls Quantum HD are classified as high-risk, with a CVSS score of 9.1. Affected versions include Frick Controls Quantum HD <=10.22, and identified CVEs include CVE-2026-21654, CVE-2026-21656, CVE-2026-21657, CVE-2026-21658, CVE-2026-21659, and CVE-2026-21660. These vulnerabilities can be exploited by an unauthenticated attacker to execute arbitrary code on the affected device, leading to full system compromise. The CISA advisory recommends upgrading to the latest platform, Quantum HD Unity, version 12 or higher, to mitigate these vulnerabilities.
The CVE-2026-21654 vulnerability allows an unauthenticated attacker to inject OS commands, potentially leading to remote code execution. This is caused by insufficient validation of input in certain parameters, permitting unexpected actions before authentication occurs. Similarly, the CVE-2026-21656 vulnerability allows for code injection, which could also lead to remote code execution.
Frick Controls Quantum HD systems are widely used in critical infrastructure, including food and agriculture sectors, controlling and monitoring various industrial processes. This makes them a prime target for attackers seeking to disrupt or exploit these processes.
Mitigation Guidance
To mitigate the vulnerabilities in Johnson Controls Frick Controls Quantum HD, organizations should:
- Upgrade to the latest platform, Quantum HD Unity, version 12 or higher, as recommended by CISA.
- Implement defensive measures to minimize exploitation risk, such as minimizing network exposure and using secure remote access methods.
- Use a firewall to restrict incoming and outgoing traffic to necessary ports and protocols.
- Implement intrusion detection and prevention systems to detect and prevent potential attacks.
- Perform regular security audits and vulnerability assessments to identify and address weaknesses.
Aeternum Botnet Loader and Other Emerging Threats
Blockchain-Based Command-and-Control Infrastructure
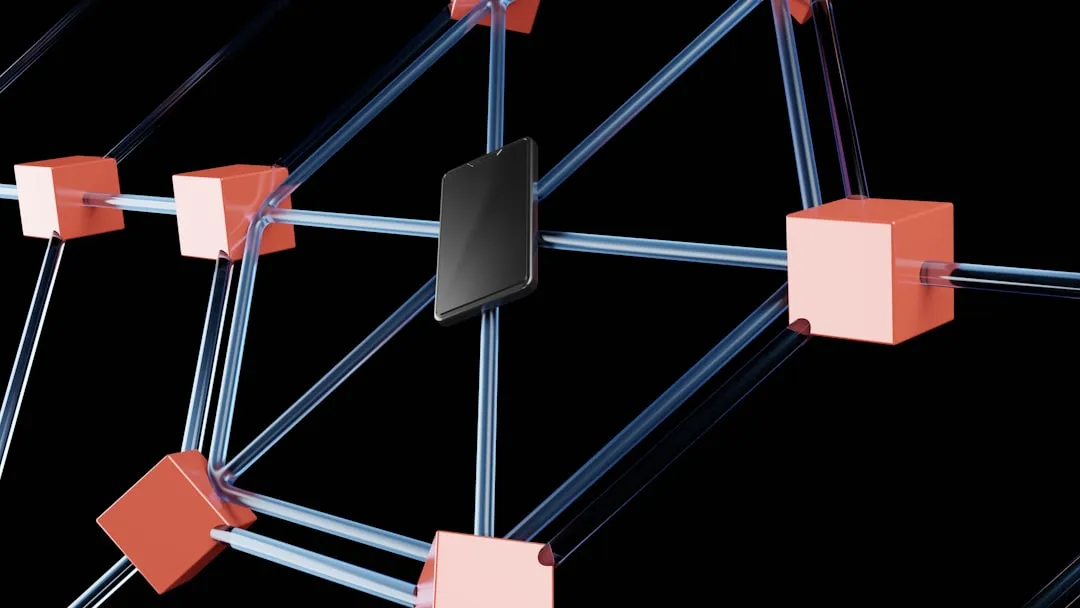
The Aeternum botnet loader uses a blockchain-based command-and-control infrastructure, making it difficult to disrupt. According to SecurityWeek, Aeternum operates on smart contracts, storing instructions on the public Polygon blockchain. This approach allows the botnet to evade traditional takedown efforts, which typically involve taking down command-and-control servers or domains.
Blockchain technology makes Aeternum's command-and-control infrastructure resilient to takedown efforts, posing a challenge for security practitioners. Blockchain-based systems are decentralized and immutable, making it difficult to alter or delete data once written to the blockchain.
Technical Details
Aeternum's blockchain-based command-and-control infrastructure uses smart contracts to store and execute instructions. Smart contracts are self-executing contracts with terms written directly into lines of code. These contracts are stored on the blockchain and can be executed automatically when certain conditions are met.
The Polygon blockchain is a public blockchain allowing for the creation and execution of smart contracts. It is a decentralized platform, meaning there is no central authority controlling the network. This makes it an attractive option for attackers seeking to create resilient command-and-control infrastructure.
Mitigation Guidance
To mitigate the threat posed by Aeternum and other botnets using blockchain-based command-and-control infrastructure, organizations should:
- Implement a blockchain-based monitoring system to detect and respond to potential threats.
- Use intrusion detection and prevention systems to detect and prevent potential attacks.
- Implement defensive measures to minimize exploitation risk, such as minimizing network exposure and using secure remote access methods.
- Stay informed about emerging threats and take proactive steps to protect against them.
- Perform regular security audits and vulnerability assessments to identify and address weaknesses.
Recommendations and Takeaways
To protect against these emerging threats, security practitioners should take a proactive and multi-layered approach to security. This includes:
- Staying informed about emerging threats and taking proactive steps to protect against them.
- Implementing defensive measures to minimize exploitation risk, such as minimizing network exposure and using secure remote access methods.
- Performing regular security audits and vulnerability assessments to identify and address weaknesses.
- Using a combination of traditional security measures, such as firewalls and intrusion detection systems, and newer technologies, like blockchain-based monitoring systems.
- Considering implementing a bug bounty program or other forms of crowdsourced security testing to identify and address potential vulnerabilities.
By taking these steps, organizations can reduce their risk of being compromised by emerging threats and better protect their critical infrastructure. It is essential to stay up-to-date with the latest security patches and updates, as well as implement a robust incident response plan to quickly respond to potential security incidents.
In conclusion, the vulnerabilities in Johnson Controls Frick Controls Quantum HD and the emergence of the Aeternum botnet loader pose significant risks to critical infrastructure. To mitigate these threats, organizations must:
- Apply the recommended patches for Johnson Controls Frick Controls Quantum HD.
- Implement blockchain-based monitoring systems to detect Aeternum and similar threats.
- Conduct regular security audits and vulnerability assessments.
- Stay informed about emerging threats through reputable sources like CISA and SecurityWeek. By prioritizing these actions, organizations can protect their critical systems and reduce the risk of compromise.