Introduction
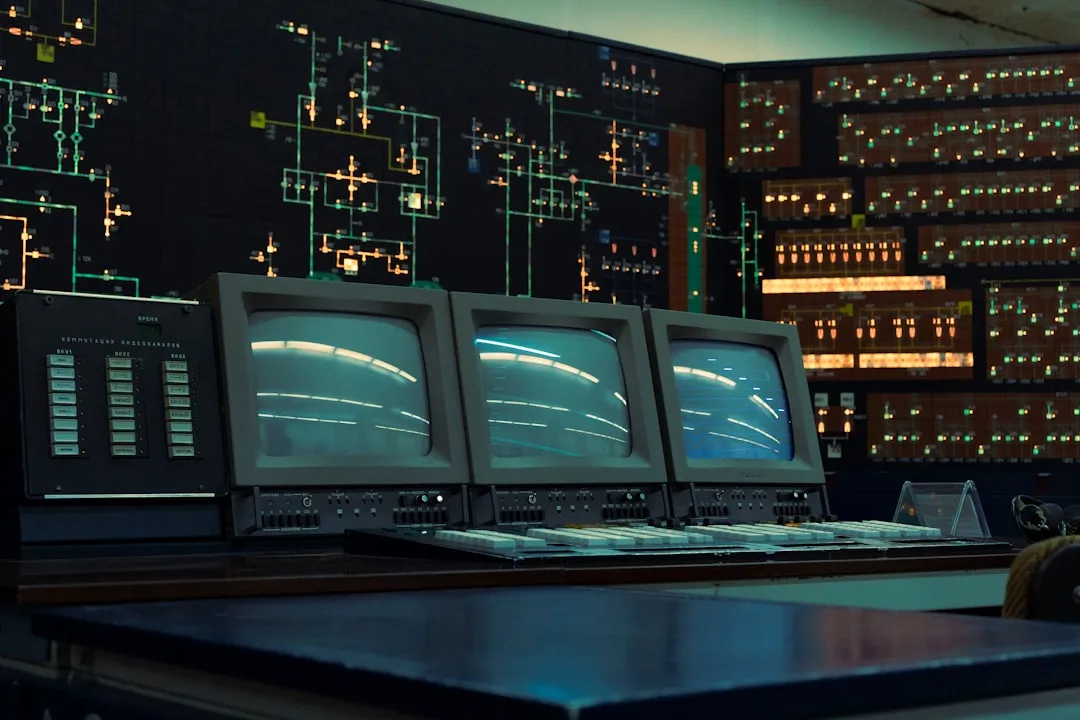
A recent wave of cyber threats is targeting critical infrastructure, with vulnerabilities in industrial control systems and malware targeting routers posing significant risks to national security and public safety. The KadNap malware, for instance, has infected over 14,000 devices, with 60% of victims located in the US, according to The Hacker News. Furthermore, the emergence of AI-powered attacks has introduced a new threat vector, with the potential to autonomously exploit vulnerabilities and evade detection. As reported by The Register, an AI agent was able to hack a chatbot and gain full read-write access in just 2 hours, highlighting the potential risks of AI-powered attacks. The impact of these threats can be devastating, with potential disruptions to critical services such as power grids, water supply systems, and transportation networks.
Critical Infrastructure Vulnerabilities
Multiple critical vulnerabilities have been discovered in industrial control systems, including Ceragon and Lantronix products. These vulnerabilities, such as CVE-2025-57176, could allow attackers to gain unauthorized access, execute arbitrary code, or disrupt critical infrastructure, as detailed in the CISA advisory. For example, the CVE-2025-67039 vulnerability in Lantronix EDS3000PS allows an attacker to bypass authentication and execute code with root-level privileges, as reported by CISA. This vulnerability is particularly concerning, as it could allow an attacker to gain control of the device and use it as a pivot point to launch further attacks on the network.
The Ceragon Siklu MultiHaul and EtherHaul Series devices are also affected by multiple vulnerabilities, including CVE-2025-57176, which allows for unrestricted file upload to the device, as reported by CISA. This vulnerability could allow an attacker to upload malicious files to the device, potentially leading to code execution or disruption of critical services. To mitigate these vulnerabilities, organizations should prioritize patching and securing these systems, following the guidelines provided by CISA and SecurityWeek.
Mitigation Guidance
To mitigate the risks associated with these vulnerabilities, organizations should take the following steps:
- Prioritize patching and securing critical infrastructure systems, focusing on the most critical vulnerabilities first
- Implement robust access controls, including multi-factor authentication and role-based access control, to prevent unauthorized access to devices
- Conduct regular vulnerability assessments and penetration testing to identify and address potential vulnerabilities
- Implement a defense-in-depth strategy, including firewalls, intrusion detection systems, and incident response plans, to detect and respond to potential attacks
- Provide training and awareness programs for employees and contractors to educate them on the risks associated with these vulnerabilities and the importance of following security best practices
KadNap Malware and Router Exploitation
The KadNap malware is targeting ASUS routers and other edge devices to create a proxy botnet, with over 14,000 devices infected, as reported by The Hacker News. The malware was first detected in the wild in August 2025 and has been expanding its reach since then, with 60% of victims located in the US. The botnet is being used for malicious traffic proxying, potentially fueling cybercrime activities such as spamming, phishing, and malware distribution.
The KadNap malware is designed to exploit vulnerabilities in router firmware, allowing it to gain control of the device and use it as a proxy server. The malware uses a combination of exploits and social engineering tactics to infect devices, including phishing emails and drive-by downloads. Once infected, the device becomes part of the botnet, allowing the attackers to use it for malicious activities.
Mitigation Guidance
To mitigate the risks associated with the KadNap malware, organizations should take the following steps:
- Ensure that all routers and edge devices are updated with the latest firmware and security patches
- Implement robust access controls, including multi-factor authentication and role-based access control, to prevent unauthorized access to devices
- Conduct regular vulnerability assessments and penetration testing to identify and address potential vulnerabilities
- Implement a defense-in-depth strategy, including firewalls, intrusion detection systems, and incident response plans, to detect and respond to potential attacks
- Provide training and awareness programs for employees and contractors to educate them on the risks associated with the KadNap malware and the importance of following security best practices
AI and Cybersecurity
AI agents can potentially open new attack vectors by acting as autonomous entities with access to sensitive data and systems. The lack of visibility into AI agent activities can make it difficult for organizations to detect and respond to security incidents, as reported by The Hacker News. A webinar guide is available for auditing modern AI workflows to prevent data leaks, providing guidance on how to secure AI systems and prevent potential attacks.
The use of AI agents in cybersecurity can be beneficial, as they can help to detect and respond to threats more quickly and effectively than human analysts. However, the use of AI agents also introduces new risks, such as the potential for AI-powered attacks. To mitigate these risks, organizations should take the following steps:
- Implement robust security controls, including access controls and encryption, to protect AI systems and data
- Conduct regular security audits and risk assessments to identify and address potential vulnerabilities
- Provide training and awareness programs for employees and contractors to educate them on the risks associated with AI-powered attacks and the importance of following security best practices
- Implement a defense-in-depth strategy, including firewalls, intrusion detection systems, and incident response plans, to detect and respond to potential attacks
Recommendations and Takeaways
To protect against these threats, organizations should prioritize patching and securing critical infrastructure systems, following the guidelines provided by CISA. Users should ensure their routers are updated and secure to prevent exploitation by the KadNap malware, following the guidelines provided by BleepingComputer. Additionally, organizations should be aware of the potential cybersecurity implications of using AI and take steps to secure their systems, following the guidelines provided by The Register. Key recommendations include:
- Prioritizing patching and securing critical infrastructure systems
- Ensuring routers are updated and secure to prevent exploitation by the KadNap malware
- Being aware of the potential cybersecurity implications of using AI and taking steps to secure AI systems
- Implementing robust cybersecurity strategies to protect against emerging threats, including AI-powered attacks
- Following guidelines provided by CISA, SecurityWeek, and BleepingComputer to secure critical infrastructure systems and prevent potential attacks.