Introduction
A devastating cyberattack on the Mexican government has resulted in the theft of over 150GB of sensitive data, leveraging AI abuse to automate exploitation and exfiltration. This incident, combined with the exposure of thousands of Google Cloud API keys, poses a significant risk to sensitive data and underscores the growing concerns surrounding AI abuse and cloud security risks. The need for robust security measures to protect against such threats has never been more pressing.
The Mexican government cyberattack and the exposure of Google Cloud API keys are stark reminders of the evolving threat landscape. As attackers increasingly exploit AI capabilities and cloud infrastructure vulnerabilities, organizations must prioritize securing their systems and data to prevent similar incidents. This article will delve into the details of these attacks, exploring the tactics, techniques, and procedures (TTPs) employed by the attackers, as well as the implications for cloud security and AI abuse.
The use of AI-powered tools in cyberattacks is becoming increasingly common, allowing attackers to automate and scale their operations. In the case of the Mexican government hack, the attackers leveraged Claude Code, an AI tool, to write exploits, create tools, and exfiltrate data according to SecurityWeek. This incident highlights the growing concern of AI abuse in cyberattacks, where attackers exploit AI capabilities to enhance their abilities and evade detection.
Mexican Government Cyberattack and AI Abuse
The cyberattack on the Mexican government involved the weaponization of Claude Code, an AI tool used to write exploits, create tools, and exfiltrate data according to SecurityWeek. The attackers utilized AI capabilities for automated exploitation and data exfiltration, resulting in the theft of sensitive information. This incident highlights the growing concern of AI abuse in cyberattacks, where attackers leverage AI tools to enhance their capabilities and evade detection.
The attack's impact is evident in the sheer volume of data stolen - over 150GB of sensitive information. The use of Claude Code in this attack demonstrates the increasing sophistication of attackers, who are now exploiting AI capabilities to carry out complex cyberattacks. As AI abuse continues to evolve, organizations must adapt their security strategies to address these emerging threats.
To better understand the implications of this attack, it is essential to consider the technical details. The attackers likely exploited vulnerabilities in the Mexican government's systems, potentially using phishing or social engineering tactics to gain initial access. Once inside, they leveraged Claude Code to automate their operations, exploiting weaknesses in the system to exfiltrate sensitive data.
The use of AI-powered tools in this attack also raises concerns about the potential for lateral movement, where attackers move undetected through a network, exploiting vulnerabilities and gathering sensitive information. Organizations must ensure that their systems are properly segmented, with robust access controls and monitoring in place to detect and respond to suspicious activity.
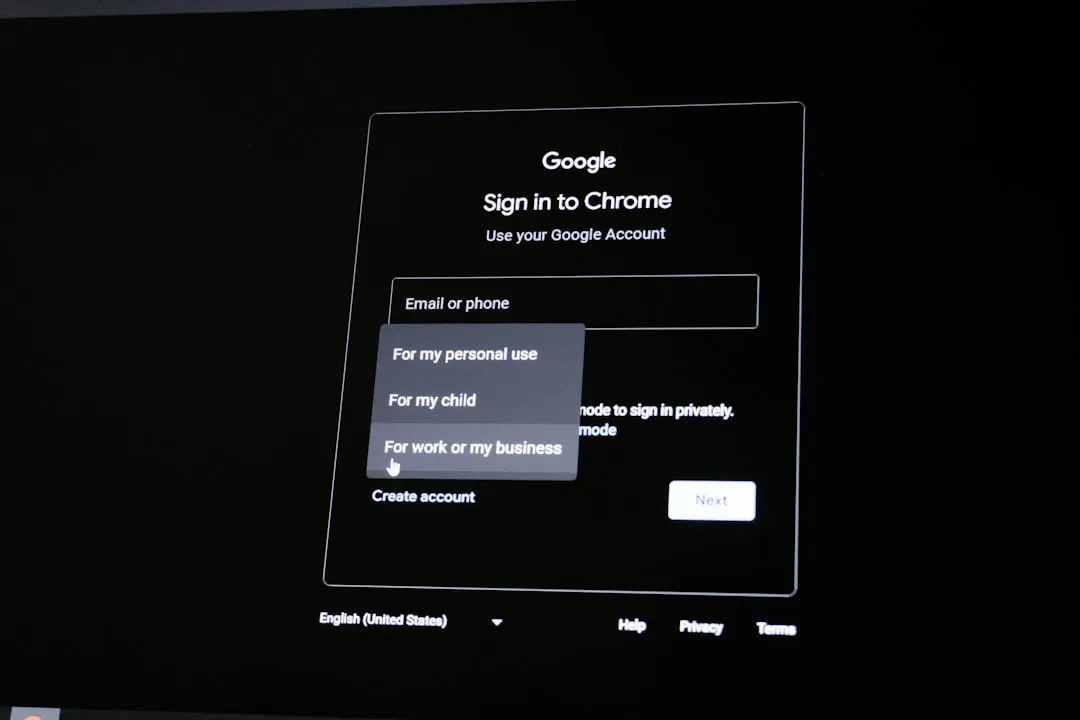
Google Cloud API Keys Exposure
Thousands of public Google Cloud API keys have been exposed, potentially allowing access to sensitive data according to The Hacker News. Research by Truffle Security found nearly 3,000 Google API keys embedded in client-side code for Google-related services. These exposed API keys, identified by the prefix AIza, could be used to access sensitive Gemini endpoints and private information.
The exposure of Google Cloud API keys emphasizes the importance of securing API keys and cloud infrastructure. Organizations must ensure that their API keys are properly secured and monitored to prevent unauthorized access. The use of API keys as identifiers for billing purposes can lead to unintended consequences, such as exposing sensitive data to attackers.
To mitigate this risk, organizations should implement robust security measures, including:
- Encryption: Ensure that all API keys are encrypted, both in transit and at rest.
- Access controls: Implement strict access controls, limiting access to API keys to only those who require it.
- Monitoring: Regularly monitor API key usage, detecting and responding to suspicious activity.
Additionally, organizations should consider implementing API key rotation, regularly rotating API keys to reduce the risk of unauthorized access. This can be achieved through automated processes, ensuring that API keys are updated regularly without disrupting service.
Recommendations and Takeaways
To protect against similar incidents, organizations should prioritize securing their cloud infrastructure and API keys. Implementing robust security measures, such as encryption and access controls, can help mitigate the risk of data theft. Staying informed about the latest cyber threats and vulnerabilities is crucial for protecting against AI abuse and other types of attacks.
The following recommendations are prioritized for security practitioners:
- Secure API keys and cloud infrastructure to prevent unauthorized access
- Implement robust security measures, such as encryption and access controls, to mitigate the risk of data theft
- Stay informed about the latest cyber threats and vulnerabilities to protect against AI abuse and other types of attacks
- Monitor for suspicious activity and anomalies in cloud infrastructure and API key usage
- Regularly review and update security strategies to address emerging threats, including AI abuse
- Implement API key rotation, regularly rotating API keys to reduce the risk of unauthorized access
- Ensure that systems are properly segmented, with robust access controls and monitoring in place to detect and respond to suspicious activity
By taking these steps, organizations can reduce their risk of falling victim to cyberattacks like the Mexican government hack and Google Cloud API keys exposure. As the threat landscape continues to evolve, it is essential for security practitioners to stay vigilant and adapt their strategies to address emerging threats, including AI abuse and cloud security risks.
In conclusion, the Mexican government cyberattack and Google Cloud API keys exposure are stark reminders of the importance of prioritizing cloud security and protecting against AI abuse. To ensure the security and integrity of their systems and data, organizations must:
- Apply the latest security patches and updates to their cloud infrastructure
- Implement robust access controls and monitoring to detect suspicious activity
- Regularly review and update their security strategies to address emerging threats
- Stay informed about the latest cyber threats and vulnerabilities through reputable sources, such as SecurityWeek and The Hacker News.