Introduction to Today's Threat Landscape
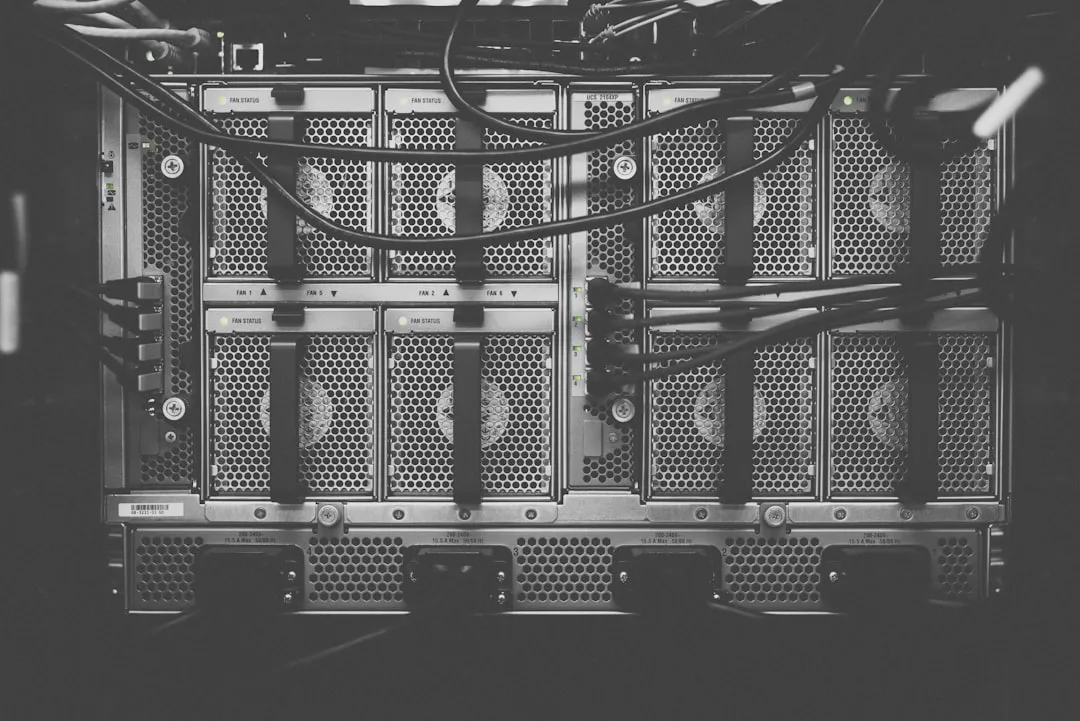
A significant escalation in threats has hit the cybersecurity landscape, with multiple critical vulnerabilities in Cisco SD-WAN systems being actively exploited by malicious actors as of February 2026, according to CISA. These exploits are occurring alongside zero-day attacks used in cyber espionage campaigns targeting governments and organizations worldwide. Furthermore, the emergence of malicious AI-generated code is increasingly being used for social engineering attacks, highlighting the evolving nature of cyber threats. The Cisco SD-WAN vulnerabilities affect various models of Cisco's software-defined wide area networking (SD-WAN) solutions, which are widely used by organizations for managing and securing their network infrastructure.
Critical Cisco SD-WAN Vulnerabilities Under Active Exploitation
The Cisco SD-WAN vulnerabilities, including CVE-2026-20127 and CVE-2022-20775, are of particular concern. CVE-2026-20127 allows for authentication bypass, enabling initial access to affected systems, while CVE-2022-20775 is used for escalating privileges after gaining initial access. As detailed in the NVD NIST database, these vulnerabilities can lead to severe consequences, including remote code execution and privilege escalation. The authentication bypass vulnerability CVE-2026-20127 exists due to improper handling of authentication requests, allowing an attacker to bypass the authentication mechanism and gain access to the system without valid credentials. On the other hand, CVE-2022-20775 is a path traversal vulnerability that could allow an authenticated local attacker to gain elevated privileges via improper access controls on commands within the application CLI.
In response to the active exploitation of these vulnerabilities, CISA has issued an emergency directive to mitigate these vulnerabilities and prevent further exploitation. The directive requires federal agencies to immediately inventory all in-scope Cisco SD-WAN systems, update them with available patches, and assess for compromise. Organizations are also advised to collect artifacts, including virtual snapshots and logs off of SD-WAN systems, to support threat hunt activities.
Zero-Day Exploits and Cyber Espionage Campaigns
The use of zero-day exploits in cyber espionage campaigns has been a significant concern. A former US defense contractor employee was jailed for selling zero-day exploits to a Russian broker, which were then used in cyber espionage campaigns targeting governments and organizations worldwide, as reported by BleepingComputer. This incident highlights the dangers of insider threats and the illicit trade of exploits. Furthermore, Google disrupted a Chinese cyber espionage campaign targeting telecoms and governments across 42 countries, demonstrating the global reach of these campaigns.
These zero-day exploits are often used in targeted attacks, where attackers use them to gain initial access to a network or system. Once inside, they can move laterally, exploiting other vulnerabilities and gathering sensitive information. The fact that zero-day exploits are being sold on the black market and used by nation-state actors underscores the importance of robust security measures, including regular patching and vulnerability management.
Malicious AI-Generated Code and Social Engineering Attacks
The emergence of malicious AI-generated code is a new frontier in cyber threats. A hacker used Anthropic's Claude chatbot to attack government agencies in Mexico, as reported by Engadget. Additionally, malicious Next.js repositories were used to target developers through fake job interviews and social engineering attacks, linked to North Korean actors, as detailed by The Hacker News. Four malicious NuGet packages were discovered, designed to steal sensitive ASP.NET data and manipulate authorization rules.
These malicious AI-generated code attacks highlight the need for developers to be cautious when using open-source repositories and to verify the authenticity of code before integrating it into their projects. Furthermore, organizations should educate their employees about the risks of social engineering attacks and provide training on how to identify and report suspicious activity.
Mitigation Guidance
To mitigate these threats, security practitioners should take the following steps:
- Immediately inventory all in-scope Cisco SD-WAN systems and update them with available patches.
- Conduct thorough threat hunts for evidence of compromise, especially focusing on signs of zero-day exploit activity.
- Implement robust security measures to prevent social engineering attacks, including education on AI-generated threats.
- Monitor for suspicious activity related to malicious AI-generated code, such as unusual network traffic or system behavior.
- Ensure that all software development and deployment processes are secure, including the use of trusted repositories and secure coding practices.
- Regularly review and update incident response plans to account for the evolving threat landscape.
- Implement a defense-in-depth approach, including firewalls, intrusion detection systems, and antivirus software.
Organizations should also consider implementing additional security controls, such as:
- Multi-factor authentication to prevent unauthorized access to systems and networks.
- Network segmentation to limit the spread of malware and unauthorized access.
- Regular vulnerability scanning and penetration testing to identify and remediate vulnerabilities.
- Security information and event management (SIEM) systems to monitor and analyze security-related data.
By taking these steps, organizations can reduce their risk of falling victim to these emerging threats and protect themselves against the evolving landscape of cyber attacks. As the threat landscape continues to evolve, it is essential for security practitioners to stay informed and adapt their defenses accordingly.
Recommendations for Cisco SD-WAN System Administrators
For administrators of Cisco SD-WAN systems, the following specific recommendations are made:
- Apply the latest security patches as soon as possible to mitigate the vulnerabilities.
- Follow CISA's guidance for mitigating the vulnerabilities and preventing further exploitation.
- Conduct regular security audits to identify and remediate any potential issues.
- Ensure that all users have strong passwords and are using multi-factor authentication.
- Monitor system logs for suspicious activity and report any incidents to the relevant authorities.
By following these recommendations, administrators of Cisco SD-WAN systems can help protect their organizations from the threats posed by these vulnerabilities and ensure the security and integrity of their networks.