Introduction to Today's Threat Landscape
A recent wave of credential-based attacks has underscored the vulnerability of authentication systems, with stolen credentials rendering even multi-factor authentication (MFA) systems ineffective according to a BleepingComputer report. This has resulted in a staggering number of organizations falling victim to such attacks. The increasing use of AI tools and browser extensions introduces new security risks, including shadow AI and unguarded extension vulnerabilities. These threats can bypass traditional security controls, creating blind spots for security teams. Organizations must be aware of these emerging threats and consider strategies to mitigate their impact.
The rise of AI-powered applications has transformed the way organizations operate, from automating tasks to enhancing customer experiences. However, this increased reliance on AI tools also introduces new security risks, such as the potential for data breaches and lateral movement within a network. Furthermore, the use of browser extensions, which are often used to enhance productivity or provide additional functionality, can also introduce vulnerabilities that can be exploited by attackers.
Emerging Threats in AI and Browser Extensions
The use of AI browser extensions poses a significant yet often overlooked threat, operating outside the visibility of security teams and potentially introducing dangerous vulnerabilities as reported by The Hacker News. Stolen credentials can turn authentication systems into an attack surface, highlighting the need for enhanced verification methods such as wearable biometric authentication. This is because traditional MFA systems can be bypassed using stolen credentials, rendering them ineffective according to a BleepingComputer report. Shadow AI introduces new security risks, including the use of unauthorized AI tools by employees without formal approval from IT and security teams as highlighted by The Hacker News. This can lead to a lack of visibility and control over AI-powered applications, creating new blind spots in what is known as shadow AI.
The use of unauthorized AI tools by employees can also lead to the introduction of malicious code or vulnerabilities into an organization's network. For example, an employee may use an AI-powered browser extension without realizing that it contains a vulnerability that can be exploited by attackers as reported by LayerX. This highlights the need for security teams to monitor and control the use of AI browser extensions within their organization. Employees should be educated on the risks associated with using unauthorized AI tools and the importance of obtaining formal approval from IT and security teams before adopting new technologies.
In addition to the risks posed by AI browser extensions, organizations must also consider the potential vulnerabilities introduced by AI-powered applications themselves. For instance, a vulnerability in an AI-powered chatbot could allow attackers to inject malicious code or steal sensitive data as demonstrated by researchers. To mitigate these risks, organizations should implement robust security controls, such as input validation and output encoding, to prevent attackers from exploiting vulnerabilities in AI-powered applications.
Technical Details of AI Browser Extensions
To understand the technical details of AI browser extensions, it is essential to examine how they operate. AI browser extensions typically use machine learning algorithms to analyze user behavior and provide personalized recommendations or automation. However, this analysis can also introduce potential vulnerabilities, such as data leakage or insecure data storage. For example, an AI browser extension may store sensitive user data, such as login credentials or credit card numbers, in an insecure manner, allowing attackers to access this data as reported by researchers.
Furthermore, AI browser extensions often rely on third-party libraries and frameworks, which can introduce additional vulnerabilities. For instance, a vulnerability in a popular machine learning library could allow attackers to inject malicious code into an AI browser extension, compromising the security of the entire system as demonstrated by researchers.
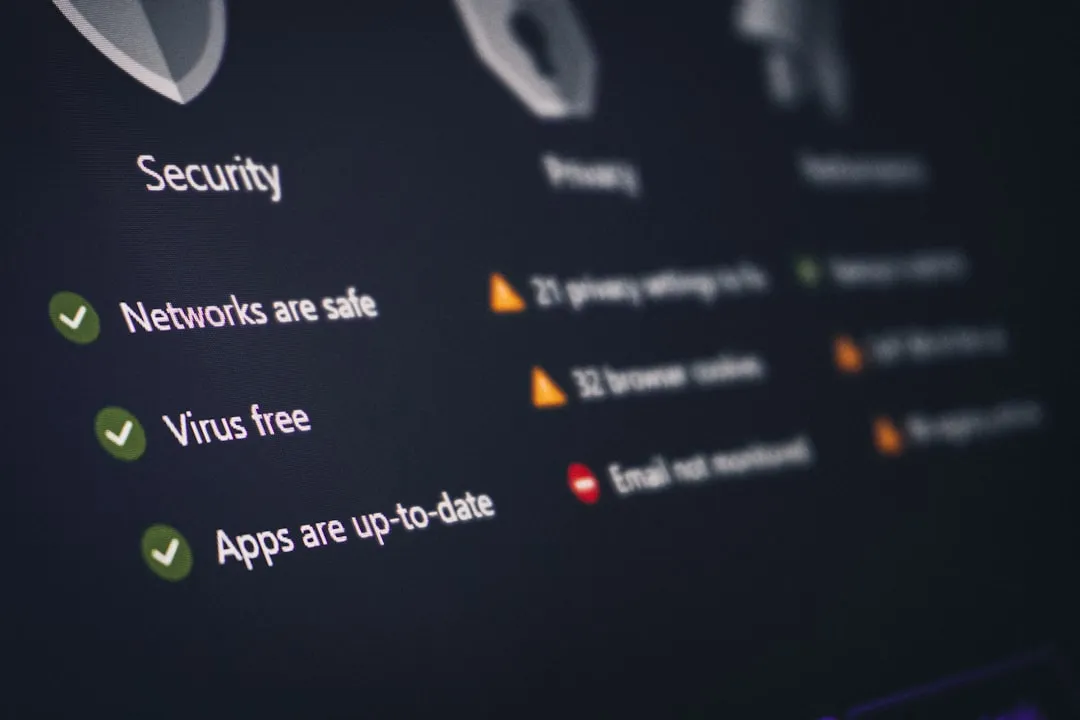
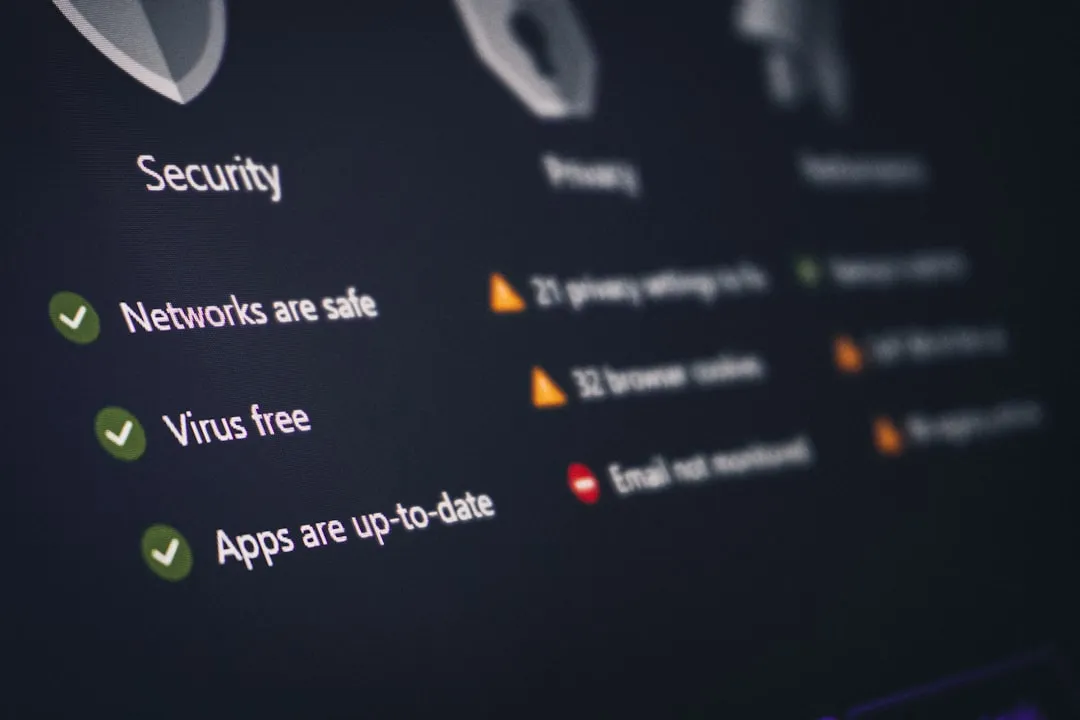
Mitigation Guidance
To mitigate the risks posed by AI browser extensions and shadow AI, organizations should implement a comprehensive security strategy that includes:
- Monitoring and control: Security teams should monitor and control the use of AI browser extensions within their organization, ensuring that only approved extensions are used.
- Education and training: Employees should be educated on the risks associated with using unauthorized AI tools and the importance of obtaining formal approval from IT and security teams before adopting new technologies.
- Robust security controls: Organizations should implement robust security controls, such as input validation and output encoding, to prevent attackers from exploiting vulnerabilities in AI-powered applications.
- Regular security audits: Organizations should conduct regular security audits to identify and address potential vulnerabilities in AI-powered applications.
- Enhanced verification methods: Organizations should implement enhanced verification methods, such as wearable biometric authentication, to prevent stolen credentials from being used to bypass security controls.
Some specific recommendations for security practitioners include:
- Implementing wearable biometric authentication to enhance verification methods
- Monitoring and controlling the use of AI browser extensions within the organization
- Providing education and training to employees on the risks associated with using unauthorized AI tools
- Implementing policies and procedures for the approval and deployment of AI-powered browser extensions
- Conducting regular security audits to identify and address potential vulnerabilities in AI-powered applications
- Using secure coding practices when developing AI-powered applications, such as input validation and output encoding
By following these recommendations, organizations can reduce the risk of emerging threats in AI and browser extensions and protect themselves against the growing threat landscape. It is essential for security teams to stay informed about the latest developments in AI security and browser extension vulnerabilities, and to take a proactive approach to mitigating these risks.
Conclusion
In conclusion, the increasing use of AI tools and browser extensions introduces new security risks, including shadow AI and unguarded extension vulnerabilities. To mitigate these risks, organizations should implement a comprehensive security strategy that includes monitoring and control, education and training, robust security controls, regular security audits, and enhanced verification methods. Key action items for organizations include:
- Implementing wearable biometric authentication within the next 6 months
- Conducting a thorough audit of all AI browser extensions in use within the organization within the next 3 months
- Providing mandatory education and training to all employees on the risks associated with using unauthorized AI tools by the end of the quarter
- Developing and enforcing policies for the approval and deployment of AI-powered browser extensions within the next 2 months By taking a proactive approach to mitigating these risks, organizations can reduce the risk of emerging threats in AI and browser extensions and protect themselves against the growing threat landscape.