Introduction to Today's Threat Landscape
The US faces a significant cybersecurity challenge as Lazarus Group's Medusa ransomware attacks and active exploitation of zero-day vulnerabilities, such as CVE-2026-25108, pose substantial threats to national security, particularly in the healthcare sector. According to The Hacker News, a former US defense contractor employee was jailed for selling zero-day exploits to a Russian broker, highlighting the risk of insider threats and the severity of these threats to national security.
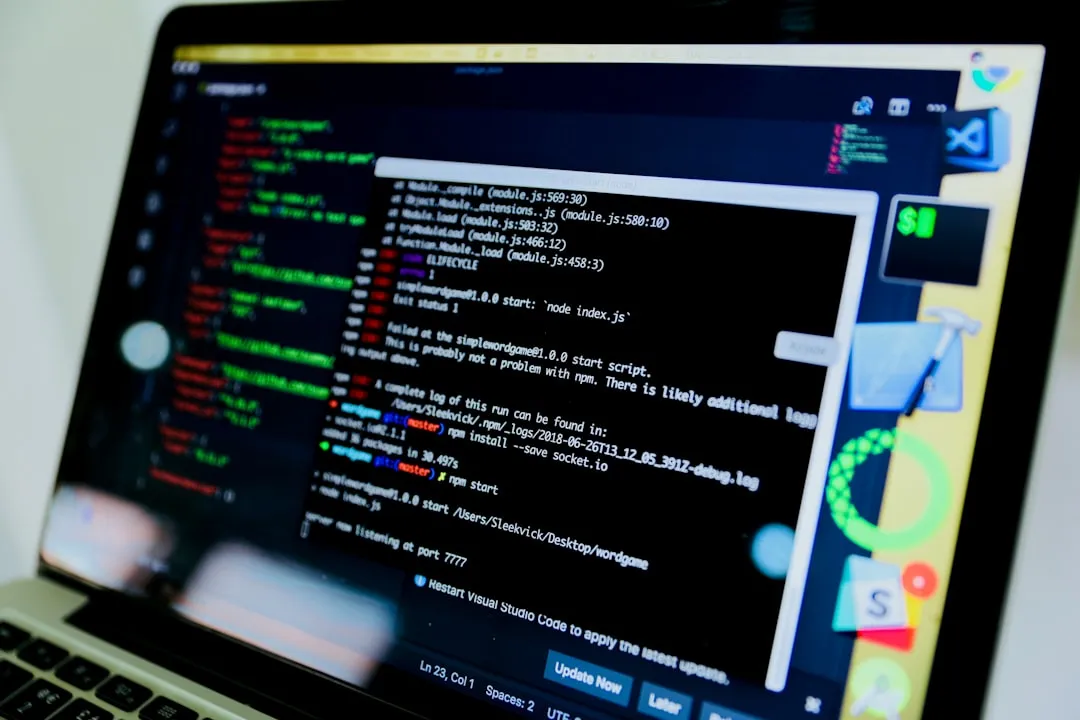
The exploitation of CVE-2026-25108, which affects FileZen with a CVSS v4 score of 8.7, allows authenticated users to execute operating system commands via command injection. This vulnerability has been added to the US Cybersecurity and Infrastructure Security Agency's (CISA) Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation, as reported by The Hacker News. The US Treasury Department has also sanctioned the Russian exploit broker for buying stolen hacking tools, further emphasizing the severity of these threats, according to Bleeping Computer.
The affected FileZen system is a widely used file management software in various industries, including healthcare, finance, and government. The vulnerability CVE-2026-25108 can be exploited by attackers to gain unauthorized access to sensitive files and data, potentially leading to data breaches and other malicious activities. To mitigate this risk, organizations must prioritize regular security updates and patches for their FileZen systems.
Active Exploitation of Zero-Day Vulnerabilities: A Critical Threat
The active exploitation of zero-day vulnerabilities poses a significant risk to national security, particularly in the healthcare sector. A former US defense contractor employee was jailed for selling zero-day exploits to a Russian broker, highlighting the risk of insider threats. The vulnerability tracked as CVE-2026-25108 affects FileZen and has a CVSS v4 score of 8.7, allowing authenticated users to execute operating system commands via command injection.
The exploitation of zero-day vulnerabilities can have devastating consequences, including unauthorized access to sensitive systems and data breaches. In the healthcare sector, this can lead to the compromise of sensitive patient data, disruption of critical services, and even loss of life. To prevent such attacks, organizations must implement robust security measures, including:
- Regular security updates and patches for all systems and software
- Implementation of intrusion detection and prevention systems (IDPS) to detect and block suspicious activity
- Conducting regular vulnerability assessments and penetration testing to identify potential weaknesses
- Implementing a robust incident response plan to quickly respond to potential threats
The US Treasury Department's sanctions against the Russian exploit broker for buying stolen hacking tools underscore the severity of these threats. According to Bleeping Computer, this incident highlights the need for international cooperation in combating cyber threats. The exploitation of zero-day vulnerabilities, such as CVE-2026-25108, can have far-reaching consequences, and it is essential for organizations to prioritize proactive measures to prevent such attacks.
Lazarus Group's Medusa Ransomware Attacks: A High-Risk Threat to Healthcare
The Lazarus Group, a North Korean state-backed hacking group, is targeting US healthcare organizations with Medusa ransomware attacks, posing a significant threat to the sector. These attacks involve the use of Medusa ransomware and other malware, such as Comebacker backdoor and Blindingcan RAT. According to The Hacker News, these attacks have been observed in both the Middle East and the US, highlighting the global reach of these threats.
The Lazarus Group's use of Medusa ransomware is particularly concerning, as it can lead to significant disruptions to healthcare services and compromise sensitive patient data. As reported by Dark Reading, the group has also leveraged other malware, such as Infohook, in its recent attacks. The targeting of US healthcare organizations by the Lazarus Group highlights the need for increased vigilance and proactive measures to prevent such attacks.
The Medusa ransomware attacks typically involve a multi-stage attack process, including:
- Initial compromise: The attackers gain initial access to the target system through phishing or other social engineering tactics.
- Lateral movement: The attackers move laterally within the network, exploiting vulnerabilities and gaining access to sensitive systems.
- Deployment of malware: The attackers deploy the Medusa ransomware and other malware, such as Comebacker backdoor and Blindingcan RAT, to encrypt files and disrupt services.
- Ransom demand: The attackers demand a ransom in exchange for the decryption key.
To prevent such attacks, healthcare organizations must implement robust security measures, including:
- Regular security updates and patches for all systems and software
- Implementation of intrusion detection and prevention systems (IDPS) to detect and block suspicious activity
- Conducting regular vulnerability assessments and penetration testing to identify potential weaknesses
- Implementing a robust incident response plan to quickly respond to potential threats
- Providing regular cybersecurity training to employees to prevent social engineering attacks
Recommendations and Takeaways: Proactive Measures Against Twin Threats
To mitigate the risks posed by zero-day exploits and ransomware attacks, organizations must prioritize proactive measures, including regular security updates and employee training. Healthcare organizations should be particularly vigilant, given the high-risk nature of these threats to their sector. The US government's sanctions against Russian exploit brokers highlight the need for international cooperation in combating cyber threats.
To prevent such attacks, security practitioners should:
- Regularly update software and systems to prevent exploitation of known vulnerabilities
- Implement robust security measures, including firewalls and intrusion detection systems
- Conduct regular employee training on cybersecurity best practices
- Monitor systems for suspicious activity and respond quickly to potential threats
- Collaborate with international partners to share threat intelligence and best practices
- Implement a robust incident response plan to quickly respond to potential threats
- Provide regular cybersecurity training to employees to prevent social engineering attacks
Additionally, organizations should consider implementing the following measures to prevent Medusa ransomware attacks:
- Implementing a robust backup and disaster recovery plan to ensure business continuity in the event of an attack
- Conducting regular vulnerability assessments and penetration testing to identify potential weaknesses
- Implementing a security information and event management (SIEM) system to detect and respond to suspicious activity
- Providing regular cybersecurity training to employees to prevent social engineering attacks
By taking these proactive measures, organizations can reduce the risk of zero-day exploits and ransomware attacks, protecting sensitive data and preventing disruptions to critical services. As the cyber threat landscape continues to evolve, it is essential for security practitioners to remain vigilant and adapt to emerging threats, prioritizing proactive measures to prevent such attacks. To start, apply the Microsoft Patch Tuesday updates released on the most recent patch day, prioritize updating FileZen systems with the latest security patches, and conduct regular employee training on cybersecurity best practices to prevent social engineering attacks.