Introduction
A sophisticated password-spraying campaign has targeted over 300 Microsoft 365 environments in Israel and the U.A.E., attributed to an Iran-linked threat actor. This ongoing threat highlights the persistent cyber threats faced by organizations in the Middle East region. As the threat landscape continues to evolve, it is imperative for organizations to prioritize robust cybersecurity measures to prevent such attacks. The campaign's focus on cloud-based services, specifically Microsoft 365 environments, underscores the need for enhanced security protocols to protect sensitive data and prevent unauthorized access.
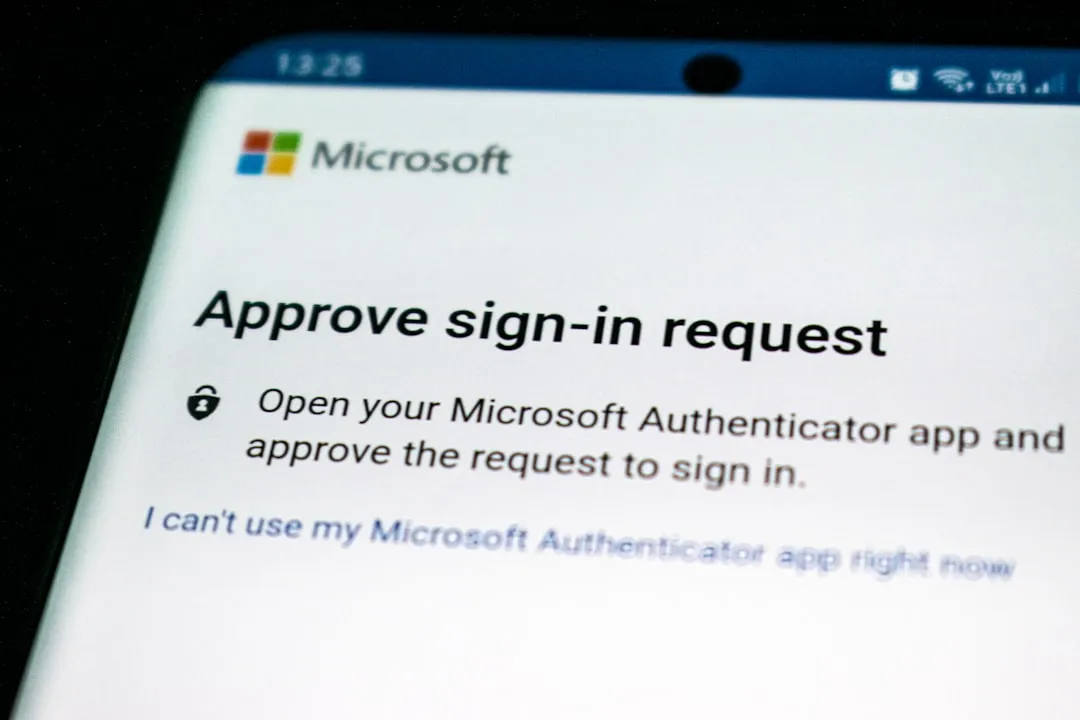
The affected systems, primarily running Microsoft 365, are vulnerable to password-spraying attacks due to weak passwords or inadequate authentication mechanisms. Attackers exploit these weaknesses by using automated tools to attempt multiple login attempts with commonly used passwords, increasing their chances of gaining unauthorized access. This technique is particularly effective against organizations that do not enforce robust password policies or multi-factor authentication.
Iran-Linked Password-Spraying Campaign Targets Microsoft 365
The Iran-linked threat actor is suspected to be behind the password-spraying campaign, which has been carried out in three distinct attack waves, with the most recent one occurring on March 23, 2026, as reported by The Hacker News. This ongoing and active threat primarily targets Microsoft 365 environments, indicating a focus on cloud-based services. The use of password-spraying tactics suggests that the attackers are attempting to exploit weak passwords or authentication mechanisms, emphasizing the importance of robust password management and authentication protocols.
According to Check Point, the campaign is primarily targeting Microsoft 365 environments in Israel and the U.A.E., with three distinct attack waves carried out on March 3, March 13, and March 23, 2026. The attackers are using a combination of techniques, including password spraying and credential stuffing, to gain unauthorized access to the targeted systems. These techniques involve attempting to log in to multiple accounts using a list of commonly used passwords or credentials obtained from previous data breaches.
The password-spraying campaign highlights the ongoing cyber threats in the Middle East region, where various threat actors are targeting organizations with sophisticated attacks. The use of password-spraying tactics is a common technique employed by attackers to exploit weak passwords or authentication mechanisms. As reported by The Hacker News, the campaign is suspected to be carried out by an Iran-linked threat actor, emphasizing the need for organizations to prioritize robust cybersecurity measures to prevent such attacks.
To better understand the scope of the attack, it's essential to examine the technical details. The attackers are using automated tools to attempt multiple login attempts with commonly used passwords. These tools can be configured to target specific systems or applications, making them highly effective against organizations that do not enforce robust password policies or multi-factor authentication. Furthermore, the use of credential stuffing techniques allows the attackers to leverage credentials obtained from previous data breaches, increasing their chances of gaining unauthorized access.
Technical Details and Mitigation Guidance
To mitigate the risk of password-spraying attacks, organizations should prioritize robust password management and authentication mechanisms. This includes implementing multi-factor authentication (MFA), which can significantly reduce the risk of password-spraying attacks. MFA requires users to provide additional forms of verification, such as a code sent to their phone or a biometric scan, in addition to their password.
Regular security audits and monitoring can also help identify potential vulnerabilities and threats, enabling organizations to take proactive measures to prevent attacks. Some key recommendations for security practitioners include:
- Implementing robust password management policies, including regular password rotations and strength checks
- Enabling multi-factor authentication (MFA) to add an additional layer of security
- Conducting regular security audits and monitoring to identify potential vulnerabilities and threats
- Prioritizing timely vulnerability remediation and robust security measures to prevent attacks
- Implementing a password spraying detection system to identify and alert on suspicious login attempts
- Providing user education and awareness training to prevent users from using weak passwords or falling victim to phishing attacks
Additionally, organizations should consider implementing conditional access policies to restrict access to sensitive systems and data. These policies can be based on various factors, such as user location, device type, or time of day, and can help prevent unauthorized access even if a password is compromised.
Recommendations for Microsoft 365 Environments
For organizations running Microsoft 365 environments, there are several specific recommendations that can help mitigate the risk of password-spraying attacks. These include:
- Enabling Azure Active Directory (AAD) conditional access to restrict access to sensitive systems and data
- Implementing Microsoft 365 security defaults to enable robust security features, such as MFA and password policies
- Configuring Azure AD identity protection to detect and respond to potential security threats
- Regularly reviewing and updating password policies to ensure they are aligned with industry best practices
- Providing user education and awareness training on the importance of strong passwords and multi-factor authentication
By prioritizing these recommendations, organizations can significantly reduce the risk of password-spraying attacks and protect their sensitive data from unauthorized access. As the threat landscape continues to evolve, it is imperative for organizations to stay vigilant and adapt their cybersecurity measures to prevent sophisticated attacks like the Iran-linked password-spraying campaign.
Conclusion
The Iran-linked password-spraying campaign targeting Microsoft 365 environments in Israel and the U.A.E. highlights the ongoing cyber threats faced by organizations in the Middle East region. To mitigate these threats, organizations must prioritize robust cybersecurity measures, including:
- Implementing robust password management and authentication mechanisms
- Conducting regular security audits and monitoring
- Prioritizing timely vulnerability remediation
- Enabling multi-factor authentication (MFA)
- Providing user education and awareness training on the importance of strong passwords and multi-factor authentication
By taking these proactive measures, organizations can ensure the security and integrity of their systems and data, protecting against the ever-present threat of cyberattacks.