Introduction
A recent wave of high-severity vulnerabilities in Cisco's Secure Firewall Management Center (FMC) software, which can give attackers root access to the system, and the takedown of the Leakbase cybercrime forum by the FBI and European law enforcement agencies, underscore the persistent threats to cybersecurity. Specifically, Cisco has released security updates to patch two maximum-severity vulnerabilities in its Secure Firewall Management Center software, as reported by BleepingComputer. Meanwhile, the Leakbase cybercrime forum, where criminals bought and sold stolen credentials and exploits, has been taken down, but new threats are emerging, including a confirmed LexisNexis data breach with hackers leaking stolen files, according to SecurityWeek. Both incidents highlight the importance of protecting sensitive information and applying security patches promptly.
The Cisco Secure Firewall Management Center is a critical component of many organizations' security infrastructure, providing centralized management and monitoring of firewall devices. The vulnerabilities in question, which affect the Cisco Secure Firewall Management Center software, can be exploited by attackers to gain root access to the system, allowing them to modify configurations, steal sensitive data, and disrupt network operations. This emphasizes the need for organizations to prioritize the application of security patches and ensure that their systems are up-to-date. As The Record notes, the FBI and European law enforcement agencies have carried out a global crackdown on the Leakbase cybercrime forum, but the emergence of new threats, such as the LexisNexis data breach, underscores the need for continued vigilance.
Cisco Secure Firewall Management Center Vulnerabilities
The vulnerabilities in Cisco's Secure Firewall Management Center software are considered high-severity due to the potential for root access, which would allow attackers to gain complete control over the system. According to BleepingComputer, Cisco has released security updates to patch these vulnerabilities, and administrators are advised to apply the patches as soon as possible to prevent potential attacks. Although Cisco has not disclosed the specific versions of the Secure Firewall Management Center software that are affected, the patches are available for download from the Cisco website. To mitigate these vulnerabilities, organizations should take the following steps:
- Immediately apply the security patches provided by Cisco to the affected systems.
- Ensure that all Cisco Secure Firewall Management Center software is updated to the latest version.
- Implement additional security measures, such as multi-factor authentication and role-based access control, to limit the potential damage in case of an attack.
- Conduct regular security audits and vulnerability assessments to identify and address any potential weaknesses in the system.
- Consider implementing a web application firewall (WAF) to provide an additional layer of protection against attacks.
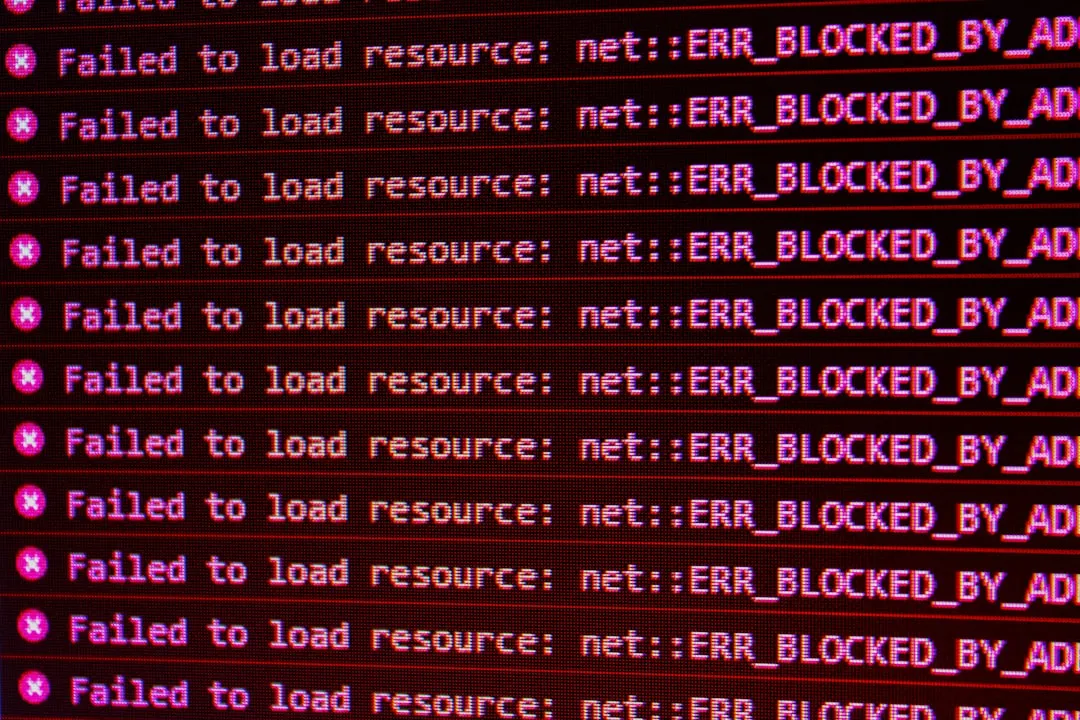
It is essential for organizations to understand that these vulnerabilities can be exploited by attackers using various techniques, including phishing and social engineering. Therefore, it is crucial to educate users about the risks and ensure that they are aware of the potential threats. Additionally, organizations should have an incident response plan in place to quickly respond to and contain any potential security incidents. As SecurityWeek notes, the LexisNexis data breach highlights the importance of protecting sensitive data and ensuring that appropriate security controls are in place to prevent such breaches.
Leakbase Cybercrime Forum Takedown and Related Threats
The takedown of the Leakbase cybercrime forum is a significant blow to cybercrime operations, but new threats are emerging. As reported by The Record, the FBI and European law enforcement agencies carried out a global crackdown on the Leakbase cybercrime forum, where criminals bought and sold stolen credentials and exploits of software vulnerabilities. However, a new LexisNexis data breach has been confirmed, with hackers leaking stolen files, including 400,000 personal information records, as reported by SecurityWeek. The breach of LexisNexis servers resulted in the access of customer and business information, highlighting the need for robust security measures. The hackers claim to have stolen 2GB of files, including sensitive information, as confirmed by BleepingComputer.
To protect against data breaches like the LexisNexis incident, organizations should consider the following measures:
- Implement robust access controls, including multi-factor authentication and role-based access control, to limit access to sensitive data.
- Use encryption to protect sensitive data both in transit and at rest.
- Conduct regular security audits and vulnerability assessments to identify and address any potential weaknesses in the system.
- Implement a incident response plan to quickly respond to and contain any potential security incidents.
- Consider implementing a security information and event management (SIEM) system to monitor and analyze security-related data from various sources.
Recommendations and Takeaways
To protect against these and similar threats, security practitioners should prioritize the following recommendations:
- Apply security patches promptly, especially for high-severity vulnerabilities like those in Cisco's Secure Firewall Management Center.
- Implement robust security measures, including multi-factor authentication and regular backups, to protect against cybercrime threats.
- Monitor for emerging threats, such as new data breaches, and be prepared to respond quickly.
- Stay informed about cybersecurity threats and best practices through reputable sources, such as BleepingComputer, SecurityWeek, and The Record.
- Consider implementing additional security controls, such as a web application firewall (WAF) and a security information and event management (SIEM) system, to provide an additional layer of protection against attacks.
- Educate users about the risks and ensure that they are aware of the potential threats, and have an incident response plan in place to quickly respond to and contain any potential security incidents.
By following these recommendations, organizations can reduce the risk of exploitation and protect their sensitive information from cyber threats. It is essential to remain vigilant and proactive in the face of evolving cybersecurity threats, and to continually assess and improve security controls to ensure the protection of critical systems and data. As the cybersecurity landscape continues to evolve, organizations must prioritize the security of their systems and data to prevent potential breaches and attacks.