Introduction to Today's Threat Landscape
A recent surge in critical vulnerabilities has exposed supply chain infrastructure to significant threats, with threat actors increasingly targeting these weaknesses to gain access to sensitive information. The discovery of over 14,000 F5 BIG-IP APM instances remaining exposed to remote code execution (RCE) attacks is a stark reminder of the risks posed by unpatched systems. Furthermore, the Claude source code leak highlights big supply chain missteps, emphasizing the need for robust security measures and timely patching to prevent such incidents.
The threat landscape is becoming increasingly complex, with malware and ransomware threats on the rise. Organizations must stay informed about emerging dangers and take proactive measures to secure their systems. Recent discoveries have highlighted the importance of supply chain risk management, with critical vulnerabilities in Progress ShareFile and Cisco IMC posing significant threats to enterprise environments.
The affected systems, including F5 BIG-IP APM, Progress ShareFile, and Cisco IMC, are widely used in various industries, making them attractive targets for threat actors. For instance, F5 BIG-IP APM is commonly used in financial institutions, government agencies, and healthcare organizations, while Progress ShareFile is used by enterprises to securely share files with partners and customers. Cisco IMC, on the other hand, is used to manage and monitor Cisco servers, making it a critical component of many organization's infrastructure.
Vulnerabilities and Supply Chain Risks
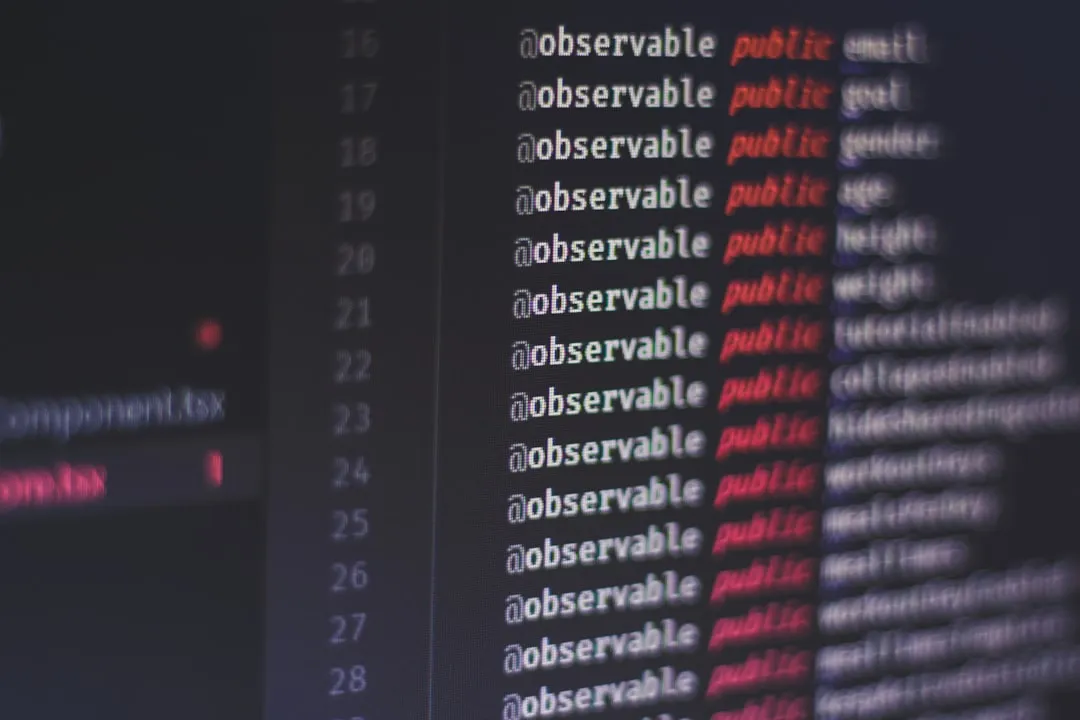
The Claude source code leak has brought attention to the lack of supply chain oversight, highlighting the need for robust security measures to prevent similar incidents. According to Dark Reading, the software supply chain should be treated as critical infrastructure with guardrails built in at every layer. This incident emphasizes the importance of secure coding practices and timely patching to prevent vulnerabilities from being exploited.
New Progress ShareFile flaws can be chained in pre-auth RCE attacks, posing a significant threat to enterprise environments. As reported by Bleeping Computer, two vulnerabilities in Progress ShareFile can enable unauthenticated file exfiltration from affected environments. This highlights the need for organizations to prioritize robust security measures, including secure coding practices and regular updates.
A critical Cisco IMC auth bypass vulnerability gives attackers Admin access, underscoring the importance of timely patching. According to Bleeping Computer, Cisco has patched several critical and high-severity vulnerabilities, including an Integrated Management Controller (IMC) authentication bypass that enables attackers to gain Admin access. This vulnerability poses a significant threat to organizations using affected Cisco products, emphasizing the need for regular updates and secure configuration.
To mitigate these risks, organizations should prioritize the following security measures:
- Implement secure coding practices to prevent vulnerabilities in software development
- Conduct regular security audits and risk assessments to identify potential weaknesses
- Apply patches and updates in a timely manner to prevent exploitation of known vulnerabilities
- Use secure protocols for communication, such as HTTPS and SFTP, to protect data in transit
- Limit access to sensitive systems and data using role-based access control and least privilege principles
Targeted Attacks and Threat Actor Activity
China-linked TA416 targets European governments with PlugX and OAuth-based phishing, indicating a surge in targeted attacks. As reported by The Hacker News, the campaign has been attributed to TA416, a cluster of activity that overlaps with DarkPeony, RedDelta, Red Lich, SmugX, UNC6384, and Vertigo Panda. This highlights the complex threat landscape faced by organizations, with multiple threat actor groups involved in targeted attacks.
The blast radius of TeamPCP attacks expands amid hacker infighting, creating a complex threat landscape for organizations. According to Dark Reading, as organizations disclose breaches tied to TeamPCP's supply chain attacks, ShinyHunters and Lapsus$ are getting involved, taking credit, and creating a murky situation for enterprises. This emphasizes the need for organizations to stay informed about emerging threats and take proactive measures to secure their systems.
To mitigate the risks of targeted attacks, organizations should:
- Implement advanced threat detection and response capabilities, such as endpoint detection and response (EDR) and security information and event management (SIEM) systems
- Conduct regular security awareness training for employees to prevent social engineering attacks
- Use multi-factor authentication (MFA) to prevent unauthorized access to sensitive systems and data
- Monitor for suspicious activity and anomalies in network traffic and system logs
- Develop incident response plans to quickly respond to potential security incidents
Recommendations and Takeaways
To mitigate supply chain risks, organizations should prioritize robust security measures, including:
- Timely patching of vulnerable systems
- Secure coding practices to prevent vulnerabilities
- Thorough risk assessments and vendor vetting to identify potential weaknesses
- Regular updates and secure configuration of critical infrastructure
- Advanced threat detection and response capabilities
- Security awareness training for employees
- Multi-factor authentication (MFA) to prevent unauthorized access
Staying informed about emerging threats and vulnerabilities is crucial for maintaining a strong security posture. Organizations should:
- Monitor reputable sources for information on new vulnerabilities and threats
- Participate in industry-wide initiatives to share threat intelligence and best practices
- Develop incident response plans to quickly respond to potential security incidents
- Conduct regular security audits and risk assessments to identify potential weaknesses
- Use secure protocols for communication, such as HTTPS and SFTP, to protect data in transit
By taking proactive measures to secure their systems and staying informed about emerging threats, organizations can reduce the risk of supply chain attacks and protect their sensitive information. As the threat landscape continues to evolve, it is essential for organizations to remain vigilant and adapt their security strategies to address new challenges.
In addition to these recommendations, organizations should also consider implementing a comprehensive supply chain risk management program, which includes:
- Identifying and assessing potential risks in the supply chain
- Implementing controls to mitigate identified risks
- Monitoring and reviewing the effectiveness of controls
- Continuously updating and improving the supply chain risk management program
To prioritize actions, organizations should focus on the following key steps:
- Conduct a thorough risk assessment to identify potential vulnerabilities in their supply chain.
- Implement secure coding practices to prevent vulnerabilities in software development.
- Apply patches and updates in a timely manner to prevent exploitation of known vulnerabilities.
- Develop an incident response plan to quickly respond to potential security incidents.
- Provide regular security awareness training for employees to prevent social engineering attacks.
By following these guidelines and staying informed about emerging threats, organizations can effectively manage supply chain risks and protect their sensitive information.