Articles tagged: vulnerabilities
19 articles found

Critical Infrastructure Under Siege
Vulnerabilities in critical infrastructure pose significant risks, with ShareFile flaws and Hitachi Energy's Ellipse product under attack. Emerging threats like CrystalRAT malware and Casbaneiro bank trojan also threaten security. Learn about the key threats and how to protect yourself.
Critical Cyberattacks Hit Mercor, Bitcoin
Mercor faces a cyberattack tied to the LiteLLM project compromise, while quantum computer researchers predict Bitcoin encryption can be broken in a few years. Ukraine also warns of Russian hackers revisiting past breaches.

Supply Chain Risks Surge Amid Critical Vulnerabilities
Critical vulnerabilities in supply chain infrastructure pose significant threats to organizations. Recent discoveries highlight the need for robust security measures and timely patching.
AI-Driven Code Surge Redefines AppSec
The surge in AI-driven code is forcing a rethink of application security practices, with evolving threats and new vulnerabilities emerging. Learn how to evaluate AI SOC agents and adapt to the changing AppSec landscape.
Critical Flaws Exposed in Anritsu, Cisco, and Telegram
Multiple high-severity vulnerabilities have been discovered in Anritsu Remote Spectrum Monitor, Cisco source code, and a critical no-click flaw in Telegram. These threats pose significant risks to communications, defense, and emergency services. Understanding these vulnerabilities is crucial for proactive defense.

Critical Infrastructure Under Siege
Critical infrastructure faces significant threats from vulnerabilities, ransomware, and nation-state attacks. Recent discoveries include Honeywell IQ4x BMS Controller and Apeman Cameras vulnerabilities, as well as new malware and threat actor activity. Learn how to protect your systems.
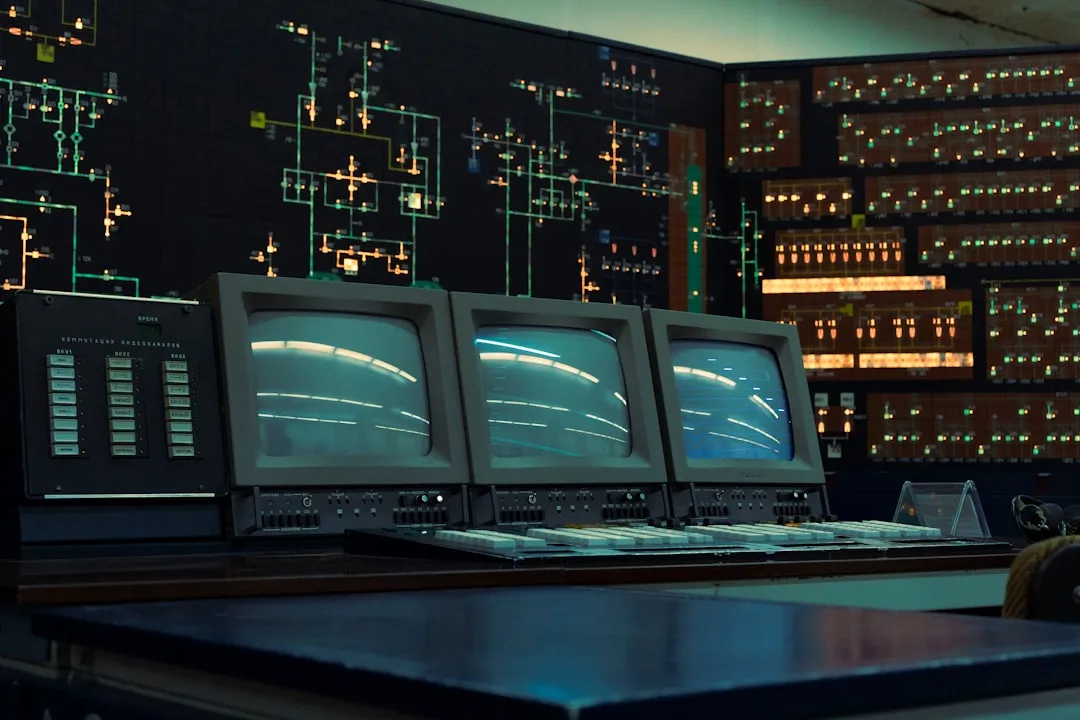
Critical Infrastructure Under Siege
Critical infrastructure faces multiple threats, including vulnerabilities in industrial control systems, the KadNap malware targeting routers, and emerging AI-powered attacks. Organizations must prioritize patching, securing networks, and implementing robust cybersecurity strategies to protect against these threats.
Google Looker Studio Vulnerabilities Exposed
High-severity vulnerabilities in Google Looker Studio and malicious Chrome extensions pose significant threats, while evolving malware and new security platforms highlight the cat-and-mouse game in cybersecurity. Learn about the latest developments and how to protect yourself.

State-Sponsored Threats and Vulnerabilities Plague Cybersecurity
State-sponsored threat actors and vulnerabilities pose significant risks to cybersecurity. Chinese state hackers target telcos, while vulnerabilities in Avira antivirus and WordPress plugins are exploited. Learn about the key threats and how to protect yourself.

Multiple Product Vulnerabilities Expose Users to Attacks
Recent security incidents and vulnerabilities in Hikvision, Rockwell, and Apple products, as well as a self-propagating JavaScript worm on Wikipedia, pose significant threats to users. These vulnerabilities could allow attackers to escalate privileges, gain access to sensitive information, and execute arbitrary code. It is essential for users to stay informed and take necessary precautions to protect themselves.
Cisco Firewall Vulnerabilities and Leakbase Takedown
Cisco has released patches for high-severity vulnerabilities in its Secure Firewall Management Center, while the FBI and European law enforcement agencies have taken down the Leakbase cybercrime forum. Learn about the key threats and recommendations for protection.

Critical Flaws in Juniper Routers and Windows 11
New vulnerabilities have been discovered in Juniper Networks PTX routers and Windows 11, posing a significant threat to cybersecurity. These flaws can be exploited by attackers to gain remote access and execute malicious code. It is essential to patch these vulnerabilities immediately to prevent potential attacks.

Critical Vulnerabilities and Malicious Campaigns Targeting Multiple Sectors
Newly disclosed vulnerabilities in software and hardware, along with malicious campaigns targeting specific sectors, pose significant threats to cybersecurity. Readers should be aware of these risks and take necessary precautions to protect themselves.

Industrial Control System Vulnerabilities Pose Critical Threats
Recent vulnerabilities in industrial control systems highlight the need for ongoing security maintenance and updates. Cybersecurity research emphasizes the importance of awareness and best practices to ensure business continuity.
Critical Infrastructure Under Fire
Johnson Controls Frick Controls Quantum HD vulnerabilities pose a high risk to critical infrastructure, while the Aeternum botnet loader emerges as a new threat. Learn about these emerging threats and how to protect against them.
Targeted Attacks Hit Developers and Critical Infrastructure
Sophisticated threat actors are targeting developers and critical infrastructure with malicious repositories, backdoors, and vulnerabilities. Stay ahead of the threats with our analysis and recommendations.
Emerging Threats Accelerate Network Breaches
Newly discovered vulnerabilities, including Spectre-like exploits and critical Serv-U flaws, are accelerating network breaches. Organizations must stay informed to ensure timely mitigation.

Industrial Control System Vulnerabilities Pose Significant Risks
The Cybersecurity and Infrastructure Security Agency (CISA) has warned of vulnerabilities in InSAT MasterSCADA and Schneider Electric EcoStruxure Building Operation products, which could allow remote code execution and unauthorized access to sensitive data. These vulnerabilities pose significant risks to critical infrastructure sectors, including energy, water, and transportation systems.

SolarWinds & FortiGate Under Attack
Critical vulnerabilities in SolarWinds and FortiGate pose significant risks, while recent ransomware attacks and newly disclosed threats demand immediate attention from security teams. Learn about the key threats and how to protect your organization.