Articles tagged: cybersecurity
34 articles found
Marimo & Chrome Under Attack
Critical vulnerabilities in Marimo and Chrome pose significant risks to users, with exploits already reported in the wild. Learn about the technical details and implications of these threats.

Ransomware Hits Healthcare
A recent ransomware attack on Dutch healthcare software vendor ChipSoft highlights the vulnerability of healthcare organizations to such attacks, which can have significant consequences for patient care. This article explores the key facts and implications of this threat. Ransomware attacks are a growing concern for healthcare.

Data Breaches Expose Sensitive Info, $3.6M Stolen
Recent data breaches have exposed sensitive information and resulted in significant financial losses, highlighting the need for robust cybersecurity measures. This article provides an overview of the latest threats and offers recommendations for protection.

Emerging Threats: Emoji-Based Attacks and Patched Vulnerabilities
Threat actors are using emojis to evade detection, while cybercriminals target accountants to drain Russian firms' bank accounts. Meanwhile, Palo Alto Networks and SonicWall have patched high-severity vulnerabilities. Learn about these emerging threats and how to protect yourself.
Zero-Day Exploits Hit Adobe Reader & WordPress
Critical zero-day vulnerabilities in Adobe Reader and WordPress are being actively exploited, posing significant risks to users and organizations. These exploits require immediate attention to prevent malicious attacks.
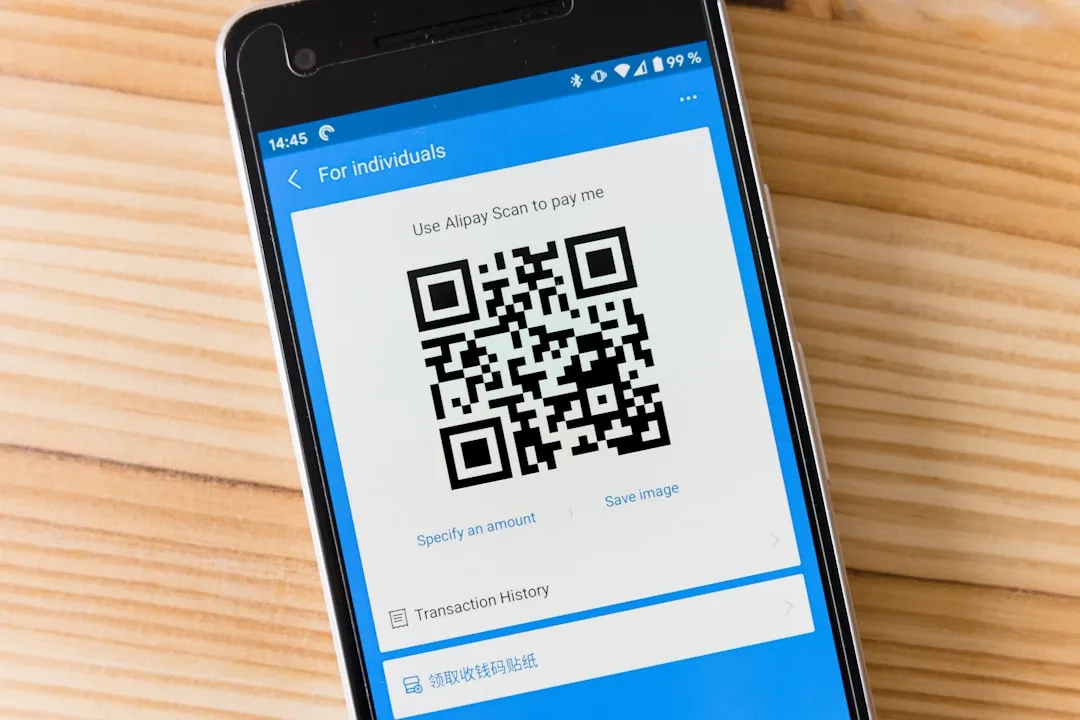
Phishing Attacks Surge with QR Codes and Device Code Abuse
A new wave of phishing attacks using QR codes and device code abuse is targeting users, stealing personal and financial information. Learn about the surge in these attacks and how to protect yourself.
CVE-2025-55182 Exploited to Steal Sensitive Data
Cybersecurity experts warn of active exploitation of CVE-2025-55182, a critical vulnerability that can be used to steal sensitive data and gain unauthorized access to systems. This large-scale credential harvesting operation has affected 766 Next.js hosts, highlighting the need for prompt patching and security updates.
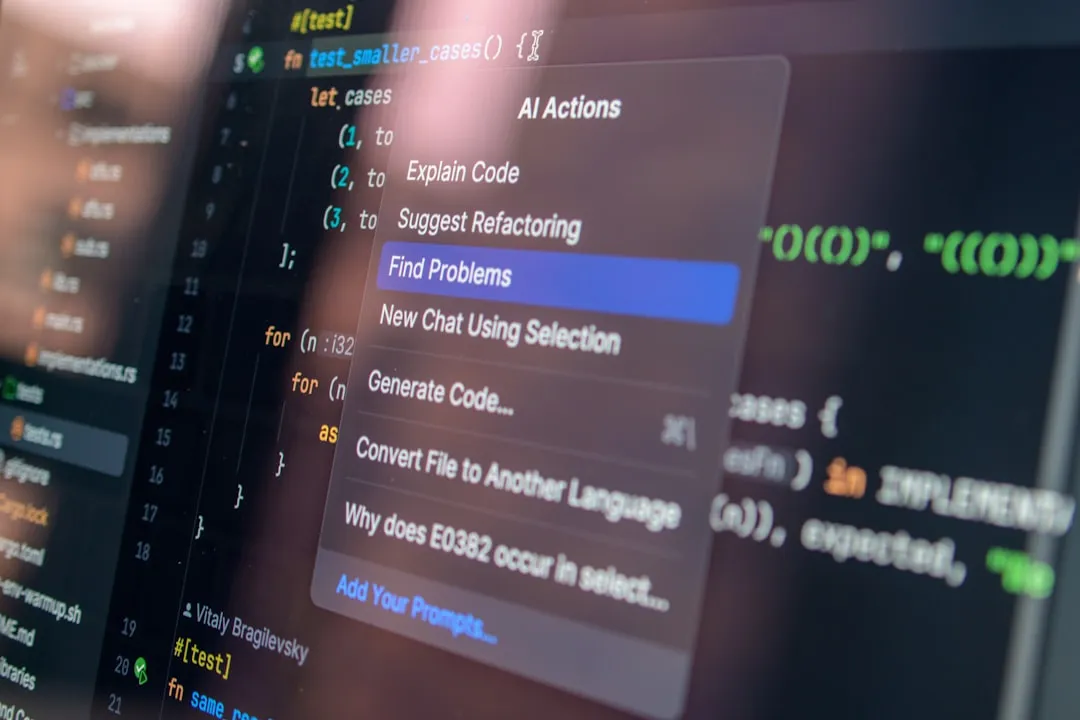
AI-Driven Code Surge Redefines AppSec
The surge in AI-driven code is forcing a rethink of application security practices, with evolving threats and new vulnerabilities emerging. Learn how to evaluate AI SOC agents and adapt to the changing AppSec landscape.

FreeBSD Forums Hacked Amidst Rising Security Concerns
The FreeBSD Forums were hacked, highlighting the need for robust security measures on online forums. This incident serves as a reminder to monitor and respond to security incidents. Learn more about this breach and its implications.

Ransomware and Crypto Exchange Hacks Surge
A surge in ransomware claims and crypto exchange hacks poses a significant threat to cybersecurity. Over 7,655 ransomware claims were reported in the past year, while a hacker stole $53 million from the Uranium crypto exchange. Learn how to protect yourself from these threats.

Italian Bank Fined $36M for Data Protection Failures
The Italian Data Protection Authority has fined Intesa Sanpaolo SpA $36 million for data protection failures, highlighting the importance of adequate technical and organizational measures to protect personal data. This incident emphasizes the need for robust security measures to prevent similar breaches.

AI-Powered Phishing on the Rise
Emerging threats in cybersecurity include AI-powered phishing campaigns and new attack techniques from SANS Institute's top 5 most dangerous threats. These sophisticated attacks can evade traditional security controls, posing significant risks to individuals and organizations. Staying informed is crucial to mitigating these threats.
Phishing Attacks Surge with OAuth Abuse
Recent phishing campaigns have targeted Microsoft accounts, including a successful attack on the Dutch National Police. Threat actors are using Bubble AI app builder to evade detection and leveraging OAuth abuse techniques.

Critical Data Breaches Hit Stryker and Telus Digital
Iranian hacktivists have struck medical device maker Stryker, while a hacker claims to have stolen nearly 1 petabyte of data from Telus Digital, highlighting the need for robust cybersecurity measures and incident response plans.
Critical n8n Flaws, KadNap Botnet, and Android Malware Threats
Today's threat landscape includes critical n8n workflow automation flaws, the KadNap botnet infecting edge devices, and new Android malware families targeting banking apps. These threats pose significant risks to security and require immediate attention.

HPE Aruba Networking AOS-CX Vulnerabilities Patched
HPE has patched multiple security vulnerabilities in the Aruba Networking AOS-CX operating system, including authentication and code execution issues. Users should apply the patches to prevent potential exploitation. No known active exploitation has been reported.
Critical Infrastructure Under Siege
Critical infrastructure faces multiple threats, including vulnerabilities in industrial control systems, the KadNap malware targeting routers, and emerging AI-powered attacks. Organizations must prioritize patching, securing networks, and implementing robust cybersecurity strategies to protect against these threats.
Google Looker Studio Vulnerabilities Exposed
High-severity vulnerabilities in Google Looker Studio and malicious Chrome extensions pose significant threats, while evolving malware and new security platforms highlight the cat-and-mouse game in cybersecurity. Learn about the latest developments and how to protect yourself.
Critical Infrastructure Under Siege
A Chinese threat actor is targeting critical infrastructure in Asia, exploiting web servers and using Mimikatz. The campaign has targeted multiple sectors, including aviation, energy, and government, highlighting the need for increased security measures.

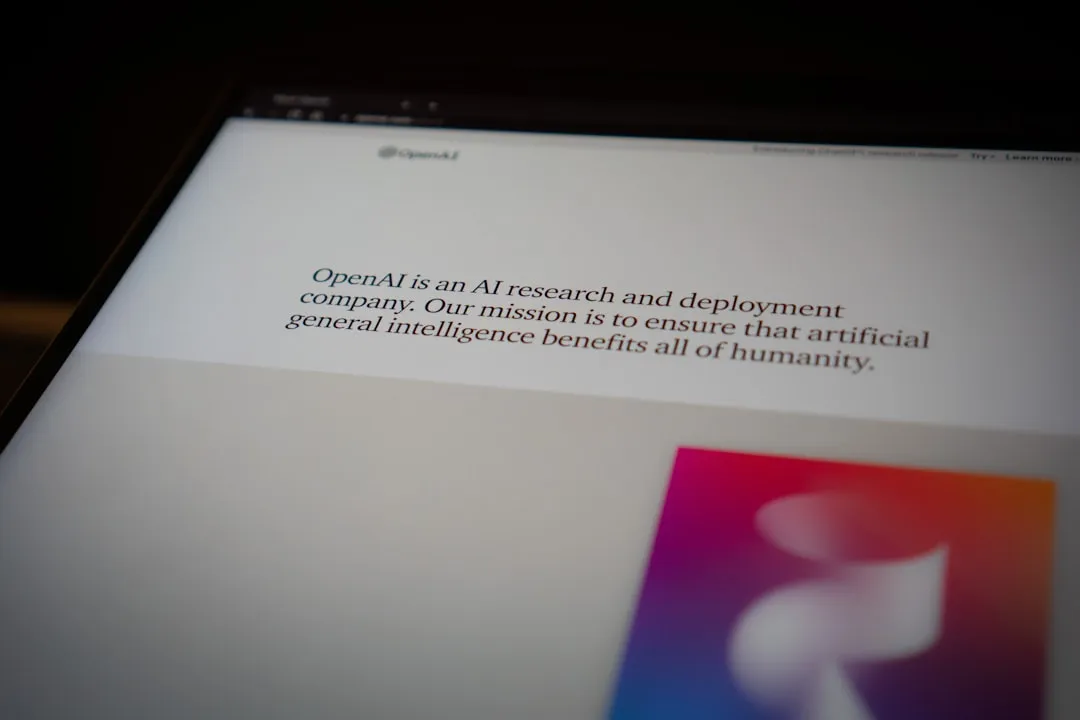
AI-Driven Cyber Threats Escalate
Microsoft reports hackers are abusing AI in cyberattacks, while OpenAI's Codex Security and Anthropic's AI model identify thousands of vulnerabilities. Learn how AI is changing the cybersecurity landscape and what you can do to protect yourself.

Hackers Abuse .arpa Domain and IPv6 to Evade Phishing Defenses
Threat actors are using the .arpa domain and IPv6 reverse DNS to bypass traditional security controls in phishing campaigns. This new evasion technique poses a significant threat to organizations, highlighting the need for improved defenses. Learn how to protect your organization from these sophisticated attacks.

Zero-Day Exploits Target iOS and GitHub Users
Critical zero-day vulnerabilities are being actively exploited, targeting iOS users and GitHub repositories. Over 100 GitHub repositories are distributing the BoryptGrab stealer, while CISA has added iOS flaws from the Coruna exploit kit to the KEV list. Users must take immediate action to protect themselves.

AI-Driven Threats Intensify Nation-State Attacks
Nation-state actors are leveraging AI-powered tools to launch sophisticated cyberattacks, targeting governments and organizations worldwide. Recent campaigns by Transparent Tribe and Iranian APT hackers demonstrate the growing threat of AI-driven attacks. Stay informed on the latest threats and learn how to protect your organization.

Phishing and Cybercrime Surge
A recent surge in phishing and cybercrime activities has highlighted the vulnerability of IoT devices and the importance of robust security measures. The hacking of the MyFirst Kids Watch and the bust of the Tycoon 2FA phishing platform underscore the need for increased vigilance. Read on to learn more about these threats and how to protect yourself.
Phishing Operations Takedown and Cybercrime Syndicates Disrupted
Law enforcement agencies and threat hunters have made significant strides in disrupting major phishing operations and cybercrime syndicates, resulting in the takedown of Tycoon 2FA and LeakBase forum. These efforts highlight the importance of collaboration in combating cybercrime. Read on to learn more about these successes and their impact on the threat landscape.

Silver Dragon Targets Governments
An advanced persistent threat group known as Silver Dragon has been linked to cyber attacks targeting entities in Europe and Southeast Asia. The group's tactics include exploiting public-facing internet servers and delivering phishing emails with malicious attachments. Organizations must prioritize security to stay informed about emerging threats.

AI-Powered Cyberattacks Escalate
Recent cyberattacks have leveraged AI to weaponize code, create deepfakes, and inject malicious data. Enterprises must invest in advanced security measures to stay ahead of emerging threats.

Cisco SD-WAN Zero-Day Exploited, Devs Targeted, ICS Vulnerabilities Found
A critical Cisco SD-WAN zero-day is being exploited, while developers are being targeted by malicious campaigns and industrial control systems are vulnerable to new threats. Learn how to protect yourself and your organization from these emerging threats.

Cisco SD-WAN Zero-Day Under Active Exploitation
A critical zero-day vulnerability in Cisco SD-WAN has been exploited since 2023, allowing attackers to bypass authentication and gain administrative access. Meanwhile, a data breach at European DIY chain ManoMano has affected 38 million customers, highlighting the importance of securing third-party services and patching vulnerabilities.
Critical Charging Infrastructure Vulnerabilities and Cisco SD-WAN Zero-Day Exploit
Multiple critical vulnerabilities have been discovered in charging infrastructure systems, while a zero-day exploit has been found in Cisco SD-WAN. These threats highlight the importance of patching and keeping software up to date to prevent large-scale denial of service, privilege escalation, and corruption of data.

Critical Vulnerabilities and Malicious Campaigns Targeting Multiple Sectors
Newly disclosed vulnerabilities in software and hardware, along with malicious campaigns targeting specific sectors, pose significant threats to cybersecurity. Readers should be aware of these risks and take necessary precautions to protect themselves.
Critical Cisco SD-WAN Vulnerabilities Exploited
Multiple critical vulnerabilities in Cisco SD-WAN products are being exploited, allowing attackers to gain admin access and potentially disrupt critical infrastructure. Ransomware attacks are also on the rise, with a recent surge in attack numbers despite decreased payments.
Ransomware Payments Plummet Amidst Rising Attacks
Despite a surge in ransomware attacks, payments to threat actors have reached an all-time low. Recent incidents include the breach of Olympique Marseille and a lawsuit against SonicWall. Learn about the evolving landscape of ransomware threats and how to defend against them.

CarGurus Breach & Zero-Day Sales Rock Cybersecurity
A massive data breach at CarGurus exposed 12.4 million accounts, while a former defense contractor employee was jailed for selling zero-days to a Russian broker. Learn about these critical threats and how to protect yourself.