Articles tagged: industrial-control-systems
9 articles found

Critical Infrastructure Under Siege
Targeted attacks on critical infrastructure are escalating, with Juniper Networks patching dozens of vulnerabilities and Russia's APT28 spying on global organizations. Learn about the key threats and how to protect your systems.
Cloud Resilience Under Fire
The Middle East conflict exposes significant cloud resilience gaps, while major vendors release critical ICS patches. Learn how to protect your infrastructure from emerging threats.
Critical Infrastructure Under Siege
Critical infrastructure faces multiple threats, including vulnerabilities in industrial control systems, the KadNap malware targeting routers, and emerging AI-powered attacks. Organizations must prioritize patching, securing networks, and implementing robust cybersecurity strategies to protect against these threats.

MyFirst Kids Watch Hacked Amidst Rising Cyber Threats
The MyFirst Kids Watch has been hacked, allowing access to its camera and microphone. This incident is part of a larger landscape of cyber threats, including fake Claude Code install guides, Iran's cyber-kinetic war doctrine, and vulnerabilities in Rockwell industrial control systems. These threats underscore the importance of cybersecurity in protecting sensitive information and physical assets.

Cisco SD-WAN Zero-Day Exploited, Devs Targeted, ICS Vulnerabilities Found
A critical Cisco SD-WAN zero-day is being exploited, while developers are being targeted by malicious campaigns and industrial control systems are vulnerable to new threats. Learn how to protect yourself and your organization from these emerging threats.
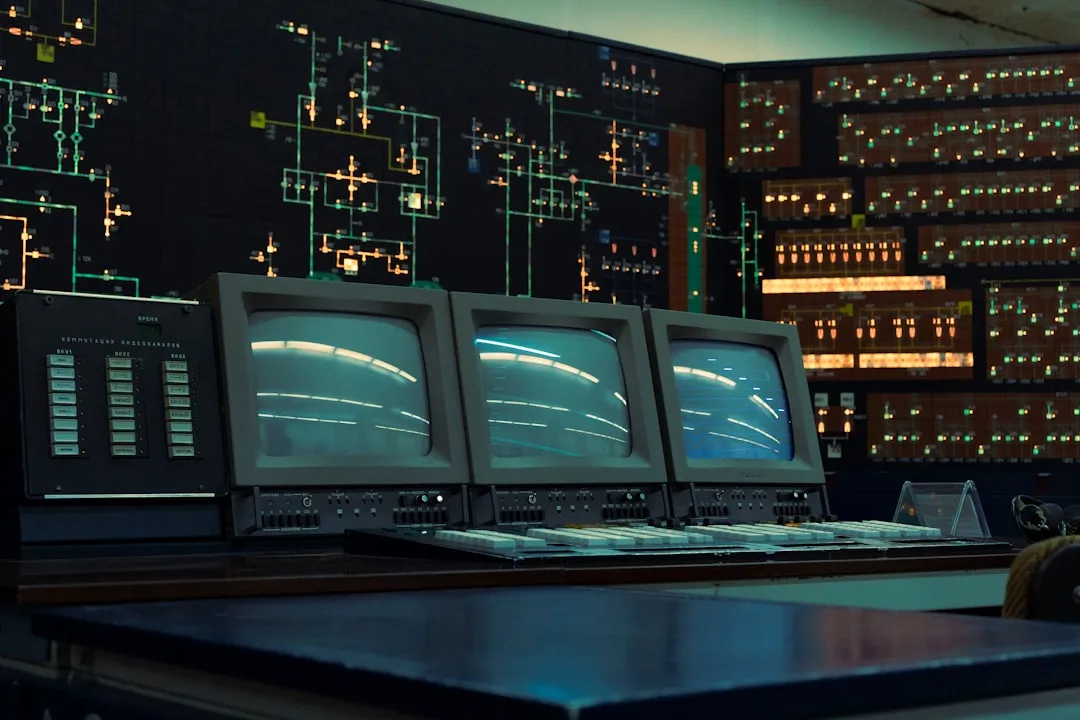
Critical Industrial Control System Vulnerabilities Under Active Exploitation
Multiple vulnerabilities in Yokogawa Centum and Exaopc products are under active exploitation, allowing attackers to gain control of industrial control systems. Cisco IOS and IOS XE software patches are also available to prevent further exploitation. Immediate action is required to patch these vulnerabilities.

Industrial Control System Vulnerabilities Pose Critical Threats
Recent vulnerabilities in industrial control systems highlight the need for ongoing security maintenance and updates. Cybersecurity research emphasizes the importance of awareness and best practices to ensure business continuity.

Industrial Control System Vulnerabilities Pose Significant Risks
The Cybersecurity and Infrastructure Security Agency (CISA) has warned of vulnerabilities in InSAT MasterSCADA and Schneider Electric EcoStruxure Building Operation products, which could allow remote code execution and unauthorized access to sensitive data. These vulnerabilities pose significant risks to critical infrastructure sectors, including energy, water, and transportation systems.

Industrial Control Systems Under Siege
Critical vulnerabilities in industrial control systems pose significant risks, while malicious activities target developers and supply chains with fake job interviews and social engineering attacks. Learn about the key threats and how to protect against them.