Articles tagged: phishing
27 articles found
High-Profile Targets Under Siege
Russia's Fancy Bear APT group, a new VENOM phishing platform, and suspected Indian government-backed threat actors are targeting high-profile individuals and organizations. These attacks highlight the importance of patching and implementing zero-trust security measures to protect against sophisticated threats.
Cyber Fraud Surges as Fortinet Releases Emergency Patch
A critical FortiClient EMS flaw is being exploited, and cyber fraud has surged to $17.6 billion in losses. Learn about the latest threats and how to protect yourself.
Phishing Attacks Surge with QR Codes and Device Code Abuse
A new wave of phishing attacks using QR codes and device code abuse is targeting users, stealing personal and financial information. Learn about the surge in these attacks and how to protect yourself.

Zero-Day Exploits Hit TrueConf Servers and Banking Systems
Hackers exploit zero-day vulnerability in TrueConf conference servers to push malicious updates, while a phishing campaign targets Latin America and Europe with Windows banking trojans like Casbaneiro. These attacks highlight the ongoing threat of zero-day exploits and social engineering.

New Malware Threats Emerge
A surge in new malware threats has been detected, including CrystalRAT, AGEWHEEZE, and AtlasCross RAT. These threats pose a significant risk to individuals and organizations, with capabilities such as remote access, data theft, and keylogging.
Google's Quantum-Safe Deadline Looms Amid Rising Threats
As Google sets a 2029 deadline for quantum-safe cryptography migration, OpenAI launches a bug bounty program to identify abuse and safety risks in its AI systems. Meanwhile, emerging threats from compromised IP cameras, AitM phishing pages, and malicious VS Code extensions pose significant security concerns.

iOS Under Siege
A high-severity targeted email campaign is leveraging the DarkSword exploit kit to target iOS devices, attributed to Russian state-sponsored threat group TA446. Organizations must be aware of the potential for targeted attacks on their mobile devices and keep software up-to-date.

AI-Powered Phishing on the Rise
Emerging threats in cybersecurity include AI-powered phishing campaigns and new attack techniques from SANS Institute's top 5 most dangerous threats. These sophisticated attacks can evade traditional security controls, posing significant risks to individuals and organizations. Staying informed is crucial to mitigating these threats.
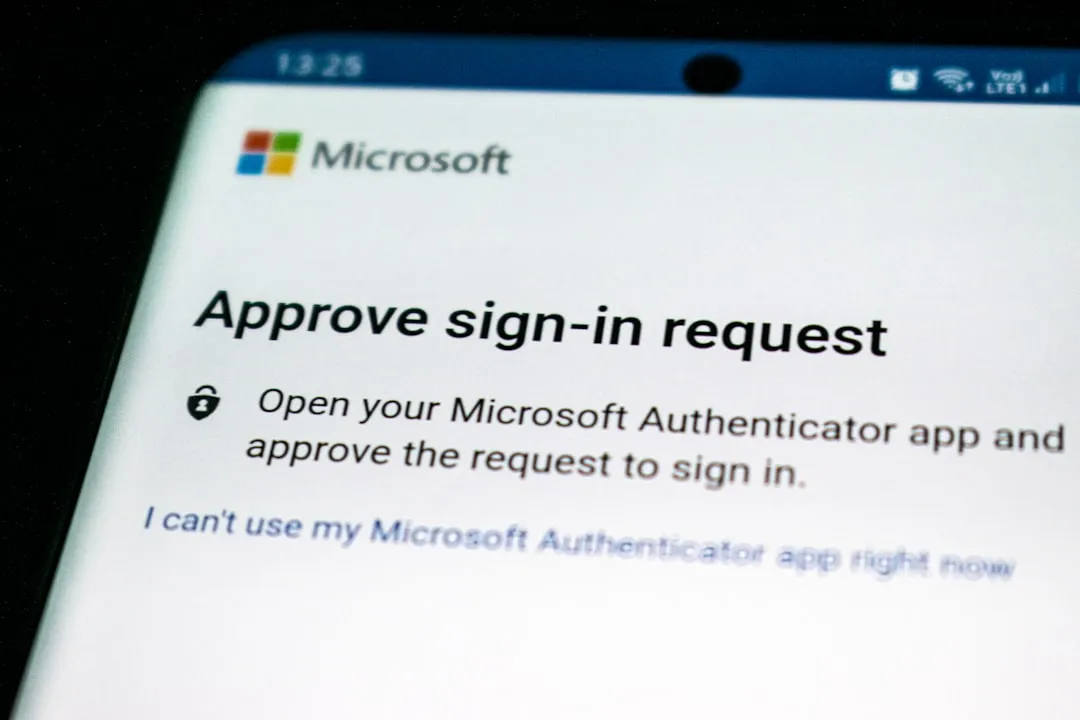
Phishing Attacks Surge with OAuth Abuse
Recent phishing campaigns have targeted Microsoft accounts, including a successful attack on the Dutch National Police. Threat actors are using Bubble AI app builder to evade detection and leveraging OAuth abuse techniques.
TikTok Phishing & Ajax Hack Expose Social Engineering Risks
A new TikTok phishing campaign and the Ajax football club hack highlight social engineering threats, while a critical PTC Windchill vulnerability requires immediate patching. Learn about these risks and how to protect yourself.

Cloud Vulnerabilities Under Siege
Hackers are exploiting cloud and software vulnerabilities at an alarming rate, with high-value organizations in Asia being targeted. Malicious code and phishing campaigns are also on the rise, highlighting the need for rapid patching and vigilance. Adobe has patched 80 vulnerabilities across eight products, and cybercriminals are impersonating city officials to steal permit payments.

Phishing Attacks Surge
Russian state-sponsored hackers are targeting government officials and journalists with Signal and WhatsApp phishing campaigns, while threat actors abuse .arpa DNS and IPv6 to evade defenses. Financial and healthcare organizations are also being targeted with Microsoft Teams phishing and A0Backdoor malware.

ClickFix Ransomware and Russian Cyber Campaigns
ClickFix attack and Termite ransomware pose high severity threats, while Russian cyber campaigns target Signal and WhatsApp. Emerging threats include abuse of internet infrastructure and custom malware. Stay informed to protect against these evolving cyber threats.

Phishing Attacks Surge with New Tactics
Phishing attacks are on the rise with new tactics, including abusing .arpa DNS and IPv6 reverse DNS. Data breaches and cybersecurity strategy updates are also in focus. Learn about the latest threats and how to protect yourself.

Hackers Abuse .arpa Domain and IPv6 to Evade Phishing Defenses
Threat actors are using the .arpa domain and IPv6 reverse DNS to bypass traditional security controls in phishing campaigns. This new evasion technique poses a significant threat to organizations, highlighting the need for improved defenses. Learn how to protect your organization from these sophisticated attacks.

State-Sponsored Threats and Vulnerabilities Plague Cybersecurity
State-sponsored threat actors and vulnerabilities pose significant risks to cybersecurity. Chinese state hackers target telcos, while vulnerabilities in Avira antivirus and WordPress plugins are exploited. Learn about the key threats and how to protect yourself.

Phishing and Cybercrime Surge
A recent surge in phishing and cybercrime activities has highlighted the vulnerability of IoT devices and the importance of robust security measures. The hacking of the MyFirst Kids Watch and the bust of the Tycoon 2FA phishing platform underscore the need for increased vigilance. Read on to learn more about these threats and how to protect yourself.
Phishing Operations Takedown and Cybercrime Syndicates Disrupted
Law enforcement agencies and threat hunters have made significant strides in disrupting major phishing operations and cybercrime syndicates, resulting in the takedown of Tycoon 2FA and LeakBase forum. These efforts highlight the importance of collaboration in combating cybercrime. Read on to learn more about these successes and their impact on the threat landscape.

Phishing Sites Slip Past Google Safe Browsing
Recent reports reveal Google Safe Browsing misses 84% of confirmed phishing sites, while the 2026 Browser Data report exposes major enterprise security blind spots. These findings highlight the need for improved detection capabilities and ongoing security research to combat emerging threats.

Zero-Days and Cybercrime: Emerging Threats
A possible US government iPhone-hacking toolkit has been leaked, while half of 2025's exploited zero-days targeted enterprises. Meanwhile, law enforcement efforts have led to the dismantling of a major phishing platform and the breakup of an African cybercrime syndicate.
Hacktivist Surge and Cybercrime Disruption
A surge in hacktivist and nation-state attacks has hit organizations worldwide, while law enforcement actions disrupt major phishing and cybercrime platforms. Learn about the key threats and how to protect yourself.

Silver Dragon Targets Governments
An advanced persistent threat group known as Silver Dragon has been linked to cyber attacks targeting entities in Europe and Southeast Asia. The group's tactics include exploiting public-facing internet servers and delivering phishing emails with malicious attachments. Organizations must prioritize security to stay informed about emerging threats.

New Surveillance Threats Emerge
Researchers uncover methods to track cars via tire sensors, while Microsoft warns of OAuth redirect abuse and a new attack hijacks OpenClaw instances. These emerging threats highlight the need for increased security measures.

Iranian Cyberattacks Disrupt Cloud Services Amidst Rising Phishing Threats
Iranian cyberattacks have hit Amazon data centers, disrupting cloud services. Meanwhile, phishing campaigns and emerging threats like quantum decryption of RSA pose significant risks. Learn about the latest cybersecurity threats and how to protect yourself.
Phishing Campaign Targets Google Users
A sophisticated phishing campaign is using a fake Google security site to steal credentials and MFA codes. Meanwhile, Samsung settles over smart TV data collection, and Claude AI experiences a worldwide outage. Learn about these threats and how to protect yourself.

Cisco SD-WAN Zero-Day Exploited, AI Threats Rise
Critical Cisco SD-WAN vulnerabilities are under active exploitation, while malicious AI-related activities and targeted attacks on critical infrastructure pose significant threats to global security. Learn about the key risks and how to protect your organization.
Ransomware Attacks Surge
A surge in ransomware attacks targets healthcare organizations, while a medical device maker discloses a data breach and phishing campaigns hit freight companies. Learn about the key threats and how to protect yourself.