Articles tagged: remote-code-execution
22 articles found
Marimo & Chrome Under Attack
Critical vulnerabilities in Marimo and Chrome pose significant risks to users, with exploits already reported in the wild. Learn about the technical details and implications of these threats.
Zero-Day Threats Hit Adobe and WordPress
Critical zero-day vulnerabilities are being exploited in Adobe Reader and the Ninja Forms File Uploads premium add-on for WordPress, posing significant risks to various industries. These threats allow hackers to execute remote code and compromise systems using malicious PDF documents and arbitrary file uploads.
WordPress & Grafana Under Attack
Hackers target Ninja Forms vulnerability to takeover WordPress sites, while GrafanaGhost attackers leak enterprise data through AI components. Learn how to protect your sites and data from these emerging threats.

Zero-Day Attacks Surge with Medusa Ransomware
A surge in zero-day exploitation is facilitating high-velocity Medusa ransomware attacks, while the Storm-1175 threat actor targets vulnerable systems. Thousands of zero-day flaws have been discovered across major systems, and a maximum-severity vulnerability in Flowise is being exploited for remote code execution.

Zero-Day Vulnerabilities Under Active Exploitation
Multiple zero-day vulnerabilities are being actively exploited, including a critical flaw in Ivanti Endpoint Manager Mobile and 13-year-old bugs in Apache ActiveMQ Classic and Flowise. These vulnerabilities pose significant risks to federal enterprises and other organizations.

Critical Infrastructure Under Siege
Vulnerabilities in critical infrastructure pose significant risks, with ShareFile flaws and Hitachi Energy's Ellipse product under attack. Emerging threats like CrystalRAT malware and Casbaneiro bank trojan also threaten security. Learn about the key threats and how to protect yourself.
Critical Vulnerabilities Under Active Exploitation
Active exploitation of critical vulnerabilities in FreeBSD and F5 BIG-IP APM instances poses a significant threat to systems. Over 14,000 F5 BIG-IP APM instances remain exposed to RCE attacks, while a full FreeBSD remote kernel RCE with root shell has been disclosed.
Citrix & F5 Under Attack
Critical vulnerabilities in Citrix NetScaler and F5 BIG-IP are being exploited, allowing attackers to gain administrative access and deploy webshells. Organizations using these products must patch immediately to prevent attacks.

Critical Exploits Hit Fortinet & F5 BIG-IP
Organizations face significant threats as critical vulnerabilities in Fortinet's FortiClient EMS and F5 BIG-IP are being actively exploited, potentially leading to remote code execution or denial-of-service conditions. Immediate action is required to patch these flaws.

F5 BIG-IP Vulnerability and Emerging Threats
A newly disclosed vulnerability in F5 BIG-IP could allow remote code execution, while security research highlights various emerging threats. Learn about the key findings and how to protect your systems.
TikTok Phishing & Ajax Hack Expose Social Engineering Risks
A new TikTok phishing campaign and the Ajax football club hack highlight social engineering threats, while a critical PTC Windchill vulnerability requires immediate patching. Learn about these risks and how to protect yourself.
CISA Orders Patching of Actively Exploited n8n Vulnerability
CISA has ordered federal agencies to patch the actively exploited n8n vulnerability, indicating a significant threat to government systems. The vulnerability allows for remote code execution, making it a high-priority patch for affected systems. Prompt patching is essential to prevent exploitation and protect against potential attacks.
Critical n8n Flaws, KadNap Botnet, and Android Malware Threats
Today's threat landscape includes critical n8n workflow automation flaws, the KadNap botnet infecting edge devices, and new Android malware families targeting banking apps. These threats pose significant risks to security and require immediate attention.

Critical Supply Chain Attacks Hit Veeam and Cloud Environments
Supply chain attacks and data breaches are on the rise, with Veeam Software patching critical flaws in its Backup & Replication solution and a threat actor breaching a cloud environment in 72 hours. Learn about the key threats and how to protect your organization.
VMware Aria Operations RCE Flaw Under Active Exploitation
A critical VMware Aria Operations vulnerability is being exploited in attacks, allowing for remote code execution. This poses a significant threat to affected systems, and immediate action is required to patch the flaw. The US Cybersecurity and Infrastructure Security Agency has added the vulnerability to its Known Exploited Vulnerabilities catalog.

Critical Flaws in Juniper Routers and Windows 11
New vulnerabilities have been discovered in Juniper Networks PTX routers and Windows 11, posing a significant threat to cybersecurity. These flaws can be exploited by attackers to gain remote access and execute malicious code. It is essential to patch these vulnerabilities immediately to prevent potential attacks.

Industrial Control System Vulnerabilities Pose Significant Risks
The Cybersecurity and Infrastructure Security Agency (CISA) has warned of vulnerabilities in InSAT MasterSCADA and Schneider Electric EcoStruxure Building Operation products, which could allow remote code execution and unauthorized access to sensitive data. These vulnerabilities pose significant risks to critical infrastructure sectors, including energy, water, and transportation systems.

Industrial Control Systems Under Siege
Critical vulnerabilities in industrial control systems pose significant risks, while malicious activities target developers and supply chains with fake job interviews and social engineering attacks. Learn about the key threats and how to protect against them.

Critical Vulnerabilities Exposed in Trend Micro, Juniper, and Zyxel Products
Newly disclosed vulnerabilities in Trend Micro, Juniper Networks, and Zyxel products pose significant risks to users. ICS and energy sector vulnerabilities are also highlighted, emphasizing the need for urgent patches and security measures.

Critical Cisco and Zyxel Vulnerabilities Under Attack
Multiple critical vulnerabilities in Cisco SD-WAN and Zyxel routers are being actively exploited, posing significant risks to organizations. Learn about the threats and how to protect your networks.

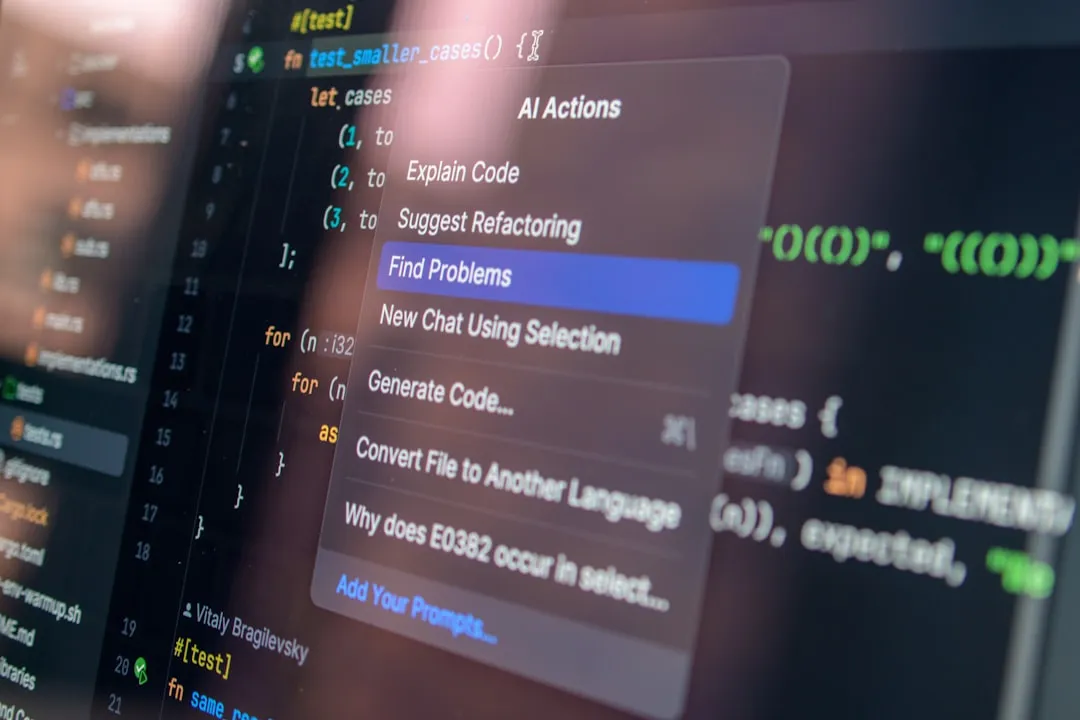
Critical Software Vulnerabilities Pose High Risk
Newly discovered vulnerabilities in popular software pose a significant threat to users, with potential for remote code execution and root access. Recent research also highlights the speed at which attackers can own a network using credential misuse and AI tools.

Data Breaches, Extortion, and Code Execution Flaws
Multiple high-severity data breaches and extortion attempts have been reported, alongside critical vulnerabilities in software that could allow for remote code execution. These threats pose significant risks to organizations and individuals alike, highlighting the need for robust security measures.